When you set up an Intune App Protection Policy for Windows 10 you are effectively enabling Windows Information Protection (WIP). This is designed to protect your business information being shared with non-business approved applications. This means there are a range of standard business ‘approved’ applications that are enabled by default. These are typically ‘enlightened’ apps that can differentiate between corporate and personal data. This allows them to abide by the policies set in the Intune App Protection policy you create. Applications that are not ‘enlightened’ are typically blocked from working with corporate data.
In a previous article:
Intune App Protection Policy blocking browser
I detailed how this could affect third party, non-Microsoft browsers, like Chrome, accessing the Internet. That article, also showed you how to easily overcome that issue with some minor configuration changes.
In this article I’ll look another way that ‘non-enlightened’ apps get blocked and how you can easily enable them.
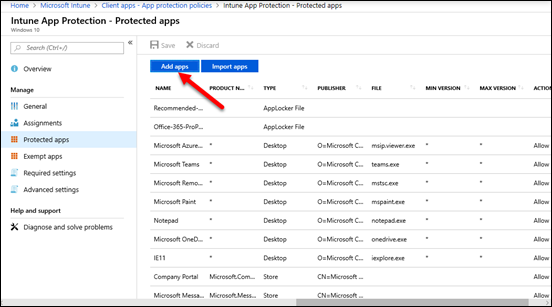
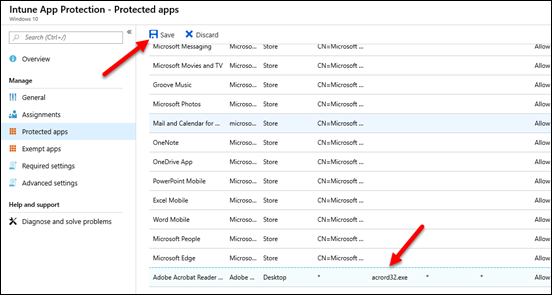
So, let’s say that you have created an Intune Windows 10 App Protection policy like that shown above. When you do you configure a number of Protected apps as you can see. Typically, these a Microsoft products like Office, Internet Explorer, Edge and so on.
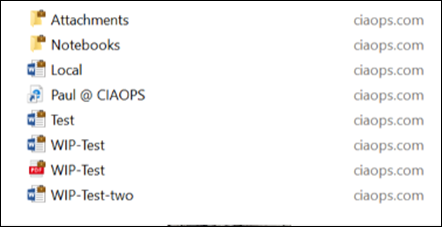
With that default protection policy successfully applied to a Windows 10 machine you can then see the data identified as personal or business on that machine now. The above shows you some files in OneDrive for Business, which is considered a business location. You can tell they are business files by the little brief case in the upper right of the file icon. Thus, all these files are considered to be business and are protected by WIP.
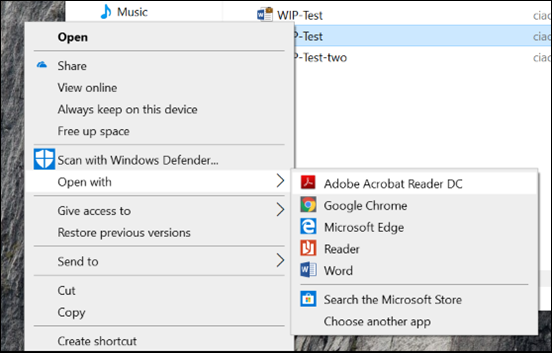
Let’s say that I now want to open the business PDF file with Adobe Acrobat Reader.
The result is, you are unable to do this because Acrobat Reader is not an ‘enlightened’ app. Thus, it is considered a personal app and is therefore denied access to business information.
To rectify this situation we need to return to the Protected apps section of the Intune App Protection policy and select the Add apps button as shown.
You then need to select the option Desktop apps from the pull down at the top of the screen. When you do so, you will probably see no apps listed below.
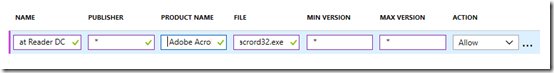
You should now enter the following information into the fields:
Name = Acrobat Reader DC
Publisher = *
Product Name = Acrobat Reader
File = acrord32.exe
Min version = *
Max version = *
Action = Allow
The most important item here is the filename for the program is entered correctly, (without any path) into the File field. In this case, the executable for Acrobat Reader is acrord32.exe.
