Introduction
Small and medium-sized businesses (SMBs) face the same cyber threats as larger enterprises – phishing, ransomware, business email compromise, and more – but often with fewer IT resources. Cybercriminals are increasingly targeting SMBs: over 50% of cyberattacks are aimed at small businesses, and nearly 1 in 4 SMBs experienced a security breach in the past year[7]. The consequences can be severe, with the average cost of an SMB data breach around $108K[7] and many businesses unable to operate afterward. In this context, Microsoft Defender for Office 365 (a component of Microsoft 365 security) provides essential email and collaboration protection. It comes in two plans – Plan 1 (P1) and Plan 2 (P2) – offering different levels of security features. This report compares Defender for Office 365 Plan 1 vs Plan 2, highlights the benefits of Plan 2 for an SMB environment, and provides a step-by-step guide to implementing Plan 2 to bolster security.
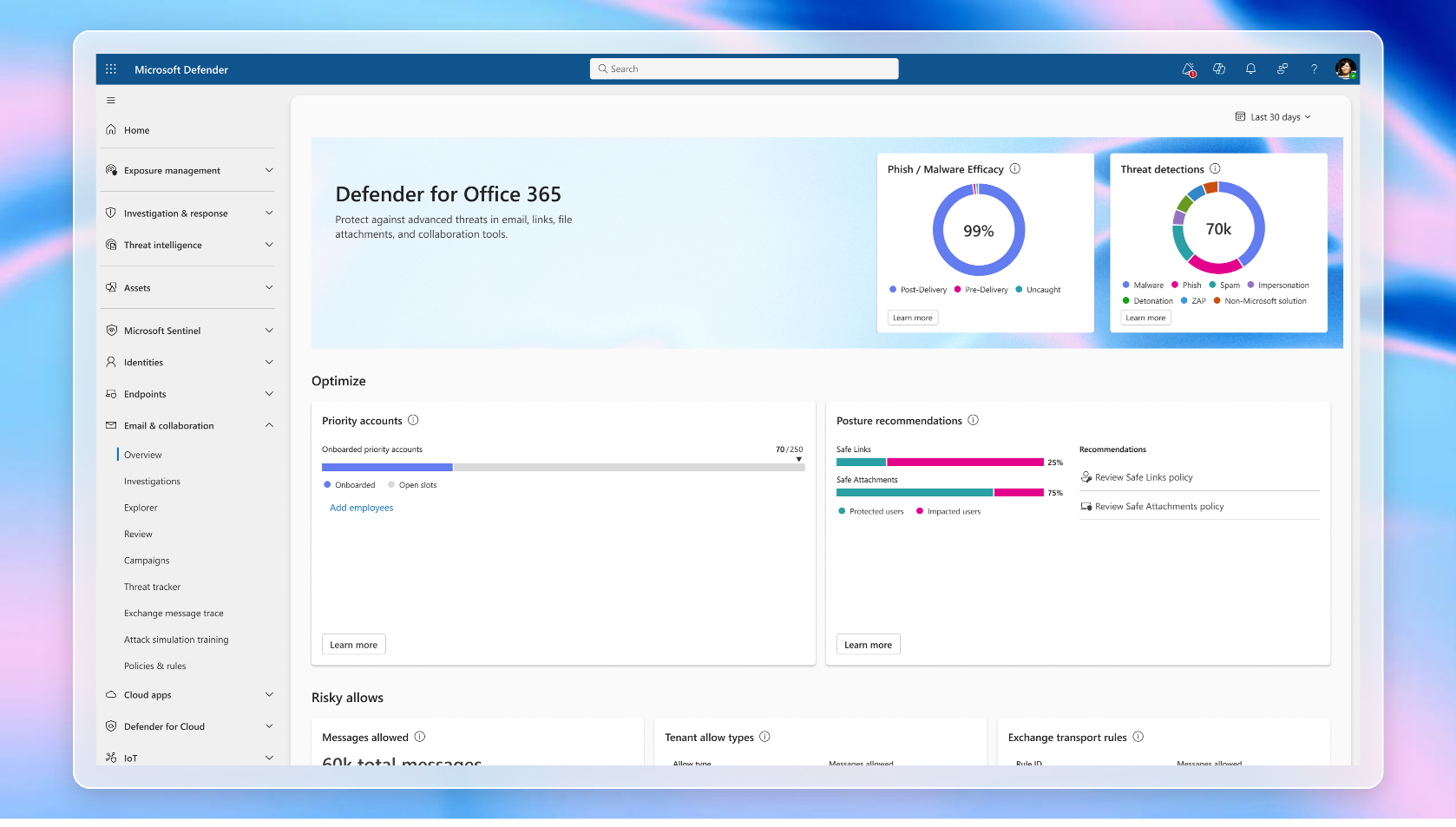
Feature Comparison: Defender for Office 365 Plan 1 vs Plan 2
Defender for Office 365 Plan 1 provides core protection for email and collaboration, while Plan 2 includes all Plan 1 capabilities plus advanced tools for threat investigation, response, and user training. Below is a comparison of key features:
-
Baseline Threat Protection (Plan 1) – Plan 1 covers the essential defensive measures:
- Safe Attachments (email attachment sandboxing) – Scans and detonate unknown attachments in a virtual environment to catch malware (Included in P1)[6].
- Safe Links (URL checking and time-of-click analysis) – Rewrites and verifies links in email or Teams to block malicious URLs (Included in P1)[6].
- Anti-Phishing Policies – Machine learning and impersonation detection to protect against phishing and spoofing (Included in P1)[3][6].
- Protection for SharePoint, OneDrive, Teams – Scans files in cloud storage and Teams for malware (Included in P1)[3].
- Real-Time Reporting and Basic Investigation – Security dashboard with real-time detections of threats (basic reporting) (Included in P1)[6].
- Preset Security Policies – Ability to use standard or strict preset security templates for easy deployment (Included in P1)[3].
-
Advanced Threat Protection and Response (Plan 2) – Plan 2 includes all Plan 1 features and adds enhanced capabilities:
- Threat Explorer & Advanced Hunting – An interactive Explorer tool to investigate threats in emails and files (e.g., search for malware/phishing across mailboxes) (Only in P2)[4]. This allows security analysts in an SMB to proactively hunt for threats and analyze the scope of attacks beyond the “real-time detections” view of Plan 1.
- Threat Trackers & Campaign Views – Insightful threat intelligence widgets and campaign views that show emerging phishing or malware campaigns targeting your organisation (Only in P2)[4]. This helps admins visualize and understand attack patterns (e.g., seeing all users targeted by the same phishing campaign).
