Unfortunately, as services like Office 365 become more prevalent so too do the attacks against them. These attacks are going to target people who are the least IT savvy.
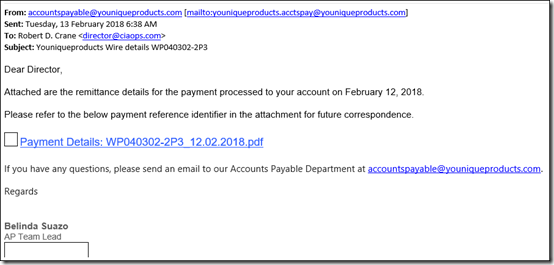
The above is the first example of an email I received this morning. Being close to Valentine’s Day it would be easy for an ordinary user to click on the link provided inside to download the PDF of their order.
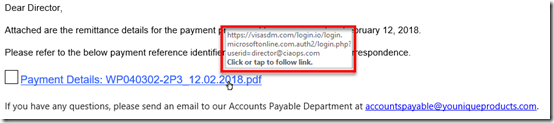
However, if you mouse over that link, you see that it actually re-directs you to a malicious web site, but of course a user isn’t going to know that.
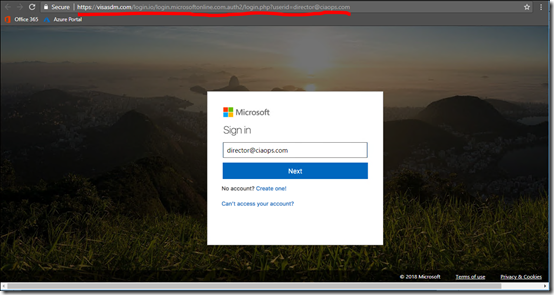
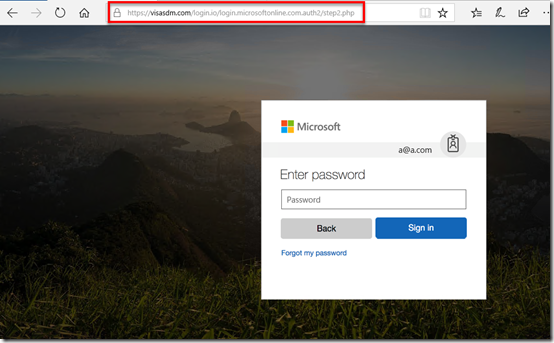
I gotta say that the malicious web site really does look an Office 365 login page doesn’t it? The only obvious give away is the URL at the top of the page.

Upon closer inspection you see that it is in fact not going to the Office 365 login URL which is:
You’ll also note that the email address is already in the dialog box so all a user would need to do is press enter as they normally would.
At the next page they are prompted for their email address. again, very, very authentic looking Office 365 login page.
Typically, the user would enter their password and hit enter. At this point their login details have been sent to the bad guys and the user is redirected to correct Office 365 login page. The user of course, thinks they entered something wrong and go through the process again. However, their account has now been compromised, pretty much without them realising.
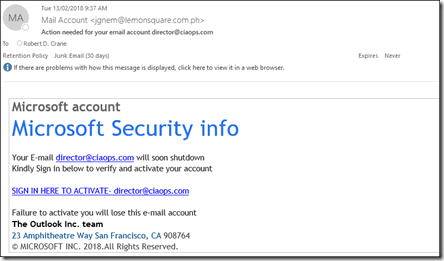
Here is the next phishing email that I received moments after getting the first. This one appears to be directly from Microsoft request an update to the security of the Office 365 account.
This prays on the underlying fear most users have of technology in order to get them to click the link.
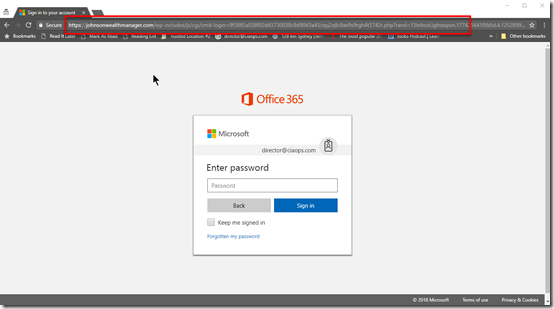
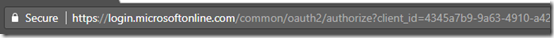
If they do so, they are again taken to another ‘official’ looking Office 365 login page as you see above.
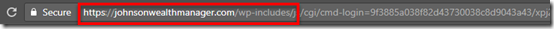
Again, this one has a non Office 365 login URL as shown above. Like the previous case, this site has it’s own certificate (HTTPS) making it appear even more legitimate.
So if you come across these sites, first course of action is to report them to Microsoft.
Submit spam, non-spam and phishing scam messages to Microsoft for Analysis
Because these types of attacks are new into the wild they are typically not picked up by reputation based systems. Eventually they picked up, like in the browser here:
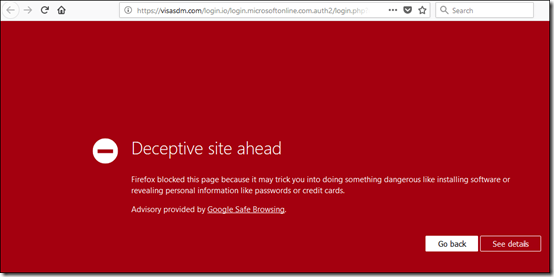
but until they are, there really isn’t much that can be done.
I’ve said this before, security is tough:
The bad guys keep winning
and technology can’t be used to solve every issue. We need to couple that with education to help people ask the right question before potentially doing the wrong thing.
if something in your inbox doesn’t seem right, chances are it isn’t. So treat it with caution.