Select Ok, once you are entered all the file details correctly here. Basically we are creating an exception for this app with WIP.
You should now see the program you just added in the list as shown above. Make sure you also Save your changes so they get applied to the policy.
Now with the policy updated, and the exemption for your app created, (in this case Acrobat Reader), you just need to wait a short time until the policy is applied to your machines.
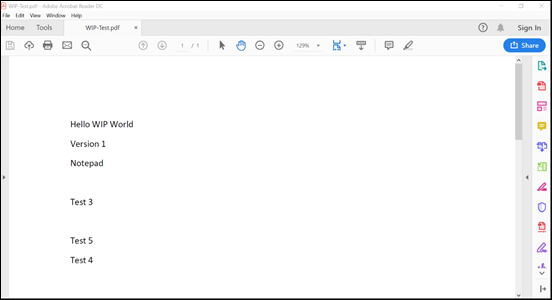
With a few minutes, you should be able to repeat the process of opening that same business file and find that you can now view the file as shown above is the program that you couldn’t before.
You can now basically repeat the same process for any other custom applications you have that are ‘non-enlightened’ and you wish to have open business information saved in Microsoft 365 protected with WIP.



Hi Rob,
We are getting the same access denied issue in opening PDF files from OD4B on local PC. we added acrobat as protected app but still can’t open. Any idea why?
LikeLike
Ensure the policy is actually being applied to the device and you have the corporate and non-corporate locations set correctly.
LikeLike
I did exactly what you described in the post but it is not working. I can’t access work content pdf file using acrobat reader.
LikeLike
Check your policies. It is easy to get wrong filename or something like that. Also check that the policy is applying correctly.
LikeLike
Every recommended application that I configured with WIP behaves correctly except acrobat reader. so, I think everything related to the policy applied correctly
LikeLike
Same here. This doesnt seem to work for me. All other policies work
LikeLike
Doesn’t work here either. I found the advice somewhere to fill in the publisher name instead of an asterisk. The publisher name can be found with Powershell:
Get-AppLockerFileInformation -path “C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\acrord32.exe” |format-list
That resulted in “O=ADOBE INC., L=SAN JOSE, S=CA, C=US”.
Although it didn’t help in my case (still doesn’t work) it may help others.
LikeLike
After some long weeks of trying to get through to an Intune engineer, they were able to solve this for me with the following configuration.
Firstly, this only works in the Exempt list, not the allowed list (at least in my setup using a WIP w/o enrollment policy). You will need to remove any previous entries for Adobe reader from either list before adding the following desktop app to the exempt list:
Name: ACROBAT READER DC
Product name: ADOBE ACROBAT READER DC
Publisher: *
File: ACRORD32.EXE
Min Version: *
Max Version: *
The engineer then had me force sync my work access profile a good 5 times in quick succession before attempting to open a PDF…and finally after nearly 2 months, it WORKED!
Note that I had the latest free version of Adobe Acrobat Reader DC (the DC bit being important) version 2020.006.20034 – the engineer thought that the enterprise paid version of Adobe Reader DC could have the necessary integrations for the app to work within the allowed list of WIP policies, but he wasn’t 100% sure.
I leave this here in hopes it helps another poor soul like myself that found this article in the past, got really exited and then had there hopes dashed when it didn’t work…!
LikeLike
Thanks for the reply, I will give this a try too.
LikeLike
Thank you Alex VB! This is the only configuration that worked for me for exempting Acrobat Reader
LikeLike
You beauty! This worked for me, too, thanks for posting!
LikeLike
I have tested this for months. Both the exempt and the allowed works this way but it depends on what you need. For example, if users just want to read pdf’s this is fine. If they want to sign the document or use any other Adobe tools, Adobe will run a different service which is not exempted, and it will crash at that point. In order for the tools to work you need to exempt or allow them one by one as if they are different applications.
LikeLike
This one worked! Thx
LikeLike
Thanks to Alex VB I got Acrobat Reader working in my WIP. Does anyone know how to get Acrobat DC (the version that allows editing) to work as a protected app?