- Automated Investigation & Response (AIR) – Automatic triggers that investigate and remediate threats. Defender can isolate emails or files, scan user mailboxes, and neutralize malware (Only in P2)[4]. This significantly reduces the manual workload and response time for an SMB IT team by handling routine threat response tasks.
- Attack Simulation Training – A built-in phishing simulation platform to run cyber-attack simulations and assign training to users based on their responses (Only in P2)[5]. This lets you send fake phishing emails to test users and then educate those who fall for them – a critical capability for building security awareness in an SMB.
- User Tags and Priority Accounts – The ability to tag users with custom labels and mark priority accounts (high-risk or high-value users like executives) for specialized monitoring (Only in P2)[5]. Priority accounts receive enhanced protection and are easier to filter in incident investigations, which is valuable if your SMB leadership or finance team is frequently targeted.
- Integration with Microsoft 365 XDR – Plan 2 ties into Microsoft 365 Defender’s extended detection and response, correlating email threats with other domains (identities, endpoints, cloud apps) (Only in P2)[4]. This is useful if your SMB uses other Defender components (like Defender for Endpoint): all alerts can be seen in one unified portal.
- Enhanced Reports and Analytics – Plan 2 provides more detailed reporting, such as detailed click trace reports (who clicked what link), and incident reporting that aggregates related alerts (Only in P2)[4]. These detailed insights help in compliance and in measuring the impact of security over time.
Summary: Plan 1 focuses on prevention – it stops phishing and malware with safe links/attachments and basic filtering. Plan 2 includes everything in Plan 1, but adds detection and response capabilities – threat hunting tools, automated response, user simulations, and deeper analytics – which provide a more comprehensive security posture.[4][6].
Benefits of Defender for Office 365 Plan 2 for SMBs
Upgrading to Plan 2 yields significant security benefits for an SMB environment, due to the advanced features described above. Key advantages include:
-
Proactive Threat Hunting & Better Visibility: With Plan 2’s Threat Explorer, security admins can actively search emails and content for indicators of compromise, rather than waiting for an alert[4]. For example, if news breaks of a specific malware campaign, an admin can quickly query if any user received related emails. This proactive stance helps find and contain threats that might have evaded initial filters. Campaign Views also aggregate all emails part of the same phishing campaign, showing which users were targeted and whether anyone clicked – invaluable context for an SMB to understand attack spread[4].
-
Faster and Automated Incident Response: Plan 2’s Automated Investigation and Response (AIR) can dramatically reduce response times. When a suspicious email is detected (e.g. a user clicks a phishing link), Defender can automatically investigate the user’s mailbox, quarantine the email across all mailboxes, and even hunt for similar messages organization-wide[4]. This automation means that even a small IT team can effectively contain threats 24/7. Microsoft notes that post-breach automated response in Plan 2 helps reduce the time and resources required to remediate security incidents[4] – a critical benefit if your IT staff wear multiple hats.
-
Security Awareness Training for Users: Human error is often the weakest link. Plan 2 includes Attack Simulation Training, which provides a safe, controlled environment to simulate real-world phishing attacks and then deliver training[4]. SMBs benefit greatly from this, as it educates employees to recognize and avoid phishing attempts. Over time, you can track improvement (e.g., fewer users clicking fake phishing emails), directly lowering the risk of a real breach.
-
Priority Protection for High-Risk Users: Plan 2 allows designation of “priority accounts” (such as CEOs, CFOs, etc.) who often are prime targets for spear-phishing[5]. These accounts get extra scrutiny (additional heuristic checks) and are flagged in reports[5], so in a security incident you can immediately see if a VIP’s account was affected. This is important for SMBs where a compromise of one key account (like the owner’s email) could be especially damaging.
-
Comprehensive Reporting and Compliance: Plan 2 provides detailed reporting on threats and user actions. SMB administrators can access reports on every malicious URL clicked by users, malware detection trends, and results of simulations[4]. These reports not only demonstrate the value of the security measures (useful for management or auditors) but also help pinpoint areas to improve. For instance, if reports show many users clicked a particular phishing link, you might conduct additional training on that attack type.
-
Integration with Broader Security Ecosystem: Many SMBs are adopting Microsoft 365 Business Premium, which includes Defender for Office 365 P1 and Defender for Business for endpoints. By moving to P2, an SMB gains XDR (extended detection & response) integration – meaning email threats can be correlated with endpoint signals, cloud app alerts, etc., in the Microsoft 365 Defender portal[4]. This holistic view is usually found in enterprise setups; Plan 2 brings it to SMBs, enabling enterprise-grade visibility into multi-faceted attacks (e.g., detecting if a phishing email led to malware on a device, and seeing that in one incident report).
-
Meeting Cyber Insurance and Regulatory Needs: As threats grow, cyber insurance and regulations are requiring stronger controls. Plan 2 features like user training and incident response automation can help satisfy security benchmarks. For example, insurers often ask if the company performs regular phishing training – with Plan 2, the answer is yes (and it’s built-in). This can potentially improve insurability and demonstrate due diligence in protecting the business.
Overall, Defender for Office 365 Plan 2 offers a layered, “defense-in-depth” approach that is particularly beneficial for SMBs that cannot staff a full security operations center. It adds readiness (through training), detection, and response on top of Plan 1’s prevention features, significantly enhancing an SMB’s security posture[4][4].
Prerequisites and Best Practices for Plan 2 Deployment
Before implementing Defender for Office 365 Plan 2, SMBs should consider licensing requirements and preparatory steps:
-
Licensing Plan 2: Ensure you have the appropriate licenses for Plan 2. Microsoft Defender for Office 365 Plan 2 is included in certain enterprise subscriptions (e.g. Office 365 E5, Microsoft 365 E5) and can also be purchased as an add-on for other plans. Notably, Microsoft 365 Business Premium (popular for SMBs) includes only Plan 1 by default[4]. To get Plan 2 features, Business Premium customers can either upgrade to an E5 Security add-on or acquire standalone Defender for Office 365 Plan 2 licenses for users. Microsoft recently enabled an “M365 E5 Security” add-on for Business Premium, which includes Defender for Office 365 P2 along with other security upgrades[4]. Best practice is to license all users who have mailboxes for Defender P2, so that threats are uniformly handled across the tenant[4].
-
Technical Prerequisites: You should have Exchange Online as your email platform (Defender for Office 365 works with Exchange Online mailboxes). If you have hybrid or on-premises Exchange, Defender can still protect cloud-delivered mail or operate in “ATP for on-premises mailboxes” mode, but most SMBs will use Exchange Online. Also, ensure that you have access to the Microsoft 365 Defender portal (security.microsoft.com) with an account that has Security Administrator or Global Administrator rights to configure policies[4]. Microsoft recommends following the principle of least privilege – assign a Security Administrator role to those who will manage Defender rather than using the Global Admin account daily[5][5].
