After a recent incident, I decided that it would be a good idea to have an EntraID app that I could use to re-enable a users inside a tenant if I needed. I have previously detailed how to do this manually:
Create an EntraID app to allow user enablement
I’ve now created a script you can use to accomplish this which you will find here:
https://github.com/directorcia/Office365/blob/master/eid-resetapp-set.ps1
Let me walk your through its operation:
You’ll need to ensure the Microsoft Graph PowerShell module is installed in your environment.
The new EntraID app will be called ‘Reset’ by default but you can change that by changing the variable $appname in the script.
The first thing the script will do is connect to the Microsoft Graph using the appropriate scopes or permissions. Typically you will need to login to your tenant with an administrator account because an new EntraID app needs to be created.
Next, the script will use the new-mgapplication command to create a new EntraID app in your environment. It will then use the add-mgapplicationpassword command to set a password for that app.

The script will now display all the important details about the EntraID app just created on the screen which you need to record for later use. Again, write this stuff down!
The script will now build the appropriate API permissions required for the EntraID app which are:
– User.EnableDisableAccount.All
– User.ReadWrite.All
– Directory.ReadWrite.All
These are required by the update-mguser command detailed here:
https://learn.microsoft.com/en-us/powershell/module/microsoft.graph.users/update-mguser?view=graph-powershell-1.0#description
The script now uses the command update-mgapplication to add these API permissions to the new EntraID app.

It then builds a consent URL and copies that to the clipboard. This consent URL you will need to past into a browser and click Accept. The consent URL is also displayed on the screen so you can copy and paste from there if needed.
I have not been able to get this consent function working inside my script. I aim to keep working on that but for now you’ll need to use the browser to consent to the permissions. If anyone know how to do this please let me know as I can’t get it to work.

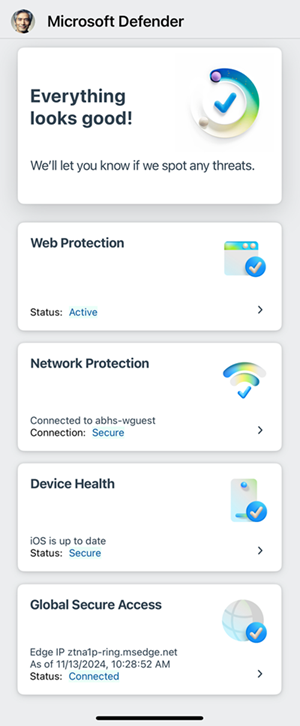
If you look inside your EntraID application you should now see one called ‘Reset’ with the appropriate API permissions consented to as shown above.
The completed script output should look like:

You should now be able to follow these instructions:
Using PowerShell to allow user enablement
to gain access if needed to enable a user, but don;t forget to save the credentials that this script produces for later use.