I’ve talked about the
CIAOPS Cyber protection model
before and you can see it above.

Now it is time to start applying it directly to Microsoft 365 to help understand the security Microsoft 365 provides and what can be configured to provide enhanced security.

I’ve therefore started by breaking the Email connector from my model into two components, Inbound and Outbound, as shown above. The left hand side (outside the box) is the Internet, while inside the box on the right hand side, is Microsoft 365.
Outside the box, on the Internet, there are three user configurable items: SPF, DKIM and DMARC. You’ll see arrow from these three items away and further into the Internet as well as back into the Microsoft 365 service. This is because these three DNS records will affect both sent and received emails and should be considered the first item on your email security check list. Some articles that may help on this include:
SPF, DKIM, DMARC and Exchange Online
Set up SPF to help prevent spoofing
Support for validation of DKIM signed messages
Use DKIM to validate outbound email sent from your custom domain
Use DMARC to validate email
When others send email to Microsoft 365, the following articles may help:
Sending mail to Microsoft 365
Services for non-customers sending mail to Microsoft 365
Inbound email is received into Microsoft 365 via Exchange Online. A component of this service is Exchange Online Protection (EOP).
Exchange Online Protection overview
EOP features
Inbound emails
The first stage of a message progressing through Exchange Online Protection is for it to traverse the Edge Protections as shown above. These are basically policies and configuration managed and maintained by Microsoft. A user is unable to alter them but information about these can be found at:
Use Directory Based Edge Blocking to reject messages sent to invalid recipients
Backscatter in EOP
How EOP validates the From address to prevent phishing
It is important to note that DNS records like SPF play an important role in helping secure email data, which is why it is important to configure them.
How Microsoft 365 uses Sender Policy Framework (SPF) to prevent spoofing
After the Edge Protection phase is complete, any inbound email is then sent to Exchange Online Protection (EOP) for further processing. It is here that there are many policies and settings that can be configured by the user. The sequence in which these take place can be found here:
Order and precedence of email protection
Generally, first to be processed is the Connection filtering.
Configure connection filtering
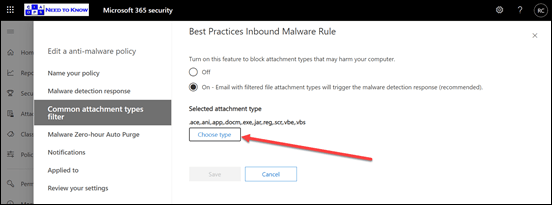
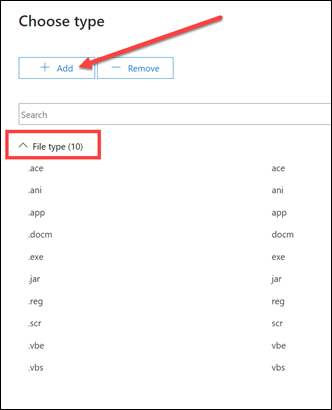
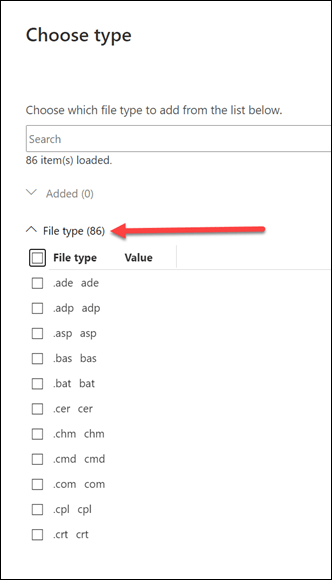
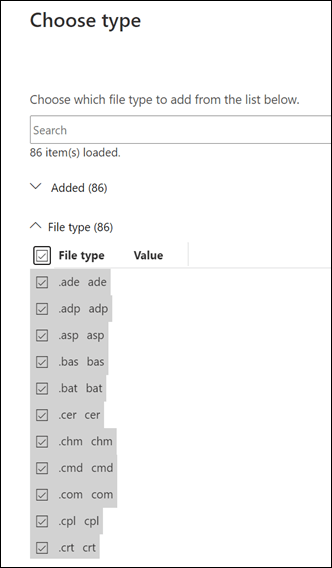
Then Malware filtering.
Configure anti-malware policies in EOP
Then Transport rules.
Mail flow rules (transport rules) in Exchange Online
Next are any Data Loss Prevention (DLP) policies.
Data Loss prevention
Spam filtering follows.
Anti-spam protection in EOP
Configure anti-spam policies in EOP
Anti-spam message headers in Microsoft 365
Bulk complaint level (BCL) in Exchange Online Protection EOP
Finally inbound email will be checked for phishing and spoofing.
Anti-phishing policies in Microsoft 365
Configure spoof intelligence policy
After all these the inbound email will continue to be processed by any additional protection options and features like Defender for Office 365 which will be covered in an upcoming article, so don’t think that email protection stops with EOP, it continues with Defender for Office 365 right through to the email app on the device which will all be covered in upcoming articles.
Outbound emails
If we now turn our attention to outbound emails and work from right to left, along the bottom arrow, we see that the email has a lot less policies to travel through. The main one is the Outbound spam filter.
Configure outbound spam filtering in EOP
However, it will also go through the DLP policy:
Data Loss prevention
and then Transport rules:
Mail flow rules (transport rules) in Exchange Online
You can also use
Message Encryption
if you wish to protect the contents of emails sent from Microsoft 365.
Summary
Remember, what is covered here is only the first part of the full range of protection capabilities that Microsoft 365 provides for emails. You will also see that a significant amount of these capabilities provide the ability of customisation. For the items that are user configurable in the diagram, a good rule of thumb is to implement and configure from left to right, top to bottom. Once you have all that done, then you can move onto the next stage which will be covered in the next article on this topic.
End to End email protection with Microsoft 365 – Part 2