-
Email Domain Configuration: Properly configure your email domain’s DNS records for SPF, DKIM, and DMARC before rolling out Defender for Office 365 protections. These email authentication protocols ensure that your domain’s emails are trusted and help Defender distinguish legitimate versus spoofed emails. Specifically: publish an SPF record for your domain, enable DKIM signing on your Office 365 mail, and set up a DMARC policy[5][5]. These steps (while not strictly part of the Defender product) greatly enhance its effectiveness by reducing false positives and blocking domain spoofing. Microsoft’s deployment guide lists this as Step 1 for a secure configuration[5].
-
User Preparation and Change Management: It’s wise to inform or train your users about new security measures. For example, with Safe Links, users might notice URLs in emails are rewritten and go via “safelinks.protection.outlook.com”. They should understand this is normal and for their safety. Similarly, if you plan to run Attack Simulations (phishing tests), leadership and employees should be aware that periodic simulated phishing emails will occur as training exercises. Setting expectations helps gain user buy-in and avoids confusion.
-
Policy Planning: Decide if you will use Preset Security Policies or custom policies in Defender for Office 365. Microsoft provides Standard and Strict preset profiles that bundle recommended settings for anti-phishing, Safe Attachments, Safe Links, etc., appropriate for most SMBs[5][5]. Using these presets can simplify deployment – for instance, you can apply the “Standard” protection preset to all users as a starting point. However, review the preset settings to ensure they align with your business needs (Strict is more aggressive – e.g., it may quarantine more mail). Presets can be turned on tenant-wide easily[5]. If your business has specific needs (e.g., allow certain senders, custom branding on quarantine messages), you might create custom policies instead. A best practice is to start with Standard or Strict preset for quick protection, then refine with customizations as needed, checking with the built-in configuration analyzer tool for any weaknesses[5].
-
Do a Phased Rollout (if possible): If you are upgrading from no Defender or from Plan 1 to Plan 2, consider piloting with a small group first. For example, enable the new Plan 2 features for your IT team or a subset of users, and run simulations or review the reports. This pilot can uncover any tuning needed (perhaps certain safe senders to allow, etc.) before full deployment to the whole company.
-
Have a Response Plan: Even with Plan 2’s automation, have a basic incident response plan for any serious threat that is detected (e.g., if a real attack gets through or a user falls victim). Identify who will be alerted (Defender can send alert emails), who will coordinate response, and how to communicate to the rest of the company if needed. Plan 2 provides the tools, but the organisation should still decide on human procedures for various scenarios.
By addressing these prerequisites and plans, an SMB can ensure that the deployment of Defender for Office 365 Plan 2 goes smoothly and maximizes security from day one.
Step-by-Step Implementation Guide for Plan 2 in an SMB Environment
Implementing Microsoft Defender for Office 365 Plan 2 involves configuring multiple layers of protection and utilizing its advanced features. Below is a step-by-step guide tailored for SMBs, aligning with Microsoft’s recommended deployment steps[5]:
Step 1: Configure Email Authentication for Your Domain
Objective: Strengthen the foundation of email security by setting up SPF, DKIM, and DMARC records for your email domain.
- Configure SPF (Sender Policy Framework): Publish an SPF TXT record in your DNS that lists Office 365 (and any other legitimate mail senders for your domain) as authorized senders. This helps receivers block emails that claim to be from your domain but come from unauthorized servers[5].
- Enable DKIM (DomainKeys Identified Mail): In Office 365, enable DKIM signing for your domain’s outbound emails. DKIM embeds a digital signature in headers of your messages, which recipients can verify against your public key in DNS[5]. This ensures emails aren’t tampered with and truly come from your domain.
- Publish a DMARC Policy: Create a DMARC DNS record to instruct recipients what to do if an email fails SPF/DKIM checks (e.g., quarantine or reject). Start with a monitoring policy (
p=none) and eventually move to p=quarantine or p=reject to block spoofed emails[5]. Include email addresses to get aggregate and forensic reports so you can monitor unauthorized use of your domain.
- (If applicable) ARC (Authenticated Received Chain): If your mail flows through third-party services (like a newsletter service that modifies messages), consider configuring trusted ARC sealers in Office 365[5]. This prevents those modifications from breaking the authentication chain.
- Why: These steps ensure that external recipients trust your emails and that Microsoft’s filters can better differentiate legitimate vs. forged sender addresses. It reduces false positives and leverages email authentication to complement Defender’s filtering[5].
Step 2: Apply Protection Policies (Anti-Malware, Phishing, Safe Links, Safe Attachments)
Objective: Turn on robust threat protection by using preset policies or custom settings in Defender for Office 365.
- Use Preset Security Policies: In the Microsoft 365 Defender portal, go to Email & Collaboration > Policies & Rules > Threat Policies. Choose Preset Security Policies and enable at least the Standard profile for all users (or Strict for high-security needs)[5]. The Standard preset will enforce recommended settings for:
- Anti-phishing: Impersonation protection for user and domain, mailbox intelligence, etc.
- Safe Attachments: Malware scanning with dynamic delivery (email delivered with placeholder while attachment is scanned).
- Safe Links: URL scanning on click, with URLs rewritten.
- Anti-spam & anti-malware (Exchange Online Protection default): Already enabled, but preset ensures they are at good default levels.
- These presets are off by default on new tenants until you turn them on[5]. Enable them for all recipients (you can simply choose “all users” in the wizard).
- Optional – Custom Policies: If not using presets, individually configure policies:
- Create an Anti-Phishing policy: Enable features like user impersonation protection (add your executives’ names so impersonation detection triggers), and set thresholds for SI (spoof intelligence) based on your risk tolerance.
- Create a Safe Attachments policy: Use Dynamic Delivery (so users get emails immediately and the attachment is swapped in after scanning) or Block mode for high security. Turn on Safe Attachments for SharePoint/OneDrive/Teams as well[3] (in Tenant settings).
- Create a Safe Links policy: Enable URL rewriting for email and Teams links and do not let users click through to original URL if malicious (disable the “Allow users to click through” option). You might apply this to all users; possibly use different policies for high-risk vs. standard users if needed.
- Confirm your anti-malware policy (EOP) is on – typically defaults cover virus scanning with multiple engines.
- Use Configuration Analyzer: After applying policies, use the Configuration Analyzer in the portal to compare your settings against Microsoft’s best practices[5]. It will highlight if any recommended setting is not configured, allowing you to adjust for optimal protection.
- Why: This step deploys the core defenses of Defender for Office 365, ensuring all inbound (and internal) communications are scanned and filtered. For an SMB, using presets is a quick way to get comprehensive protection without needing deep expertise, as Microsoft has pre-tuned those settings[5].
