Microsoft Edge is a modern, secure-by-default browser, but organizations can further harden it using tools in Microsoft 365 Business Premium – especially Microsoft Intune – to protect users and data. This post outlines best practice security settings for Microsoft Edge and details how to deploy and manage these settings across a fleet of devices using Intune. We also cover ongoing management, monitoring, and user awareness to ensure maximum day-to-day protection.
Introduction: Why Secure Edge with Intune
Microsoft Edge for Business provides a dedicated work browser experience that is secure by default, separating work and personal browsing data to prevent leaks[6]. It includes robust built-in security features (like Microsoft Defender SmartScreen) and supports enterprise controls. However, to achieve a consistent security posture across all devices, IT administrators should enforce configurations via Intune. Microsoft Intune (part of M365 Business Premium) allows centralized management of Edge’s security settings on Windows PCs, Macs, and mobile devices. By leveraging Intune policies, security baselines, and integration with other Microsoft 365 security tools, organizations can:
- Enforce security best practices on every Edge browser used for work (e.g. enable phishing protection, restrict unsafe features).
- Deploy these settings at scale to all managed endpoints (Windows, macOS, mobile) in a uniform way.
- Ensure compliance with organizational security requirements and industry recommendations.
- Monitor and update Edge configurations over time, responding to new threats and updates.
In the sections below, we’ll first explore the key Edge browser security settings and best practices. Then we’ll provide a step-by-step guide to implement these via Intune, discuss deployment to multiple devices, and cover management, updates, and user training.
Best Practice Security Settings for Microsoft Edge
To secure Edge browsers in an enterprise environment, administrators should focus on several critical security areas. Microsoft provides an Edge security baseline – a template of recommended settings – which we will use as a reference for best practices. This baseline reflects the latest security team recommendations for Edge’s configuration[1]. Below is a summary of key Edge security settings and their recommended state (as per Microsoft’s baseline and industry best practices), along with their purpose:
| Security Setting |
Recommended Configuration |
Purpose / Protection |
| Microsoft Defender SmartScreen |
Enabled (On) |
Blocks access to phishing sites, malicious downloads, and other threats in real-time. |
| SmartScreen – Potentially Unwanted Apps (PUA) |
Enabled (On) |
Blocks download of adware, browser hijackers, and other low-reputation apps. |
| SmartScreen Bypass |
Disallow user bypass |
Prevents users from clicking through warning pages for malicious sites or files. |
| Typosquatting Checker |
Enabled |
Warns users if they mistype URLs and helps avoid look-alike malicious sites. |
| Site Isolation (Strict Site Per Process) |
Enabled (On) |
Isolates each website in its own process, mitigating spectre-type attacks between sites. |
| Legacy Browser Mode (IE mode) |
Disabled unless needed |
Avoids using Internet Explorer mode except for approved legacy sites, reducing exposure to older insecure web technologies. |
| HTTP/Legacy Authentication |
Disable Basic auth |
Blocks legacy HTTP Basic authentication to prevent sending credentials in cleartext; only allow modern auth (NTLM/Kerberos). |
| Browser Extensions |
Restrict add-ons (block unapproved) |
Block all unauthorized extensions – by default, no extensions are allowed unless whitelisted. This prevents installation of malicious or unvetted add-ons which could hijack the browser. |
| Legacy Extension Points |
Enabled (Block legacy hooks) |
Blocks old-style extension injection points, preventing malware from using unsupported methods to hook into Edge. |
| Application Bound Encryption |
Enabled |
Encrypts browser data tied to user identity or device, adding a layer of protection for stored credentials/cookies. |
| Insecure Network Requests |
Blocked |
Blocks requests from HTTP websites to local or more secure network resources (protects against cross-network attack vectors). |
| TLS/Encryption Protocols |
Enforce TLS 1.2+ |
Ensure only modern TLS versions (1.2 or 1.3) are used, preventing fallback to deprecated 1.0/1.1 protocols that have known weaknesses. |
| Password Manager / Autofill |
Configured securely |
Consider disabling password save for sensitive accounts or ensure saved passwords are protected by OS credentials. (The baseline doesn’t disable it entirely, but organizations may choose to manage this depending on policy.) |
| Automatic Updates |
Enabled (Auto-update Edge) |
Allow Edge to update itself automatically on all devices for timely security patches. Do not disable the built-in update mechanism. |
As shown above, Microsoft’s Edge security baseline already sets most of these configurations to the recommended values by default.[1] By using this baseline (or configuring equivalent settings manually), you achieve a hardened browser configuration that significantly reduces risk.
