A common problem that many businesses have is securely sharing their Office 365 resources, like a SharePoint Team site, with users outside their organisation quickly and easily.
Microsoft have added a great new feature called Azure AD B2B sharing that greatly simplifies making Office 365 resources like a SharePoint Online Team Site available to users who are not part of the same Office 365 tenant.
There will be typically two types of external users who reside outside an Office 365 tenant:
1. Those with an existing Azure AD account thanks to being an user of a Microsoft commercial product such as Office 365
or
2. Those without an existing Azure AD account
Here is the typical process for sharing an Office 365 Team Site with both an external Office 365 user (i.e. already has Azure AD) and an external user who just has an email address (i.e. doesn’t have Azure AD).

In this case I want to share the above Test site (https://tenantname.sharepoint.com/sites/test) with two external users. The Office 365 user will be admin@ciaops365.com and the standard user will be aston.martin@supercarhelp.com.
The Azure AD B2B process does not allow you to use consumer domains like @hotmail.com, @outlook.com, @gmail.com, etc. Youcan only use custom domains.
The first thing I need to do is ensure that the Team Site I want to share has been enabled for external sharing.
You do this by navigating to the SharePoint admin center after logging into the Office 365 portal as an administrator.

You select the site collection in question (here https://tenantname.sharepoint.com/sites/test/) and then select the Sharing button on the Ribbon Menu.

This will reveal a dialog box like that is shown above. Ensure either Allow external users who accept sharing invitations and sign in as authenticated users or Allow both external users who accept sharing invitations and anonymous guest links is selected an save any changes made.

You should then return to the Office 365 admin center and create a new security group for these external users to reside in. You do this via the Groups option on the left hand side of the Office admin center.

When you create a new Office 365 security group using the portal you must add at least one member to that group. In this case the group was created with a single member and then immediately afterwards the group was edited and that initial user was removed. The end result here is a new Office 365 security group called Externals that contains no members.

You now need to return to the SharePoint Online Team Site and assign the appropriate permissions to this new security group. In this case the whole Team Site will be shared with any member of the security group Externals and they will be permitted Edit rights as shown above (i.e. they will basically have ‘Member’ rights on that site).

You’ll then need to run PowerShell and connect to the Office 365 tenant you wish to share. I have detailed how to do that previously here:
Configuring PowerShell Access in Office 365
I also have an online course available that covers the material in more depth:
PowerShell for Office 365
Once you have connected to the tenant you’ll need to the command:
get-msolgroup | fl displayname, objectid
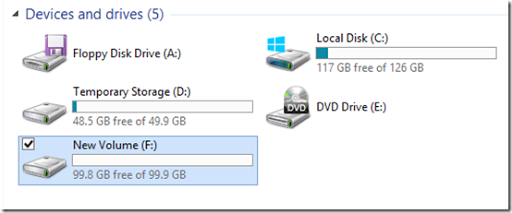
This will return a list of Office 365 security groups as shown above. You then need to record the ObjectId for the security group you just created that will contain the external users (here Externals).
You will then need to visit:
https://azure.microsoft.com/en-us/documentation/articles/active-directory-b2b-collaboration-overview/#csv-file-format
and obtain the format for the CSV import file that is required.

Into the CSV file you enter the following information into the columns:
Email = users email address
Display Name = Firstname Lastname
InviteReplyURL = SharePoint Team Site being shared (here https://tenantname.sharepoint.com/sites/test/)
InviteAppresources = leave blank
InvitegroupResources = ObjectID obtained from PowerShell step
InviteContactUsURL = A contact URL. Here just my normal web site.
Once each user you desire to have access to the SharePoint site has been entered in its own row, save the CSV file.
You’ll then need to access the Azure AD for the tenant. If you haven’t yet enabled this see my blog post:
Enabling your Office 365 Azure AD
or my online course:
Integrating Azure Active Directory Features with Office 365

You’ll then need to navigate to the users area of you Office 365 Azure AD as shown above.


You’ll then need to select the Add User button at the bottom of the page.

In the dialog window that appears you’ll need to select the Users in partner companies option in the Type of User field. You’ll also need to specify the location of the CSV file to upload with the users to be provisioned that you just created.
When this is complete, select the check mark button in the lower right.

The import process will now run. When complete you will receive a status message at the bottom of the Azure management console as shown above. You can select the option to view the report to verify there are no errors.

If you do view the report and everything has worked as expected the status should say Email generation started as shown above for the external user and

and Directory invite operation finished for the Office 365 user.

Each user should then receive an email like the one above with a link to access the shared application at anytime.

The first time that the non-Office 365 user clicks on the link they will be taken to an Application Invite page as shown above.
(Side note – if you are wondering how the image on the left of the Application Invite page has been customised, see my my online course:
Integrating Azure Active Directory Features with Office 365
)

You should see that the email address has already been entered. All the user needs to do is select the Accept button.

Since this user doesn’t have an existing Azure AD account they need to create a new one. They will therefore be prompted to complete a password as well as confirm their name and country.
When this is complete select the Sign up button to continue.

It will take a few moments for the new Azure AD account to be created

The user will then need to login with their email address and the password just entered.

Then they will have access to the shared SharePoint site as shown above.
If they select the link in the email again, they will taken to a standard Office 365 login page where they need to again use their email address and password to access the site.

Now if the Office 365 external user clicks on their received email link they will be taken to a similar Application Invite page as shown before. Simply select the Accept button to proceed.

Because the Office 365 external user already has an Azure AD account they do not need to establish a password, they are instead taken to their own tenant login page as shown above.

But once they login they are automatically taken to the destination shared SharePoint Team Site just like the previous user.

If you return and view the securities of the SharePoint Team Site as an administrator you should see the Office 365 security group created previously as shown above.

If you then view the Office 365 security group from the Office 365 admin center you should see the two users as shown above.
So now both users can simply select the link in their email to return to the shared Team Site at any point in the future.

If the non-Office 365 user attempts to access Office 365 via the standard URL (i.e. https://login.microsoftonline.com) they can login and when they do they see the above screen.

If they select the App Launcher in the top left they see the above tiles.

If they then select the Admin tile they are basically stepped through the process of verifying their own domain and creating a full office 365 account. Some guerilla marketing there maybe?
What I have shown here is only what is possible with SharePoint but as the recent video from Microsoft Mechanics highlights you can use a similar process to share apps from the Windows Azure Single Sign On Apps portal that is also part of Office 365.
If you want to know more about setting up the includes office 365 Azure AD portal then
see my my online course:
Integrating Azure Active Directory Features with Office 365
What’s coming soon will be the ability to use social media accounts like Twitter, Facebook and Google Plus to login to externally shared Office 365 resources. That is going to really make external sharing of Office 365 information easy. I can’t want for when that is available and I’ll make sure I write an article on it.
In summary, using the built in B2B collaboration that comes with Office 365 you can now more easily share information with external parties that have their own domain.
What this stuff should also illustrate is how important Azure AD is to Office 365 and how you really need to enable it to get access to the additional options that are available with Office 365. In short, if you are not using Azure AD with Office 365 then you are driving around everywhere in first gear!
Also, please don’t forget to take a look at all my online courses at:
http://www.ciaopsacademy.com
You may even find a lesson about this very topic in there shortly.