Step 3: Assign Appropriate Admin Roles and Permissions
Objective: Set up proper administration model following least-privilege principles for ongoing management of Defender for Office 365.
- Verify who in your organisation will administer security features. Assign them the Security Administrator role in Microsoft Entra ID (Azure AD) or in the Microsoft 365 Defender portal roles[5]. This role allows managing Defender for Office 365 without granting full tenant admin rights.
- Alternatively, add relevant users to the Organization Management or Security Operator roles in Exchange Online / Defender as needed[4] (Organization Management can configure all Exchange settings including security, typically for IT leads).
- Remove or avoid using Global Administrator accounts for daily security management tasks[5]. Reserve Global Admin for only critical changes. This reduces risk in case an admin account is compromised.
- If you have an external IT provider or consultant managing security, create dedicated accounts for them with Security Admin role rather than sharing credentials.
- Why: Following least privilege ensures that no single account has unnecessary access to all management functions, reducing the impact of credential theft[5]. It also allows distributing responsibilities (e.g., helpdesk can be given a role to view and release quarantined emails without giving them rights to change policies).
Step 4: Identify and Tag Priority Accounts (Plan 2 feature)
Objective: Leverage Plan 2’s Priority Account and User Tags features to protect critical users and categorize user groups.
- Determine which users are most sensitive or critical – typically leadership (CEO, CFO), accounts handling financial transactions, or IT admin accounts. These are your Priority Accounts.
- In the Defender portal, go to Settings > Email & Collaboration > Priority accounts. Add up to 250 accounts as priority accounts[5]. This tagging will highlight these users in reports and give them enhanced protection heuristics (Microsoft applies stricter filters for them behind the scenes)[5].
- Use User Tags for custom categories as needed. For instance, you might tag departments like “Finance”, “HR” or “Interns” if you want to track certain groups in the incident reports[5]. In Plan 2, you can create custom tags and assign users to them (e.g., tag all finance department users). This won’t change protection directly but helps in filtering and investigating by those tags (e.g., quickly see if any “Finance” user’s account was impacted in an attack).
- Why: Priority accounts receive extra scrutiny by Defender (since a breach of those is higher impact)[5], and they are easier to spot in threat Explorer or incident views. For a small business, this ensures your “crown jewel” accounts have an added safety net. User tags, on the other hand, are a convenience for investigations and reporting – helpful if you want to show, for example, how many phishing emails targeted the finance team versus others.
Step 5: Enable User Submissions (Report Phishing) and Train Users
Objective: Activate the mechanisms for users to report suspicious emails, and integrate this feedback into Defender for Office 365.
- Reporting Button: Ensure the Report Message add-in (or built-in “Report Phishing” button in Outlook) is deployed for all users[3]. In Microsoft 365, the add-in can be deployed via the admin center (many Outlook clients now have it by default in the ribbon). This allows users to report any email as phishing or junk with one click.
- Set up User Report Settings: In the portal, go to User Submissions settings. Configure where user-reported messages go:
- Enable sending copies of reported messages to Microsoft (for analysis and to improve filters)[5].
- Optionally, specify a mailbox to receive the reported messages (e.g., an IT or security mailbox) for internal awareness[5]. Microsoft recommends either to Microsoft only or Microsoft + mailbox so that the feedback loop is complete.
- Educate Users: Announce to employees that they should use the “Report Phishing” button any time they suspect an email. Assure them that false reports are okay – it’s better to over-report than miss a threat. Reported messages go into a special portal view for admins (“User reported” tab)[5]. This user-driven feedback helps catch threats that automated filters might allow or to quickly remove similar emails tenant-wide.
- Simulate and Train: With Plan 2, consider running an Attack Simulation campaign soon after deployment to baseline your users’ awareness. For example, run a simple phishing simulation (Defender’s Attack Simulation Training wizard has templates) targeting all users and see what percentage fall for it. Then use the built-in training modules to educate those who clicked[5]. This both raises awareness and signals to users that the company is proactive about phishing threats.
- Why: Empowering users to be part of the defense is key, especially for SMBs. The user-reported messages feature acts as an early warning system – if one person reports a phish that slipped through, Defender can immediately raise an alert and optionally start automatic investigations on that campaign[5]. Over time, as users report more, Defender’s Machine Learning also learns from that feedback. Attack Simulation Training further reduces the human risk factor by improving employees’ ability to spot malicious emails in real life.
Step 6: Fine-tune Allow/Block Lists
Objective: Learn to manage false positives/negatives by using Defender for Office 365’s Tenant Allow/Block List and submission process.
- Understand Blocking vs Allowing: Microsoft’s guidance – it’s generally safer to block specific senders or files than to create broad allows[5]. Overusing allow lists can expose your org to danger (e.g., allowing a sender could let any email from them bypass some filters)[5]. So treat allow entries sparingly and as temporary.
- Tenant Allow/Block List: In the portal (Policies & Rules section), familiarize with the Tenant Allow/Block List[5]. Here you can manually add:
- Blocked senders or domains (e.g., you might block a persistent spammer domain).
- Blocked file hashes or URLs (perhaps from threat intelligence you receive externally).
- Spoofed sender blocks or allows via the Spoof Intelligence tab[5].
- Handling False Positives (good email quarantined): If users complain about missing emails that were incorrectly quarantined, you (or they, if permitted) can release them from quarantine. Then, if needed, add the sender to the allow list via submission: In Submissions page, submit the quarantined item as “Not Junk” and choose to allow the sender/domain so future messages aren’t blocked[5]. This creates a temporary allow entry (good for 30 days by default) on Tenant Allow/Block List[5]. Avoid manually adding permanent allows unless absolutely necessary.
- Handling False Negatives (missed phish): If a malicious email got through, submit it to Microsoft via the Submissions portal or Outlook Report button[5]. When submitting, choose the option to also “Block this sender (or file or URL)” for the organisation. This will add an entry to block that content going forward[5][5]. For example, if ransomware.exe wasn’t caught by scanners, submit it and block its file hash so it won’t hit others.
- Regular Review: Periodically review the Tenant Allow/Block List for any entries that can be removed (e.g., a 3-month-old allow for a vendor that has since fixed their emailing system might be removed). Also review Spoof Intelligence insight page[5] – it will show if someone attempted to spoof your domains or send as your users, and you can one-click block those senders.
- Why: Properly managing these lists helps maintain a balance between security and business continuity. SMBs can’t afford to have important client emails lost, but also can’t allow threats in. This step ensures you have a process to quickly unblock legitimate mail or stop a new threat, using Defender’s built-in tools[5][5].