Below we further explain some of these best practices and why they are important:
- SmartScreen & Phishing Protection:
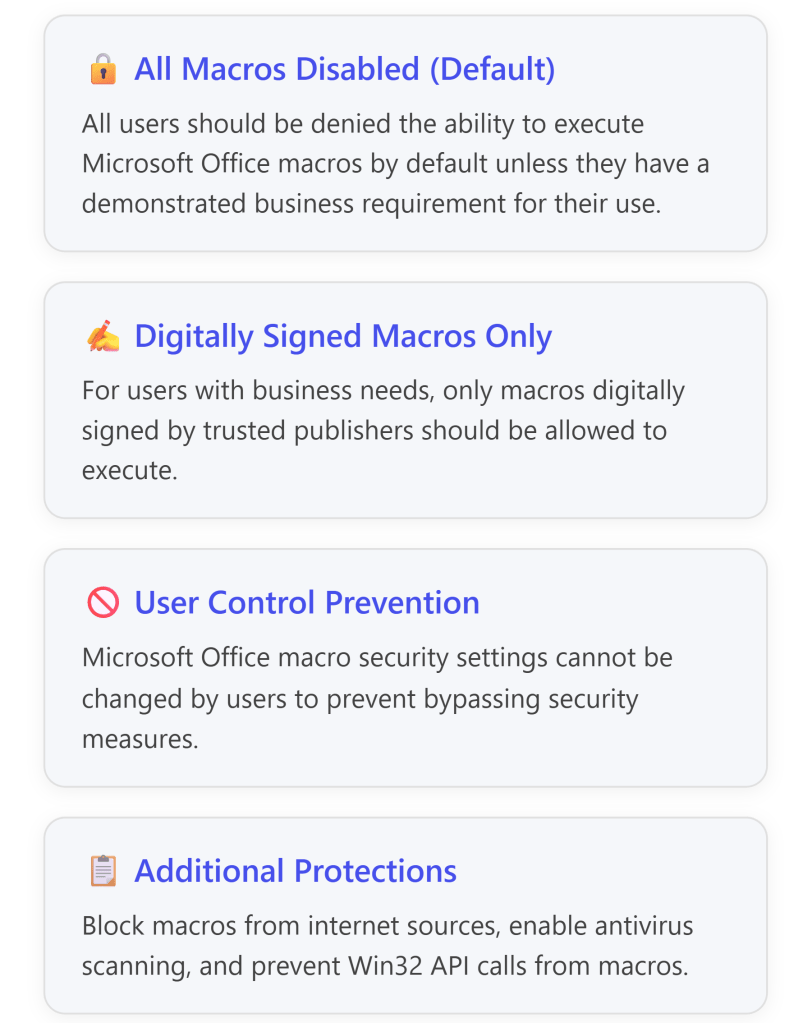
Microsoft Defender SmartScreen is a cloud-based URL and app reputation service built into Edge. Enabling SmartScreen (with no user bypass) is critical – it provides industry-leading protection against phishing websites, malicious drive-by downloads, and other web threats[2][1]. SmartScreen will block known dangerous sites and files, and with Potentially Unwanted App blocking enabled, Edge also prevents users from inadvertently downloading unwanted software like adware[1]. The baseline sets SmartScreen and PUA blocking on, and even stops users from bypassing the warnings[1], ensuring maximum protection.
- Typosquatting Checker:
This feature warns users if they mistype a popular URL (for example, “micros0ft.com” instead of “microsoft.com”) and might have landed on a fraudulent look-alike site. Enabling typo protection helps prevent credential theft via spoofed domains[2]. The Edge security baseline enables this by default[1].
- Site Isolation:
Site Isolation (also known as strict site-per-process) forces each website to run in a separate browser process. This is a defense against attacks like Spectre, which attempt to read data across sites via speculative execution vulnerabilities. With site isolation enabled, a malicious site cannot easily access data from other sites’ sessions[7][3]. Microsoft’s baseline now enables full site isolation for every site (earlier versions had it off, but it’s enabled in newer baseline versions)[3].
- Legacy Content (Internet Explorer Mode):
Edge can use IE mode for legacy web apps, but IE’s outdated rendering can pose security risks. Best practice is to minimize the use of IE mode. The baseline disables loading unconfigured sites in IE mode[1] and hides the “Reload in IE mode” button[1], so IE is only used for sites explicitly configured by IT. This reduces exposure to old ActiveX or insecure controls. Only enable IE mode for trusted internal sites that absolutely require it.
- Encryption and Network Protections:
Edge and Windows support modern encryption protocols. Force strong encryption by disallowing legacy protocols. The baseline, for instance, disables old TLS 1.0/1.1 (Edge already deprecated these by default) and ensures TLS 1.2 is the minimum[7]. It also disables HTTP Basic authentication in the browser[1] – Basic auth sends credentials in plaintext and should be avoided in favor of NTLM or OAuth flows[1]. Additionally, Edge baseline disables insecure cross-network requests (Private Network Access)[1], which stops public websites from reaching into internal resources by default – mitigating certain CSRF and lateral movement scenarios.
- Extensions Management:
Browser extensions can greatly increase productivity but also introduce risk. Malicious or poorly made extensions might redirect users to phishing sites, inject ads or scripts, or steal data[7]. A best practice is to allow only approved extensions. The Intune Edge baseline helps here by including a setting to block all extensions by default[1]. Administrators can then maintain an allow-list of specific extensions if needed (by specifying permitted extension IDs and leaving others blocked). This way, users can’t install random add-ons – reducing malware and data leak risks. If your organization needs certain extensions (password managers, etc.), explicitly approve those and keep the list minimal and reviewed.
- Legacy Plug-ins and Code:
Edge has a setting to block legacy extension points (legacy plug-in APIs or injection mechanisms used by older apps/malware). The baseline keeps this blocking enabled[1] to prevent any unsupported mechanism from loading into Edge’s process. This hardening measure protects against malware that tries to use outdated hooks to compromise the browser.
- Application Bound Encryption:
Newer versions of Edge support Application Bound Encryption, which ties data encryption to the application context or user’s corporate identity. The security baseline enables this by default[1]. In effect, it ensures certain sensitive data that Edge stores (like cookies or credentials) are additionally encrypted such that only Edge (or only the user’s profile) can use them. This reduces the risk of sensitive browser data being stolen and used outside the browser, even if the underlying OS is compromised.
- Auto-Updates for Edge:
Keeping Edge up-to-date is one of the simplest yet most vital security practices. Microsoft Edge receives frequent security updates (aligned with a 4-week stable channel cycle). Allow Edge to update automatically in your environment. By default, Edge’s internal updater will periodically check and install updates[5]. Intune can enforce the update check frequency if needed (via Edge Update policies)[5], but generally the key is: do not disable or delay Edge updates. Ensuring all users run the latest Edge version means known browser vulnerabilities are patched and the latest protections are active. We will discuss later how Intune can help monitor or enforce update compliance.