LikeLike
Just to let you guys know, i was not succesful with this method, tried all above and it didn’t work. I then looked at the exe in the process monitor and i saw that the .exe name was a mix of capitals and non capital lettering, AcroRd32.exe, i’ve entered this exact name in the field, and now it works.
LikeLike
This also worked for me, kudo’s to Lennart!
LikeLike
I was able to get it to work using https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protection/wip-learning#use-device-health-and-intune-to-adjust-wip-protection-policy.
I followed the instructions and went to…
Microsoft Endpoint Manager admin center->All Services->Apps->Monitor->Reports. The “App learning report for Windows Information Protection” report listed Acrobat DC with the following information
O=ADOBE INC., L=SAN JOSE, S=CA, C=US\ADOBE ACROBAT DC\ACROBAT.EXE\20.13.20064.12623
Desktop
I then went to Microsoft Endpoint Manager admin center->All Services->Apps->App protection polices and added the above information to the WIP.
I am now able to successfully open protected data in Acrobat DC.
LikeLiked by 1 person
May you please try to edit or sign the document now?
LikeLike
Yes. I was able to edit and sign the protected pdf in Acrobat DC.
LikeLike
Thanks for your reply. Was the document protected and running under enterprise context?
LikeLike
Yes, the pdf was protected and running under enterprise context.
LikeLike
Hey there, I’ve been banging my head against a wall with this one so I was wondering if you would be happy for me to pick your brain on this?
So far I’ve got the following in Endpoint Manager inthe WIP-WE protection policy but for the life of me I cant get it to work
Name: Adobe Acrobat DC
Publisher: O=ADOBE INC., L=SAN JOSE, S=CA, C=US
Product Name: ACROBAT.EXE
Min Version: *
Max Version: *
Action: Allow
I have tried all sorts so far such as lower case “acrobat.exe”, * for the Publisher and name etc but I cant seem to get it to open apps without stating “This document cannot be opened”
If you could provide some more info on how you got yours working it would be greatly appreciated
LikeLike
Looks like you need to change Product name to “ADOBE ACROBAT DC” and then add File: “ACROBAT.EXE” … all without quotes.
Here are my settings:
Type: Desktop apps
Name: ADOBE ACROBAT DC
Publisher: O=ADOBE INC., L=SAN JOSE, S=CA, C=US
Product Name: ADOBE ACROBAT DC
File: ACROBAT.EXE
Min Version: *
Max Version: *
Action: Allow
After you make the change you will need to wait ~15 minutes for propagation and then for your computer to sync. After ~15 minutes you can force your computer to sync by navigating to Start->Settings->Accounts->Access work or school. Click on your work email address and click Info. Near the bottom click Sync.
You should also see in Start->Programs that Adobe Acrobat DC will have “Managed” listed next to the name.
LikeLike
Thank you! That worked for me
LikeLike
Go to Microsoft Endpoint Manager admin center->All Services->Apps->Monitor->Reports->“App learning report for Windows Information Protection” report. This will provide let you know any app that has attempted to access the Office 365 data. You can use the information to configure your WIP. The information is delimited by /
LikeLike
Has this been removed from Microsoft? I’ve tried everything mentioned in this blog post and in the comments but whatever I set in the Protected Apps, nothing works. Always shows as “Personal” in the “Enterprise context” column of Task Manager. Was able to add other Microsoft apps like this, but third party apps does not seem to work and I cannot find any information from Microsoft that suggests that they support third party apps as enlightened apps.
In fact I found this reddit thread that suggests third party apps will not work: https://www.reddit.com/r/Intune/comments/ius9zr/windows_information_protection_third_party_apps/
LikeLike
It works still to my knowledge
LikeLike
I was able to resolve it by adding it in to the Exempt-list instead of the Protected-list. After reading more about the subject (and especially Enlightened vs Unenlightened apps) it became clear as of why.
“Adobe Acrobat Reader is an Unenlightened application that helps to view PDF files. A user can use it to view personal PDF files as well as corporate PDF files. If you add this Unenlightened application to the Protected Apps section of your WIP policy, the application will enforce protection (encrypt file) even when a user opens a personal PDF file, which is undesirable. As such you should be adding this kind of apps to the Exempt Apps section instead.”
I used wildcards for everything except the publisher info.
LikeLike