Step 7: Launch Phishing Simulation Campaigns (Attack Simulation Training)
Objective: Utilize Plan 2’s Attack Simulation Training to improve user resilience against phishing.
- Navigate to Attack Simulation Training in the Defender portal (under Email & Collaboration). Use the wizard to create a phishing simulation:
- Choose a realistic phishing template (e.g., an Office 365 login page lure or a fake package delivery email – there are many presets).
- Target a group of users or all users. It might be wise to start with all users for a baseline, since SMBs might have manageable numbers.
- Schedule the simulation or launch it immediately. Plan 2 allows running multiple simulations and even automation (e.g., periodic campaigns that automatically harvest real threat payloads)[5], but to start, one campaign is fine.
- Ensure “payload” (the link or attachment) is something safe but trackable (the built-in ones are).
- Once the simulation runs, monitor results in real-time. See which users clicked the link, entered credentials (the system does not actually steal their password; it just records the attempt), or reported the email.
- After it concludes, assign the relevant training modules to users who fell for it[5]. Defender Plan 2 has training experiences (videos, quizzes) covering why that phishing email was convincing and how to avoid it next time. The platform can automatically send training links to those users.
- Repeat simulations regularly (e.g., quarterly). Use varying templates – perhaps an attachment-based phishing next, or a different theme – to cover different attack types. Over time, track the improvement metrics: ideally, with each campaign, the “click rate” goes down.
- Why: Simulated phishing campaigns are one of the most effective ways to vaccinate your users against real attacks. By experiencing harmless test attacks, users learn to spot red flags. Microsoft data shows Plan 2’s simulation training provides SMBs a safe environment to train employees in recognizing phishing attempts[4]. This is an invaluable layer of defense – technology alone is not enough if an employee is fooled; training reduces that likelihood.
Step 8: Monitor, Investigate, and Respond to Threats Continuously
Objective: Use Defender for Office 365 Plan 2’s ongoing detection and response capabilities to maintain security over time.
- Secure Score and Dashboard: Check your organisation’s Microsoft Secure Score and Threat protection status in the security center dashboard. Secure Score will give you a numerical rating of your security posture and recommend improvement actions (many of which you might have done by deploying Plan 2 features). Aim to maximize the score relevant to email & collaboration security.
- Real-Time Detections/Incidents: The Defender portal will aggregate alerts into Incidents. For example, if a user opens a malicious file and later fails a login – these could be linked. For email, if multiple phish are detected, it might form one “phishing campaign” incident. Regularly review any active incidents or alerts. For an SMB, it’s good practice to check the portal at least daily (or ensure alert emails are going to an admin mailbox that is monitored). With Plan 2, many incidents will show an Automated Investigation running or completed[4]. Review the results: e.g., an investigation might say “X malicious emails removed from 5 mailboxes”. Verify that and mark incident as resolved once done.
- Threat Explorer: Make use of Threat Explorer (also called Explorer or Real-Time detections in UI) to investigate as needed. For instance, if you hear about a new virus via news, you can search for that file name or hash in Threat Explorer across Exchange, SharePoint, etc. Or if you suspect a user account might be compromised (maybe sign-in risk alerts from Entra ID), use Explorer to see all mail sent from that account or unusual inbox rules (some phishing attacks create auto-forward or delete rules – those can be seen in Explorer under “Rule” events). Hunting Queries: Optionally, Plan 2 allows writing or running queries (similar to advanced hunting) for email traces. This is more advanced but can be valuable for deeper forensics if needed.
- Responding to Incidents: When a real threat is confirmed – use Plan 2 tools to respond:
- If a malicious email is identified, use Explorer or Content search to find all instances of it and then Detonate or Soft-delete those messages from mailboxes.
- If indicators are found (malicious URL or attachment), add them to block lists (Step 6 above).
- If a user fell for a phishing link and entered credentials, trigger a password reset for that user immediately and investigate if their account sent out more phish.
- Use Automated Investigation results as a guide – they often recommend actions. For example, the automation might quarantine emails but leave it to you to confirm and permanently delete them – follow through on those.
- Maintain and Update Policies: Periodically re-evaluate your policies. As your business evolves, you may tighten policies (e.g., move from Standard to Strict preset if threat landscape worsens) or adjust whitelists/blacklists. Also stay informed via the Message Center in Microsoft 365 Admin – Microsoft often announces new Defender features or changes. For example, new rule toggles or improvements might be released; adopting them can improve protection.
- Monthly Review Meetings: It may help to have a monthly (or quarterly) security review within your team. Go over reports like Top Malware Detections, Phishing emails blocked, User simulation performance, etc. Identify if additional training is needed or if certain departments are being targeted more. This is essentially treating security as an ongoing cycle: Deploy > Monitor > Improve.
- Why: Consistent monitoring and quick response ensure that Plan 2’s features are effectively used. The solution provides detailed alerts and even automatic fixes for many issues, but human oversight is still required to verify and to handle the edges. By actively using the tools (Explorer, Incidents, reports), an SMB can stay on top of threats and continuously harden their environment. Microsoft emphasizes that after initial setup, admins should “monitor and investigate threats in the organisation” using the Security Operations Guide[5] – this step is about practicing that on an ongoing basis.
By following these steps, an SMB can methodically deploy Microsoft Defender for Office 365 Plan 2 and integrate it into their security operations. The result is a multi-layered defense system: secure configuration of the email ecosystem, robust threat filtering, educated users, and rapid response to any incidents – all tailored to fit the limited resources but significant needs of a small/medium business.
Integration with Existing Security Measures
Defender for Office 365 Plan 2 is one component of a broader security strategy. In an SMB environment, it’s important to integrate Plan 2 with other security measures in place:
-
Email Filter Co-existence: Some SMBs might have an existing third-party email security gateway or spam filter (e.g., Proofpoint, Mimecast) in front of Office 365. Plan 2 can complement or even replace these. Microsoft generally recommends using Defender for Office 365 as the primary protection to take full advantage of its capabilities. However, if you choose to keep a third-party gateway (for a “defense in depth” approach), be sure to configure connectors and skip-listing properly so that the third-party filtered email still goes through Defender’s scanning without interference. Microsoft provides a “Configure defense in depth” guide for running Defender behind another gateway[4]. Key is to avoid double-marking of emails. For example, you’d want to disable Safe Links rewriting if the other gateway already rewrites links, or vice versa. Carefully consider if maintaining two solutions is necessary – many SMBs consolidate to Plan 2 alone, reducing complexity and cost.