By implementing the above settings, you establish a strong defensive baseline for web browsing. Next, we’ll describe how to use Intune to configure these settings across all your devices in a scalable way.
Implementing Edge Security Policies with Intune
Microsoft Intune (part of the Endpoint Manager) is the primary tool to enforce the Edge configurations described. Intune offers multiple methods to deploy browser policies:
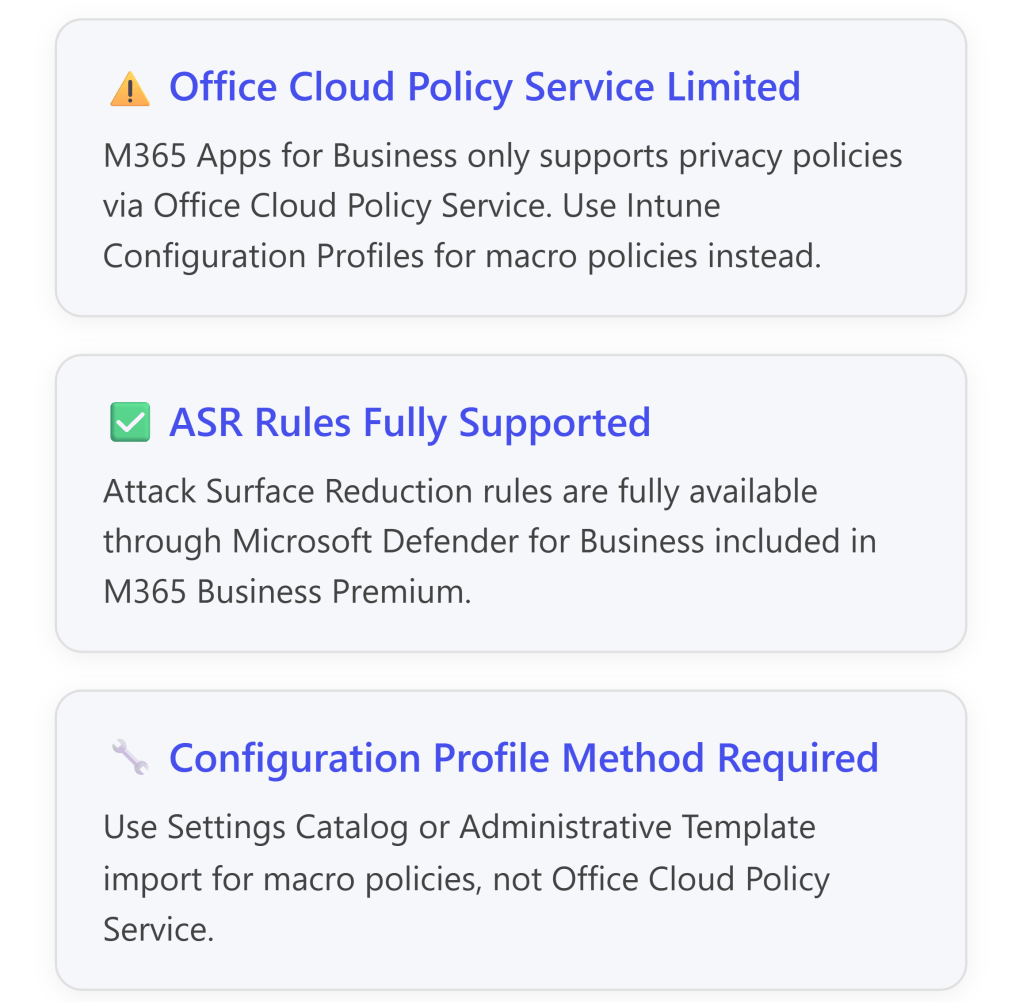
- Security Baselines – Microsoft provides a pre-packaged Microsoft Edge Security Baseline profile in Intune. This is a template with a comprehensive set of recommended settings (many of which we summarized above) that you can deploy with minimal effort. The baseline ensures a default secure posture for Edge aligned with Microsoft security team guidance[1].
- Configuration Profiles – For more granular control or to implement settings not in the baseline, Intune allows custom Configuration Profiles. Using the Settings Catalog or Administrative Templates in Intune, admins can configure individual Edge policies (analogous to Group Policy settings) and deploy them. This can supplement or fine-tune the baseline.
We’ll focus first on using the Edge Security Baseline, as it covers best practices out-of-the-box.
