There is no doubt PowerShell is the premier way to configure and manage things like Azure. However, there has always been a challenge actually connecting to the environment to get the ball rolling.
The first thing that you need to do to connect to Azure Resource Manager via the command line is ensure that you have PowerShell 5 installed and configured for Azure Resource Manager. This previous article of mine:
Life is far easier with PowerShell 5
which will show you how to not only configure your PowerShell environment on a Windows 2012 R2 server but also install the modules required to access Azure Resource Manager.

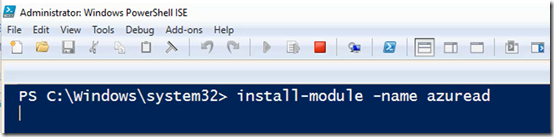
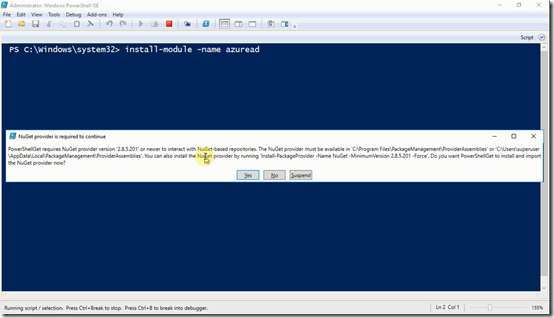
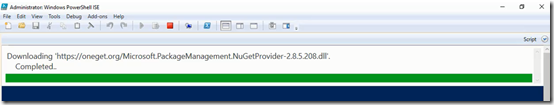
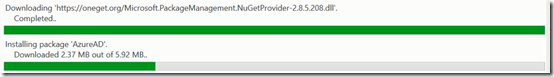
Once you have launched the PowerShell environment enter the following commands to load the ‘classic’ Azure Service Manager and the newer Azure Resource Manager modules into the session:
import-module azure
import-module azurerm

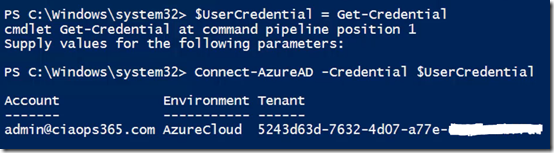
You’ll now need to login to your Azure account and in this case you’ll login to the Azure Resource Manager account using the command:
login-azurermaccount
Typically a dialog will now appear asking you to enter your Azure account login and password.

When this has been successfully completed you should details of the account echoed back to you as shown above.

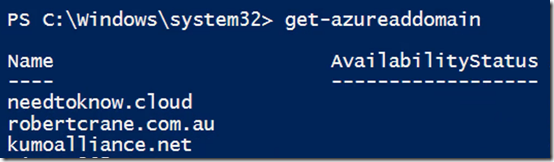
If you also want to access the ‘classic’ Azure Service Manager account issue the command:
add-azureaccount
You may need to login again with your Azure account details.
Once complete you’ll again be echoed back the details of that account as shown above.
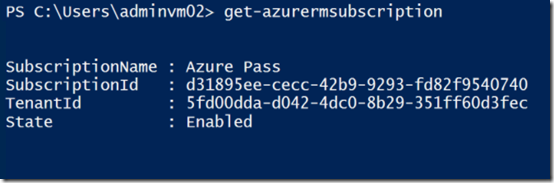
We will continue to work with the newer Azure Resource Manager here. So if you now issue the command:
get-azurermsubscription
You will see the details of the Resource Manager subscription as shown above. The important thing here is typically the subscription name (here ‘Azure Pass’). You’ll typically need to refer to the subscription by name when using PowerShell commands for Azure.

The recommendation way to do this easily is to issue the command:
$subscription=get-azurermsubscription
This will store the results of the get-azuresubscription command in a variable called $subscription.
To extract the actual name of the subscription and store it in a variable issue the command:
$subscriptionnname = $subscription.subscriptionname
In this case, the command will store the string ‘Azure Pass’ into a variable called $subscriptionname that can be used later throughout the script.

You can then issue the command:
select-azurermsubscription –subscriptionname $subscriptionname
To select the Azure Resource Manager subscription to work with (remembering that it is possible to have multiple different subscriptions inside a single Azure tenant).
You should see the Azure Resource Manager account details echoed back to you as shown above.

If you also want to target the older Azure Service Manager subscription then you should issues similar commands:
$subscriptionold = get-azuresubscription
$subscriptionnameold = $subscriptionold.subscriptionname
select-azuresubscription –subscriptionname $subscriptionnameold
as shown above.
Now you can work with you Azure tenant and PowerShell commands for both Azure Resource Manager and the older Azure Service Manager if required.
As you can appreciate with scripting and PowerShell there is lot more we can do to improve the connection experience and I’ll look to detail that in the future but this should at least get you started.