-
Endpoint Security Integration: Plan 2 is part of the Microsoft 365 Defender suite, which includes Defender for Endpoint (for device protection), Defender for Identity (for on-prem AD threat detection), and Defender for Cloud Apps. If your SMB uses Microsoft Defender for Endpoint (MDE) on Windows/Mac devices (for example, via Microsoft 365 Business Premium’s Defender for Business), the signals from Plan 2 and MDE will feed into a unified incident queue in the Microsoft 365 Defender portal[4]. This is a powerful integration: if a user clicks a malicious email and that leads to malware on their PC, the email alert and the endpoint alert will be correlated as one incident. Ensure that you onboard devices to Defender for Endpoint and verify in the portal that incidents show data from both Email and Device. Plan 2’s XDR integration essentially bridges email and endpoint, so you get a cross-domain view of attacks[4].
-
Identity and Access Management: Security is not just about content scanning. Make sure you also have strong identity security, which works hand-in-hand with Plan 2. Enable Multi-Factor Authentication (MFA) for all users (this is perhaps the single most effective measure to prevent compromised accounts via phishing). Use Conditional Access if available (requires Azure AD P1/P2) to block risky sign-ins. These measures ensure that if a password is phished via email, the attacker still can’t easily use it. Plan 2 can send alerts if it sees anomalous behavior (e.g., impossible travel logins if integrated with Identity protection), strengthening overall security.
-
Data Loss Prevention (DLP) and Compliance: While Plan 2 focuses on threat protection, consider setting up DLP policies in Office 365 to prevent sensitive data leaks (like SSNs or credit card numbers being sent out via email). This guards the outbound side. Also, Office Message Encryption can be used if sending confidential info externally – ensure it’s configured (Business Premium includes basic Office 365 encryption features). These are security controls that complement Plan 2 by addressing data protection rather than threat protection.
-
Security Information and Event Management (SIEM): If your SMB uses a SIEM like Microsoft Sentinel or another logging system, you can integrate Defender for Office 365 with it. Plan 2 allows API access and alert forwarding. For instance, you could forward Defender alerts to Sentinel or to an IT service management tool to ensure nothing is missed. Many SMBs might not have a SIEM, but for those who do (perhaps via an IT provider or MSSP), integration ensures Plan 2 events are part of centralized logging and compliance.
-
Third-Party Services: There might be other security layers – for example, endpoint antivirus (if not using Defender for Endpoint), firewall and network security appliances, backup solutions. While those don’t directly integrate with Plan 2, your overall security procedures should consider them. For example, ensure that if Plan 2 identifies a malware outbreak, you also scan endpoints with your AV. Or if ransomware is detected, verify backups. Essentially, use Plan 2 alerts as triggers to check other systems. You can also import threat intelligence from other sources into Plan 2’s block lists (step 6 above) – e.g., if your firewall vendor shares an IoC (indicator of compromise) list of malicious URLs seen, you could add those to Defender’s blocked URLs.
-
User Experience Considerations: Integration is also about making security seamless. For instance, if you have an internal Teams or Slack channel for security alerts, you might set up email notifications from Defender to post there. Or integrate Defender with a ticketing system so that when an alert arises, an IT ticket is created automatically. These process integrations ensure that Plan 2 becomes a well-oiled part of your IT operations.
In summary, Defender for Office 365 Plan 2 should not be viewed in isolation. It works best when combined with strong identity protection (MFA), device protection (Defender or other AV), and good IT policies. The good news for SMBs is that Microsoft 365 Business Premium, in particular, provides a cohesive suite – pairing Plan 2 (via an add-on) with Defender for Endpoint P2, Azure AD P2, etc., essentially brings an enterprise-grade security stack within reach of an SMB[4]. Integrating these components yields a comprehensive security posture: email threats blocked, compromised devices isolated, and suspicious user activities flagged, all under one roof.
Monitoring, Maintenance, and Effectiveness Evaluation
Deploying security controls is not a one-time project – it requires ongoing monitoring and maintenance to remain effective. For SMBs using Defender for Office 365 Plan 2, here’s how to ensure the solution continues to deliver strong protection and how to evaluate its effectiveness over time:
-
Continuous Monitoring: As covered in Step 8 of the implementation guide, it’s critical to keep an eye on the Defender security portal or set up alerting. Make sure alert notifications in Defender for Office 365 are configured to email or text the admin (or MSP) for high-severity incidents (like multiple infections or detected compromised accounts). The sooner you know about an issue, the faster you can act. Many SMB breaches occur not because defenses failed, but because an alert was missed until too late. With Plan 2, take advantage of the central Incidents queue and consider enabling the 24/7 alerting feature (if available) where Microsoft can even call your phone for the most critical alerts (this is optional, often reserved for severe incidents).
-
Regular Policy Audit: Every few months, review your policies and rules. Things to check:
- Quarantine configuration: Are users allowed to self-release emails from quarantine? (By default, end users can get quarantine summaries and release false positives unless you restrict it.) Decide if this is working or if too many false releases happen – you might tighten or loosen accordingly.
- Safe Links and Attachments: Review if any users or groups are exempted from these policies (perhaps done for testing) and ensure none remain inadvertently unprotected.
- New features: Microsoft frequently updates Defender. For instance, they might introduce a new setting like “Tenant Allow/Block for files in Teams” or enhancements to detection algorithms that can be toggled. Stay aware via the Microsoft 365 Message Center or the Defender for Office 365 blog[3] and incorporate new best practices.
- Licence count: If your organization grows, ensure new users are licensed for Plan 2 and receive the same protections (license management can be a form of maintenance too!).
-
False Positive/Negative Tuning: Track if users are experiencing any pain from the security – e.g., important emails landing in quarantine often (false positives), or conversely, if any spam/phish are leaking through (false negatives). Use the submission data and user feedback. For repeated false positives from a known partner, you might add a domain to the Allowed senders list (with caution as noted). If users report they’re getting phishing emails regularly, check if something is misconfigured (perhaps those emails are newsletters with bad links that trigger Safe Links – if legitimate, maybe add to allow). Regularly checking quarantine and user submissions can reveal patterns to tweak. Aim for a balance: maximum security with minimal disruption. Plan 2’s rich data should help pinpoint what needs adjustment.
-
Metrics to Evaluate Effectiveness: To justify and evaluate Plan 2’s value, look at measurable outcomes:
- Threats Detected/Blocked: Use the Reports section in the Defender portal. For example, check the Threat Protection Status report, which shows how many emails were malware, phish, etc., and were blocked. If, say, 500 phishing emails were blocked last month, that’s 500 potential incidents avoided – a clear benefit. You can track this month over month.
- User Resilience: Monitor the results of Attack Simulations. If initially 30% of users clicked a simulation link and after training it’s down to 5%, that’s a major improvement in security culture (and reduces real risk). Plan 2’s detailed click reports[4] mean you can even see if any user clicks malicious links in real emails – if zero successful phishing-related account compromises occur over a year, that’s a good indicator of efficacy.