Using the Microsoft Edge Security Baseline in Intune
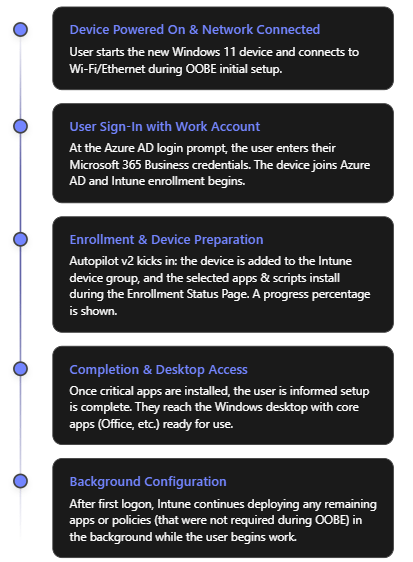
Intune’s Security Baseline for Edge is the fastest way to apply a broad set of hardened settings to Edge browsers. It includes dozens of configurations with Microsoft’s recommended defaults. Follow these steps to create and deploy an Edge baseline profile:
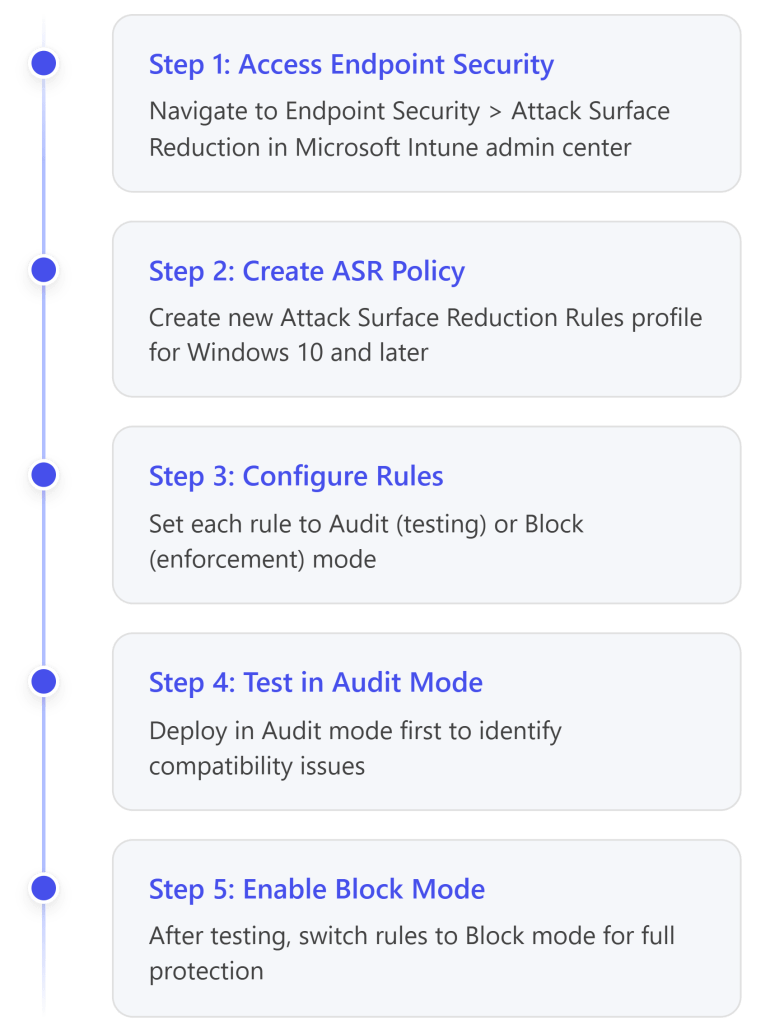
- Open Endpoint Security > Security Baselines in Intune: Sign in to the https://endpoint.microsoft.com/ and navigate to Endpoint security > Security baselines. You’ll see a list of available baseline templates (Windows 10, Defender for Endpoint, Microsoft Edge, etc.)[3].
- Select the Edge baseline and create a profile: Choose Microsoft Edge (version 112 and later) from the list (this is the Edge for Windows 10/11 baseline)[3]. Click + Create profile. Give the profile a name (e.g. “Edge Browser Security Baseline”) and optional description[3].
- Review and configure settings: On creation, you can review the baseline’s settings groups. By default, all settings are set to Microsoft’s recommended value (as summarized in the table above). You can leave them as-is for a standard deployment. Optionally, you may customize specific settings – for example, if you want to allow a particular extension or adjust a policy, you can modify that before deployment. Intune’s interface lets you expand categories (Security, Privacy, Extensions, etc.) and see each setting and its default[3]. Insights (lightbulb icons) may be available next to settings to indicate how many other organizations enable a setting, which can guide you[3].
- Assign the baseline profile to device groups: Once the profile is ready, proceed to the Assignments step. Select one or more Azure AD groups containing the target users or devices to include[3]. For example, you might assign it to an “All Corporate Devices” group. (You can also exclude certain groups if necessary, e.g., a pilot or IT testing group.) Note: The Edge baseline contains both computer and user settings, and Intune will handle applying them appropriately. At least one group must be assigned, otherwise the profile won’t deploy[3].
- Finish and deploy: Click Review + create and then Create. As soon as you create the baseline profile, Intune will push it to all devices in the assigned groups[3]. Managed PCs will receive the settings policy over the air. Users might need to restart Edge for certain policies to take effect immediately, but many settings apply dynamically.
Tip: It’s recommended to test new baselines on a small set of devices before broad deployment. Intune allows creating multiple baseline profiles – you could assign a baseline first to a pilot group, verify the impact, then roll out to everyone[3]. You can also duplicate a baseline profile and update it (e.g., when a new baseline version is released) for testing before replacing the old one[3].
- Monitor deployment status: After deployment, you can check Intune > Endpoint security > Security baselines > [Your Edge baseline] > Device status to see a report of devices and whether the policy succeeded, is pending, or has errors. A successful status indicates the device has applied the Edge settings. We’ll cover more on monitoring in a later section.
Using the security baseline is often the best method, as it bundles all essential settings. However, you might want to adjust or add policies outside the baseline. For instance, maybe you want to configure a new Edge setting that the current baseline doesn’t include, or you want a slightly different value for a particular setting. This is where custom configuration profiles come in.
Custom Edge Configuration via Settings Catalog (Optional)
Intune’s Settings Catalog provides access to all available Edge policies (equivalent to the Chrome/Edge ADMX settings) that you can configure in a profile. This approach is useful if you need to:
- Add settings beyond what the baseline covers (for example, a brand-new Edge feature or a less common setting).
- Relax or tighten a baseline setting for specific groups (e.g., allow a certain extension for developers while baseline blocks all others).
- Manage Edge settings on platforms like macOS (the Windows baseline might not apply there, so you’d create a separate macOS configuration profile for Edge).
To create a custom Edge policy profile:
- In the Intune admin center, go to Devices > Configuration profiles and create a new profile. Choose the appropriate platform (Windows 10/11, macOS, etc.) and pick Settings Catalog as the profile type.
