I’m sure there are many of us out there that continue to provide free unpaid support for our family members. Well, many it isn’t so much free, as a ‘barter’ arrangement in that every time I’m on site I get fed. That type of compensation may of course vary in your particular situation but many IT Pros are expected to support our own family as they use technology. That can be extremely challenging if you don’t do it right. Thanks to the tools available in the Microsoft Cloud, you can quite easily!
One of the benefit of doing security right for your family is that it is going to drastically reduce the amount of support calls you receive. So here’s some of the stuff I do:
1. Everyone has Microsoft 365 Business
This one license ensures that they have commercial grade email and the latest version of Office on their desktops. It ensures that they have both Safe Links and Safe Attachments for their mailboxes to protect against inbound malware and viruses.
2. Everyone runs the latest version of Windows 10 Professional on their desktop
Windows Home has lots of limitations and does not allow connection to Azure AD. Thus, all machines are Windows 10 Professional and all machines update automatically.
3. All machines are joined to Azure AD
I don’t want to have a traditional on premises domain controller to manage these Window 10 machine. By joining all the Windows 10 Professional workstations directly to Azure AD I get the management, security and control that I want all from the cloud.
4. All machines have Intune compliance and configuration policies applied

Thanks to Intune, which is part of Microsoft 365 Business, at a glance I can ensure all the machines, including my own, are compliant and configured appropriately.
5. All machines only use Windows Defender as their AV
Windows Defender is the best solution for AV in my experience. I can manage many settings thanks to Intune, although I would like some more I would admit, but I have never had an viruses or malware issues wince ditching third party AV providers a number of years ago. I am considering potentially upgrading to Windows Defender ATP but it is probably not worth the investment given the other steps I am already taking.
6. All machines are covered by Azure AD Premium P1
Azure AD Premium P1 is an add on to Microsoft 365 Business but has a number of very, very handy security features that I use to keep everyone safe.
7. Conditional access is limiting access to devices via IP address
One of the features that Azure AD Premium P1 provides is the ability to set conditional access policies. I have restricted access to my parents logins to be ONLY available on two unique IP addresses, theirs and mine. This means that if they were phished and gave up their logins a remote user would be prevented from logging in thanks to these conditional access policies as they are not connecting from these allowed IP addresses.
In my own personal cases, I also use conditional access policies but I have them set a little broader, typically limited to allowing access just from Australia. If I travel, I need to temporarily adjust the policy to accommodate where I’ll be and then set it back to just Australia when I return.
8. All POP and IMAP access has been disabled to all mailboxes

The most common way that random bad actors on the Internet are trying to gain access to accounts is using IMAP and POP3 as you can see from a recent log above. Conversely, all Microsoft 365 mailboxes have both POP3 and IMAP enabled for all mailboxes by default unfortunately. No user needs to access mail via old protocols and thus it is disabled across the tenant.
9. Basic authentication has been disabled on the tenant
Because I have modern devices and software connecting to my information, as I have said before:
Disable basic auth to improve Office 365 security
‘nuff said.
10. All accounts have Multi Factor enabled
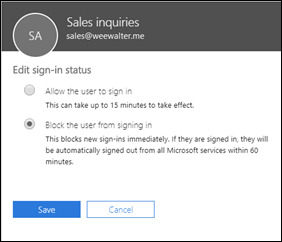
All accounts have the requirement for MFA on them. Now, my parents don’t have smart phones or devices other than their PC’s, so how do they access their accounts using MFA? Well, they actually don’t! See item 11 as to how I achieve this.
11. Trusted IPs have been enabled
Once again, thanks to magic of Azure AD Premium P1, I am able to implement Trusted IPs. This means that when a login request comes from a configured Trusted IP the user will not be prompted for MFA even if the account requires it. Thus, thanks to the locations I have already set up with Conditional Access I can also use these same IP addresses to configure Trusted IPs for my parents logins. This means, that their accounts ARE protected by MFA but since they are always logging in from a single IP address that is now trusted, they WON’T be asked for MFA. This, makes it easy on them and hard on the bad guys.
12. I have Office 365 Cloud App Discovery
Again, thanks to the wonders of Azure AD P1 I have Cloud App Discovery which enables me a far more granular logging of events in my tenant. I can see exactly what my parents are actually doing.
I’ve talked about the benefits of Cloud App Security before:
A great security add on for Microsoft 365
and recommend you have it.
13. All machines use password-less Windows Hello logins
All the machines are using Windows Hello, either biometric or a PIN to access the machines. No complex passwords to remember, just a simple PIN number or just sitting in front of the machine now gives my parents access to their desktops. It couldn’t be easier and yet secure.
There are a lot more actions I take on my production tenant to ensure it is secure but the above items are the ones that most affect and protect my parents and their information. As you can see, via the implementation of Microsoft Cloud technologies I have made it both super secure and super easy for them. In most cases they don’t even realise what I’ve done, and that’s the way it should be.
Now, if I can do this for my parents, why are you not doing the same for your business users? Eh?