- Incident Response Time: With Plan 2 automation, measure how quickly issues are resolved. For instance, when a real phishing incident happened, how long did it take from alert to containment? Ideally, Plan 2’s automation plus your admin action should neutralize threats within minutes or hours, not days. If you have historical data from before Plan 2 (maybe when using manual processes or no advanced tool), you might see a reduction in response time.
- Secure Score Improvement: If you started with a lower Microsoft Secure Score and after deploying Plan 2 and related features your score climbed (e.g., from 30% to 85%), it quantifies improved posture. Secure Score will specifically count things like “User training simulations enabled” and “Safe attachments policy configured” as points.
- Reduction in Successful Breaches or Losses: Ultimately, the best metric is the lack of a successful attack. If your company hasn’t experienced a serious email-borne security incident since Plan 2 implementation, that is evidence of success (though it can be hard to prove causation, the correlation is strong when filtering and training are robust). Some organisations calculate $ ROI of security tools by estimating how many breaches were prevented. Microsoft even published a Total Economic Impact study for Defender for Office 365 that showed reduced likelihood of breaches and cost savings due to automation[3]. For an SMB, even preventing one $50k wire fraud or one ransomware infection can justify the investment in Plan 2 many times over.
-
User Feedback: Check in with users periodically. Are they finding the Safe Links and Safe Attachments experience acceptable? (Usually it’s seamless, but if users complain about delayed emails due to scanning, you can investigate if Dynamic Delivery is configured properly, etc.) Are users more confident knowing suspicious emails get caught? Sometimes the cultural impact – users feeling safer – is a soft benefit. Make sure, however, users aren’t developing complacency (“the system catches everything, so I might click anyway”). Continue to remind them that technology is one part and their vigilance is the other.
-
Update Training and Awareness: Cyber threats evolve, and so should your training. Use the content updates provided in Attack Simulation Training – Microsoft adds new templates reflecting current real-world lures. Also, share newsletters or tips with staff when you see new trends (e.g., “There is a surge in fake invoice scams this quarter – be extra careful with any invoice emails. Our systems are monitoring, but stay alert and report anything suspicious.”). Keeping security in the conversation maintains a security-conscious culture, amplifying the effect of Plan 2’s technical controls.
By maintaining diligent monitoring and being metrics-driven in evaluating Plan 2’s performance, an SMB can ensure they are getting the most out of their security investment and continuously adapting to the threat landscape. The goal is that over time, incidents become rarer, and the organisation’s confidence in its security grows – all while knowing that if something does happen, the tools are in place to quickly mitigate it.
Challenges and Mitigations in Plan 2 Implementation
Implementing advanced security like Defender for Office 365 Plan 2 in an SMB can come with some challenges. Anticipating these and planning mitigations will lead to a smoother experience:
-
Challenge 1: Initial Configuration Complexity – Plan 2 has many features and settings, which can be daunting for a small IT team during setup. Misconfiguring a policy could reduce protection or cause user friction.
- Mitigation: Leverage Microsoft’s Setup Guides and Best Practices[4]. The Defender for Office 365 setup wizard can auto-configure recommended policies if you’re unsure. Start with Preset policies (Standard/Strict) to cover everything broadly. You can also engage a Microsoft partner or utilize Microsoft’s FastTrack (if eligible) for guidance. Always test new policies with a small group before deploying company-wide to catch misconfigurations.
-
Challenge 2: False Positives Impacting Business – Aggressive filters might quarantine valid emails (e.g., a safe attachment being sandboxed, causing a slight delay, or a legitimate domain getting flagged for phishing). If users or management perceive that security is “getting in the way” of business, they may push back.
- Mitigation: Fine-tune gradually. Use “Monitor” modes where available – for example, an anti-phishing policy can be set to audit (just tag the email) before enforcing full quarantine. Review quarantine daily especially in the early weeks to release any good mail and train the filters (via user Submissions)[5]. Build an Allow list for known partners/newsletters only if absolutely needed, and prefer using spoof allow (for domains you trust that often get spoofed) rather than blanket safe sender allows. Communicate to users that they should check their quarantine notifications – educate them on how to self-release emails if that’s enabled. By addressing false positives quickly and adjusting policies (using the Tenant Allow/Block list as needed[5]), you can minimize business disruption. Over time, as Defender’s machine learning learns your mail flow (and you add necessary exceptions), false positives typically drop.
-
Challenge 3: User Resistance to Phish Simulations or New Protocols – Some users (or even managers) might feel the phishing tests are a “gotcha” tactic or be embarrassed by failures. Others may ignore the training assignments. Additionally, changes like mandatory MFA or new login flows due to Safe Links could initially confuse users.
- Mitigation: Leadership endorsement and positive framing are key. Explain to everyone that the simulations are there to help, not to punish – “just like a fire drill, it’s practice to keep us safe”. Emphasize that results are used to improve training, not to single out individuals (keep results reasonably private or only share department-level scores rather than naming and shaming). Perhaps even gamify the process: reward teams with the best phishing test performance or most improved rates. For other changes, provide user guides or internal brown-bag sessions about the new “Report Phish” button or why a link they click now opens with a safe redirect. This reduces confusion and makes users partners in security, rather than adversaries of the new system.
-
Challenge 4: Limited IT Manpower for Ongoing Management – A small IT department might struggle to regularly review all the alerts, incidents, and logs that Plan 2 generates, potentially leading to oversight of important signals.
- Mitigation: Take advantage of automation and prioritization. Plan 2’s automated investigations already take care of many issues – trust them to handle the noise. Configure notification rules so that only high-severity or specific alerts page your team. For example, you might set an alert when Auto-Remediation fails or when user clicks on a confirmed phish link, rather than every single spam quarantine event. Additionally, consider using a Managed Service Provider (MSP) or Microsoft’s own
Threat Experts service (if available for SMB) for additional monitoring – some SMBs outsource Tier-1 security monitoring to an external SOC. Within the team, assign clear responsibilities (e.g., who checks the dashboard each morning). Using the Secure Score as a guide can also focus efforts on what to improve next instead of wading through raw logs.
-
Challenge 5: Keeping Pace with Updates and Threat Landscape – Cyber threats evolve quickly. A tactic that was not caught today might appear tomorrow. SMBs might not have dedicated security analysts to track these trends or new features in Plan 2.