- Under Configuration settings, click Add settings. Search for “Edge” to see categories of Edge browser settings. Intune lists hundreds of available settings derived from the Edge administrative template.
- Select the desired settings and set their values. For example, to enforce extension blocking manually: find “Control which extensions cannot be installed” and add it, then set it to Enabled and specify “*” (block all) as the prohibited extensions list[1]. Likewise, you can configure SmartScreen (Enable Microsoft Defender SmartScreen = Enabled)[1], “Prevent bypass of SmartScreen warnings” (Enabled)[1], “Enable site isolation” (Enabled) etc., matching the best practices discussed. Each setting in the catalog includes a description of what it does, and often a link to documentation.
- Once you’ve configured all needed settings, assign the profile to your device/user groups similar to the baseline assignment. Intune will deploy these settings to those devices.
- Monitor the profile deployment under the profile’s Device status, and resolve any conflicts. (If a device has both a baseline and a custom profile with overlapping settings, ensure they are consistent. Intune will mark a conflict if two policies set the same setting differently. It’s usually best to avoid duplicates – you can stick mostly to baseline OR custom for a particular setting, but not both with different values.)
Using the Settings Catalog approach requires more manual work to select and configure each setting, but it provides flexibility. Many organizations will start with the Edge security baseline (for broad coverage) and layer any additional needed settings via a small custom profile.
Intune App Protection (MAM) for Edge on Mobile
In addition to device configuration profiles (which apply to managed devices), M365 Business Premium allows App Protection Policies for scenarios where you manage only the app (Edge) on a mobile device. For example, if employees access corporate web apps via Edge on their personal phone (without enrolling the phone in Intune), you can use Intune’s MAM (Mobile Application Management) policies on Edge for iOS/Android.
These policies can require a PIN to open the app, prevent data from Edge being copied to personal apps, require Edge to open links from corporate emails, etc. Edge for Business on mobile can be managed such that corporate data viewed in the browser is containerized and protected[6]. If this scenario applies, configure an App Protection Policy targeting the Edge app for your user group – enabling features like app-level encryption, disable “Save-as” for files, block screenshots, and so on, to secure corporate web access on unmanaged devices[6]. This extends your Edge security to BYOD cases.
Deploying Policies Across Your Device Fleet
Deploying the Edge security settings across a fleet is straightforward with Intune once the profiles (baseline or custom) are set up. Here are some best practices for fleet-wide deployment:
- Organize devices into Azure AD groups: Intune assignments are group-based. Ensure all company endpoints are members of a group (or multiple groups) that you target with the Edge policy. Many admins use an “All Managed Devices” dynamic group. Alternatively, separate groups by platform if you have different profiles for Windows vs. macOS.
- Include new devices automatically: If using dynamic device groups (e.g., all devices with a specific enrollment tag or all Windows 10 devices), any new device enrolled into Intune will automatically receive the Edge policies shortly after enrollment. This is useful for autopilot scenarios – when a new PC is set up, it joins Intune and moments later the Edge hardening policy is applied, ensuring compliance from day one.
- User vs Device targeting: The Edge baseline can be assigned to device groups (then user settings in it apply to any user on those devices) or to user groups (then when that user logs into any managed device, the settings apply). Microsoft documentation notes that you may need multiple profiles if you want to cover both device-targeted and user-targeted scenarios[3]. However, for simplicity, many organizations assign Edge policies to devices (since browsers are generally used on company devices). Choose the approach that fits your management model.
- Monitoring deployment: After a broad deployment, use Intune’s reports to ensure all devices have received the policies. Under Reports > Endpoint security or under the baseline profile’s per-setting status, you can identify if any device is in error or conflict. Ideally, all managed devices should show the Edge profile status as “Succeeded”. Any failures should be investigated (e.g., perhaps a PC is offline, or a setting is not applicable to Windows Home edition, etc.).
- Policy refresh: Intune-managed devices typically check in and refresh policies periodically (every ~8 hours by default, with some variance). If a device is powered off or offline, it will get the Edge policy next time it comes online and syncs. You can expedite testing on a specific device by using “Sync” from the Intune portal (or Company Portal app) for that device.
By thoughtfully targeting groups and monitoring, you can achieve near 100% coverage of your fleet with these Edge security settings. This ensures every user’s browser adheres to your security standards, whether they are in the office or remote.
Managing User Access and Identities in Edge
Securing the browser also involves managing how users access corporate resources through Edge and what they can do with their accounts:
- Require Azure AD Sign-In for Edge (Work Profile): Encourage or enforce that users sign into Edge with their work (Entra ID/Azure AD) account. This turns on “Edge for Business” mode automatically, separating work browsing from any personal profiles[6]. When signed-in, enterprise policies (like the ones deployed via Intune) are enforced on that profile. You can use Azure AD Conditional Access policies to ensure that only compliant, domain-joined, or Intune-managed devices can access certain resources – indirectly this means they must use the managed Edge (or other compliant apps) to log in. For example, a Conditional Access policy could block access to Office 365 from unmanaged browsers, guiding users to use their Intune-managed device with Edge.
- Multiple Profile Control: Edge allows multiple browser profiles (e.g., personal and work). Admins can set policies to limit the mixing of profiles, such as disabling the ability to add additional profiles or at least controlling sign-in modes. One policy of interest is ”BrowserSignin” which can force users to sign into Edge with a work account or block personal sign-in. Coupled with “Enterprise Profile Separation”, this ensures work content stays in the work profile. While not always enforced in Business Premium environments, these settings can be considered if data separation is a concern.
- Permissions and Capabilities: Through Intune’s Edge settings, you can also manage specific browser capabilities for users:
- For instance, you might disable the Edge Password Manager or Form Autofill for highly sensitive environments, or require a primary password. The security baseline doesn’t outright disable password saving, but it’s something to review based on your org’s password management strategy.
- You can restrict printing or saving of work data via Edge if needed (e.g., disable printing from Edge to avoid physical data leakage, or restrict downloads to only certain locations).
- Manage Favorites and data sync: Corporate Entra ID accounts can sync Edge favorites, history, etc. to Microsoft cloud. This is generally useful and encrypted, but some orgs might disable cloud sync for confidentiality. Intune can control that (“Allow syncing of browsing data” policy).
- Conditional Access App Control: For web apps, Azure AD Conditional Access can integrate with Defender for Cloud Apps to apply session controls in Edge (e.g., preventing downloads of sensitive files via the browser for unmanaged sessions). This is more of an Azure AD/M365 E5 feature, but mentionable as an additional layer if Business Premium customers opt for add-ons: effectively, even if a user is in Edge, the access can be limited by cloud policy if certain risk conditions are met.
In summary, leverage Intune and Azure AD to ensure that Edge is used in a managed, authenticated context. By tying Edge usage to the user’s corporate identity, you gain better control (policies follow the user) and visibility (logs of sign-ins, conditional access reports). Edge for Business will keep personal and work browsing separate[6], reducing the chance of corporate data mixing with personal accounts.
Monitoring and Compliance
After deploying security policies, ongoing monitoring is crucial to maintain Edge’s secure state across all devices.
- Intune Policy Compliance: Intune provides compliance and configuration reports. Regularly review the Device compliance dashboard in Intune. While Edge settings themselves are configuration profiles (not “compliance policies” in Intune’s terminology), a device’s overall compliance can be tied to whether required settings are in place. For example, you might create a Custom Compliance Policy that checks if a particular registry key (set by the Edge policy) exists, though this is advanced. More straightforward: check each managed device in Intune – under Device Configuration > Setting status, verify that no Edge setting is in error or conflict. Any misapplied setting should be fixed promptly.
- Security Baseline Compliance: If you used the Edge baseline, Intune has a dedicated report for baseline compliance. It will show each setting and how many devices deviated or had issues. Pay attention to any settings showing non-compliance. Perhaps a user changed something or a machine is missing the policy. Intune can’t usually be “undone” by the user (since these are enforced), but a user might install an unsupported extension if they found a workaround, etc. If an Edge policy was misapplied (e.g., due to concurrent GPO in Hybrid AD scenarios), Intune will flag a conflict.
- Defender for Endpoint Signals: M365 Business Premium includes Defender for Endpoint (Plan 1). If onboarded, Defender for Endpoint will monitor browser threats. Edge is tightly integrated with Defender – SmartScreen blocks, for instance, are reported. Check the Microsoft 365 Security Center for any alerts related to Edge, such as attempts to visit malicious sites that were blocked. While Plan 1 might not have full Threat & Vulnerability Management, it will still log detected threats. If you see repeated SmartScreen blocks for certain users, that might prompt further training or investigation.
- Browser Update Compliance: Ensure all devices are running a recent version of Edge. Because Edge auto-updates, this is generally the case if internet access is available. For compliance, you can use Intune Proactive Remediations (a scripting feature) or a reports to see Edge versions installed. If some devices fell behind (perhaps auto-update was disabled or failed), Intune can push an update. One method is to deploy the latest Edge installer as a Win32 app to those devices, but normally enabling auto-update is simpler. Consider implementing the Edge Update policy via Intune that sets Auto-update check period override to a reasonable interval (e.g., every 4 hours)[5], to ensure frequent update checks. Intune doesn’t have a native “Edge version compliance” policy, but you could use Azure AD or Endpoint analytics to query versions.
- Logging and Auditing: Edge itself produces logs/events for policy enforcement. For example, if an extension is blocked by policy, that event can be found in the Event Viewer under Applications and Services Logs -> Microsoft -> Edge. In a security audit, you might review such logs or use a log aggregator. However, this is typically only done if investigating an incident. Day-to-day, rely on Intune and Defender dashboards for a high-level view.
- User Feedback Loops: Sometimes users will report an issue (e.g., “I can’t install an extension” or “Edge won’t let me bypass a certificate warning”). These reports are actually signs that your security policies are working! Nonetheless, monitor helpdesk tickets or user feedback to identify if a policy is too restrictive or causing workflow issues. For instance, if a developer legitimately needs a certain extension, you might adjust the allowed list. Monitoring isn’t just technical – it’s also listening to user impact and balancing security with usability.
By actively monitoring these areas, you can verify that your Edge security measures remain effective and that all devices stay in line with the policy. It’s far easier to address compliance drift or new threats early than to remediate after a breach.
Keeping Edge Up-to-Date and Patched
Maintaining the latest browser version is a non-negotiable aspect of browser security. New Edge releases often patch security vulnerabilities and introduce improved defenses. Here’s how to manage updates:
- Built-in Auto-Update: Microsoft Edge’s built-in updater is the primary mechanism to get updates. By design, Edge will automatically download and install updates in the background for users, without needing full admin rights. This should be kept enabled in all environments. The good news is that, on a standard Windows install, users typically cannot easily disable Edge updates (especially if governed by Intune policies). Verify that no Intune policy or GPO is inadvertently turning off updates. The default (no special policy) is that Edge checks for updates approximately every 12 hours[5]. You can shorten this interval via policy if needed[5].
- Intune Management of Updates: While there isn’t a dedicated “Edge update” slider in Intune like there is for Windows Update, you can deploy Edge update configurations via Administrative Templates. For instance, using Intune’s administrative template for Edge, set “Update policy override default” or “Target Channel override” if you want to lock Edge to a particular channel (Stable vs. Extended Stable). Small businesses usually stay on the Stable channel. You might also configure “Allow Edge browser to automatically update” (should be enabled) and “Restore failed updates” (Edge can rollback if an update fails, which is fine). Intune can enforce that Edge continues to update itself normally.