- Mitigation: Microsoft helps by continuously updating Defender’s backend with new threat intelligence (so many new threats are addressed automatically via cloud updates). To keep up on your side: subscribe to the Microsoft Defender for Office 365 blog or Community for announcements. Set aside time monthly to read Microsoft’s summary of recent changes or upcoming updates (Message Center). Also, consider joining an industry ISAC or a security mailing list oriented to SMBs – sometimes, peer insights can alert you to scams hitting local businesses, which you can then watch for in your org. The good part is Plan 2 includes Threat Trackers – use those in the portal; they often highlight current top phishing themes or malware impacting organizations globally, which is like built-in threat intel at your fingertips[4]. You can then verify if those are seen in your tenant.
-
Challenge 6: Licensing Costs – Upgrading to Plan 2 or adding E5 Security licenses does incur additional cost, which might strain an SMB’s IT budget if not anticipated. Decision-makers might question the ROI if they haven’t yet seen a breach.
- Mitigation: Build a strong business case using some data and the features Plan 2 provides. Emphasize the cost of a potential breach or business email compromise (which can easily be five or six figures, not to mention reputational damage) versus the subscription cost of Plan 2. If available, leverage any trial periods – Microsoft often allows a 30-day trial of E5 which includes Plan 2; use that to demonstrate value (e.g., show leadership how many threats were caught in just one month of trial). Also mention that Plan 2 is part of Microsoft 365 E5 Security add-on which also upgrades other areas (like Endpoint P2, Identity P2)[4], so it’s a comprehensive security uplift, not just email. Many SMBs find that consolidating on Microsoft’s security stack (instead of multiple point products) can even save money in the long run[4].
By recognizing these common challenges and proactively addressing them, you can ensure that deploying Defender for Office 365 Plan 2 is a net positive experience for your organisation. With thoughtful tuning and user engagement, the robust security gains far outweigh the initial hurdles.
Resources for Ongoing Support and Training
SMBs implementing Plan 2 have a wealth of resources available to help maintain and improve their security posture:
-
Microsoft Learn Documentation: Microsoft provides extensive official documentation and step-by-step guides for Defender for Office 365. The “Get started with Microsoft Defender for Office 365” guide is highly useful for initial setup[4], and there are specific docs for managing Safe Links, Safe Attachments, Attack Simulator, etc. Keep the Microsoft Learn links handy for reference whenever you need to adjust a setting. Relevant docs include: “Microsoft Defender for Office 365 service description” (feature list)[3], “Set up Safe Attachments policies”, “Safe Links in Office 365”, and “Attack simulation training in Office 365”. These are updated by Microsoft as the product evolves.
-
SMB Security Guide: Microsoft has published a Practical Guide to securing SMBs with Microsoft 365 Business Premium[2] (often available via aka.ms/smbsecurityguide). This guide, and an accompanying checklist[1], covers a holistic security approach – including enabling Defender for Office 365 P1/P2, plus device security, identity, and data protection. It’s essentially a blueprint for partners and IT admins in the SMB space. It can ensure you didn’t miss any important configuration and provides rationales for each step. Using the checklist (aka.ms/smbsecuritychecklist) you can periodically audit your setup against best practices.
-
Admin Training and Certifications: If you or your team want to deepen your knowledge, Microsoft offers free training modules on Microsoft Learn for security administration. There is even a certification (SC-200: Microsoft Security Operations Analyst) that covers Microsoft 365 Defender components, including Office 365 Defender – pursuing such structured learning can strengthen your skills in using Plan 2 effectively. Microsoft Virtual Training Days or webinars specifically often have sessions on Defender for Office 365 – keep an eye out for those.
-
Community and Support Forums: The Microsoft Tech Community has an area for Defender for Office 365 where Microsoft engineers and experts often post blogs or answer questions. It’s a good place to seek advice for peculiar scenarios or see how others are using the product. Similarly, forums like Stack Exchange (Server Fault) or even Reddit (r/Office365) see discussions on issues/solutions – sometimes you’ll find that someone has already asked a question that you’re facing. Always verify info from community with official docs, but it’s a useful supplement. For official support, if you face an issue (like something not working as it should), remember that Microsoft 365 support is included in your subscription – you can open a support ticket from the admin center; Microsoft’s support can assist with troubleshooting or confirming if an issue is a known bug.
-
Microsoft 365 Lighthouse (for MSPs): If your SMB’s IT is managed by a partner or if you are an MSP handling multiple SMB tenants, Microsoft 365 Lighthouse is a tool specifically designed to manage security across multiple Business Premium tenants. It highlights security issues across customers, including threats discovered by Defender for Office 365, in a unified portal. This can greatly aid partners in supporting SMBs at scale (ensuring none of their clients slip through the cracks security-wise). If you are an SMB without an MSP, Lighthouse wouldn’t directly apply, but it’s good to know if you consider using a partner’s services.
-
User Training Materials: For end-user education, Microsoft provides some ready-made resources. Apart from the Attack Simulation Training content, you can find PDFs or videos in the Microsoft Security Awareness Toolkit. There are email templates, posters, and tips you can circulate to users. Keep security awareness alive by occasionally sharing a one-minute “Did you know?” about phishing or safe computing. The more users hear it, the more it sinks in.
-
Staying Updated on Threats: To keep security top-of-mind, subscribe to alerts from organisations like US-CERT or SANS for any major new email threat campaigns. While Plan 2 will likely catch new threats, knowing about a big wave (e.g., a COVID-19 themed phishing wave) lets you warn your users to be extra careful even before any phish might hit their inbox. Microsoft’s Security Intelligence Reports and the Defender for Office 365 Threat Analytics (if enabled) are also good ways to understand emerging threats.
-
Periodic Microsoft Services: Microsoft occasionally offers free security assessments or workshops for eligible customers (sometimes via partners). For instance, an Email Threat Assessment might be offered, where they analyze your last X days of mail for latent threats. Check with your Microsoft account rep or partner about such programs – they can provide insight and tune-ups that complement your own efforts.
In summary, you are not alone in maintaining your security – Microsoft and the security community provide ample support. By regularly consulting these resources, you can keep your Defender for Office 365 Plan 2 deployment optimized and stay ahead of new threats. As threats evolve, so do defenses, and continuous learning is part of the journey. Given the robust capabilities of Plan 2 and the support around it, even a small IT team can effectively protect an SMB environment at a level that rivals enterprise security, creating a safer environment to conduct your business.
References
[1] Module 02 – Security v2.0
[2] PracticalGuideToSecuringWorkFromAnywhereUsingMicrosoft365BusinessPremium
[3] Microsoft Defender for Office 365 service description
[4] Microsoft 365 E5 Security is now available as an add-on to Microsoft …
[5] Get started with Microsoft Defender for Office 365
[6] MS-900T01A-ENU – PowerPoint_03
[7] Microsoft SMB Briefings Partner Presentation deck_August 2023