- Forced Updates: In scenarios where a critical fix is out and you want to ensure users restart Edge to apply it, you can send a notice or use Intune’s endpoint analytics messaging or a toast notification script. There is no native Intune button to “reboot all Edge browsers,” because it’s generally not needed (Edge will eventually enforce a restart after update, and users often restart the browser daily). However, in high-security environments, you might instruct users to restart Edge or even schedule a device reboot after a major security update rollout.
- Update Compliance Monitoring: As part of monitoring, review the Edge versions in use. Microsoft’s Security Center or Defender for Endpoint Threat & Vulnerability Management (TVM)—if you had it—would list outdated browsers as vulnerabilities. Without TVM, you can still periodically generate a report using a script: for example, an Intune Proactive Remediation script can query the version of
msedge.exe on devices and report it. Ensure it’s at the expected version (e.g., if the current version is 114.x, no one should be on 112.x). If some devices are lagging significantly, investigate if their update service is broken or if they are rarely online.
- Edge on Mac and Mobile: Don’t forget non-Windows platforms. Edge on Mac updates via Microsoft AutoUpdate (MAU). Intune on macOS can enforce MAU settings. Edge on iOS/Android updates via the respective app stores – ensure your mobile application management doesn’t block app updates. Generally, encourage users to keep apps updated, possibly using Apple’s managed App Store updates or the Google Play Enterprise management for controlled devices.
In summary, let Edge do its job with automatic updates, and use Intune policies only to monitor or fine-tune if necessary. Keeping browsers patched closes the door on many vulnerabilities attackers might exploit.
Integration with the Microsoft 365 Security Ecosystem
One advantage of standardizing on Edge and Intune is tight integration with other M365 security features. Here are ways the Edge security initiative ties into your broader security landscape:
- Microsoft Defender for Endpoint (MDE): As mentioned, Edge shares threat intelligence with Defender. For example, SmartScreen phishing blocks in Edge provide signals to your Security Operations Center via Defender[2]. If a user encounters a malicious site, it’s logged and can be correlated with other alerts. MDE can also do web content filtering for any browser, but it has enhanced controls with Edge (e.g., it can block access to certain categories on Edge specifically if configured). With Business Premium’s MDE P1, you at least get basic web threat monitoring. If upgraded to P2, you get vulnerability management that covers Edge settings and version as part of the endpoint’s security score.
- Microsoft Purview (Data Loss Prevention): Edge has native hooks for Microsoft Purview DLP on endpoints[2]. If your subscription includes Purview DLP (E5 Compliance or an add-on – note: Business Premium might not include full DLP, except possibly for Office apps), Edge can enforce DLP policies such as blocking copy-paste of sensitive info into web forms or preventing uploads of classified files to unsanctioned websites. This is an area to explore if data exfiltration via web is a concern. Even without full DLP, Edge allows basic controls like printing or download restrictions for trusted vs. untrusted sites if you configure it.
- Azure AD Conditional Access: We touched on this under user access, but to reiterate, CA policies can ensure that only devices with Intune policies (compliant devices) access corporate cloud resources. This means even if a user tries a different browser or an unmanaged machine, they’d be blocked. You can specifically target “Browser” as a client app in Conditional Access rules. If you want to enforce Edge usage, one indirect method is to only allow browsers that support integrated Windows authentication or conditional access authentication contexts – in practice, Edge (and Chrome with a plugin) are the primary ones that do. Many orgs simply require “Require device to be marked as compliant” for web app access, which covers Edge since on an Intune-managed device Edge will be compliant.
- Global Secure Access / Secure Web Gateway: Microsoft has introduced Microsoft Defender for Cloud Apps and Azure AD Application Proxy, etc., for securing access. While beyond the scope of this report, note that Edge for Business can work with Microsoft’s SSE (Security Service Edge) offerings (such as Global Secure Access) to route traffic through cloud security gateways. In a Business Premium context, you might not have these advanced features, but the ecosystem is ready to integrate if you do invest in them.
- Logging and Analytics: By using Edge enterprise policies, you gain visibility. For example, signs of abnormal browser usage (mass downloads, visiting risky sites) may surface in logs that feed into Microsoft Sentinel or other SIEM solutions. If you have Sentinel, there are data connectors for Office 365 and Azure AD that, together with Defender logs, can be used to analyze browser usage patterns for anomalies.
In short, securing Edge is not an isolated task – it reinforces and benefits from all other security layers in Microsoft 365. The identity protection, endpoint protection, and information protection features all intersect at the browser. Taking advantage of these integrations can elevate your security posture beyond just configuring Edge settings.
User Education and Awareness
No security configuration is complete without addressing the human factor. While Intune and Edge can enforce many protections, users should be educated on safe browsing practices to complement these technical measures:
- Train employees to recognize browser warnings: Ensure users understand that Edge’s warnings (Smartscreen blocks, certificate errors) are serious. They should not try to circumvent them. In fact, you have disabled bypass for most warnings in policy[1], but explain why. For example, if Edge shows a red phishing warning, the user should know not to proceed (and in our setup, they can’t). Teaching them the importance of those warnings will reduce any temptation to find workarounds.
- Phishing awareness: Regular security awareness training should include spotting phishing attempts, not just in email but on the web. Users should be cautious when entering credentials into web pages. Edge will help by identifying known phish sites and showing the domain clearly, but user vigilance is still key. Encourage them to report suspicious web pages to IT.
- Extensions caution: Since you blocked extensions by default, users might ask “Why can’t I install this add-on?” Educate them that unapproved extensions can pose risks, and there’s a process to request an extension to be allowed if it’s business-critical. This manages expectations and prevents users from attempting to use unmanaged browsers to get an extension (a risk in itself).
- Personal vs Work browsing: Remind users to separate their work and personal web activities. With Edge’s profile separation, it’s easier – work stuff in the work profile (with your policies active) and personal stuff in a personal profile/browser. Users should avoid logging into work sites on personal browsers or devices, as those wouldn’t have Intune protections. Similarly, discourage them from doing personal sensitive transactions on their work browser session.
- Policy transparency: Let users know what protections are in place. For instance, inform them that certain file downloads might be blocked if deemed dangerous, certain websites are off-limits, etc. This can prevent frustration and foster a security culture. Many users feel better knowing the organization is actively protecting them with modern tools, as long as they’re aware of the “rules of the road.”
- Reporting issues: Encourage users to promptly report if they encounter a website needed for work that is being blocked or not functioning due to the browser settings. There may be cases where a line-of-business web app uses an outdated control that got blocked. Rather than the user trying unsafe tweaks, they should alert IT. You can then assess and possibly adjust policy for that site (e.g., allow an exception for an internal site in IE mode if absolutely required, or add a certain URL to Trusted Sites via policy, etc.). A feedback loop helps maintain security without hampering productivity.
Security awareness training should be an ongoing effort – it reinforces that technology alone isn’t a silver bullet. By combining a locked-down Edge configuration with educated, security-conscious users, your defense-in-depth is much stronger.
Ongoing Maintenance and Policy Review
Finally, securing Edge is not a one-time set-and-forget task. Regular maintenance and review will ensure your policies remain effective and up-to-date:
- Stay updated on Edge baseline changes: Microsoft periodically updates the security baseline for Edge (e.g., with each major release or annually). New settings might be added as security features evolve. For example, in version 128 of Edge’s baseline Microsoft added and removed some settings to keep the recommendations current[4]. When Intune offers a new baseline version, review the change log. Plan to update your baseline profiles to the latest version after testing[3]. New settings could include additional protections you want, and outdated ones might be deprecated.
- Evaluate new Edge features: Microsoft Edge is continuously improving, including security features (like Enhanced Security Mode, which was introduced to mitigate memory vulnerabilities by disabling JIT for untrusted sites[2]). Keep an eye on Edge release notes. If a new feature could benefit security, consider enabling it via Intune policy. For instance, Enhanced Security Mode can be enforced (it’s the feature that provides extra protection on unfamiliar sites by using hardware-enforced security). The same goes for upcoming features like Edge network isolation improvements, or integration with Windows Defender Smart App Control – as these come, adjust your policies.
- Revisit exceptions and allowances: Over time, you might grant some exceptions (e.g., allow a specific extension or enable an old protocol for a specific system). Maintain a documented list of these and revisit them periodically. Aim to tighten exceptions if possible (maybe that legacy system got updated and you can remove the exception now). The goal should be to converge back to baseline standards after temporary needs pass.
- Audit configurations: Perform an audit at least annually (if not quarterly) of your Edge Intune configuration. This means reviewing Intune profiles to ensure they align with current best practices, verifying all device groups are covered, and cleaning up any unused profiles. Microsoft’s documentation and compliance toolkit can help compare your settings with the recommended baseline.
- Security incidents review: If there were any security incidents or near-misses involving browsers (e.g., a malware download was caught, or a user fell for a phishing page), analyze if additional Edge controls could prevent those in the future. Maybe enabling a stricter download policy, or integrating a threat feed. Use incidents as learning opportunities to refine policy.
- User feedback and usability: Check in with user representatives or run surveys to gauge if the Edge policies impede work in any way and if so, is there a justified trade-off or a safe adjustment. Browser security is critical, but sometimes overly harsh measures (like completely blocking all downloads) might not be suitable for all roles. Adjust with caution, always weighing risk vs reward.
- Documentation: Keep your own documentation of what settings are deployed and why. This helps for continuity (e.g., if another admin takes over, or if you liaise with compliance officers). Document any rationale for non-standard configurations.
By maintaining vigilance and adapting to new developments, you’ll ensure that your Edge browsers remain a strong link in your security chain rather than a weak point.
Conclusion
Microsoft Edge is a key application through which users interact with the internet and corporate resources, making it a critical component to secure. By leveraging Microsoft 365 Business Premium’s capabilities – especially Intune – you can transform Edge into a highly secure enterprise browser with minimal impact on user productivity. We covered how to apply best practice settings (like SmartScreen, site isolation, extension control, and more) uniformly via Intune, using the built-in Edge security baseline as a foundation[1]. We walked through deploying these configurations to all devices and highlighted the importance of keeping the browser updated and integrated with other security measures like Defender for Endpoint and Conditional Access.
In addition to technical enforcement, we emphasized user education and ongoing management: a secure configuration today must be maintained tomorrow through updates, policy reviews, and training. Security is an ongoing process, and using the rich toolset in M365 Business Premium, administrators can continuously monitor compliance and address new threats as they arise.
By following the guidance in this report, your organization can confidently provide users with a safe, protected browsing experience in Microsoft Edge – one that shields them from threats, protects sensitive data, and meets the highest security standards in day-to-day work. With Intune and M365 Business Premium, enterprise-grade Edge security is within reach for organizations of all sizes, delivered in a cloud-manageable and scalable way.
References
[1] List of settings for the Microsoft Edge security baseline in Intune …
[2] Microsoft Edge for Business Recommended Configuration Settings
[3] Configure security baseline policies in Microsoft Intune
[4] Edge Browser Security Latest Best Practices Released by Microsoft
[5] Best practice to enforce updates on Microsoft Edge to have the latest …
[6] Secure your corporate data using Microsoft Edge for Business
[7] Deploying a Microsoft Edge security Baseline with Intune