In my article
Moving to the Cloud – Part 2
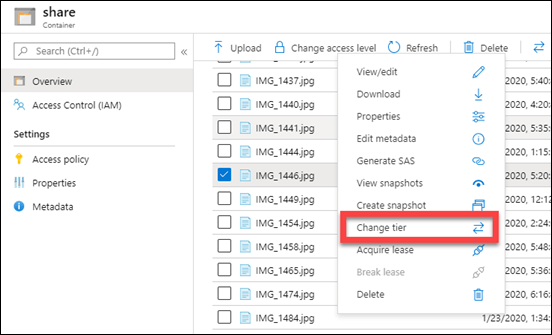
I spoke about using Azure Archive storage as a good location for long term data retention. The way that you configure this is basically to set up a storage account as usual and initially configure it as ‘Cool’ storage (since you can’t do Archive storage directly). You then upload files there (typically using Azure Storage Explorer). The final piece of the puzzle is to change the access tier from ‘Cool’ to ‘Archive’ by right mouse clicking on the item.
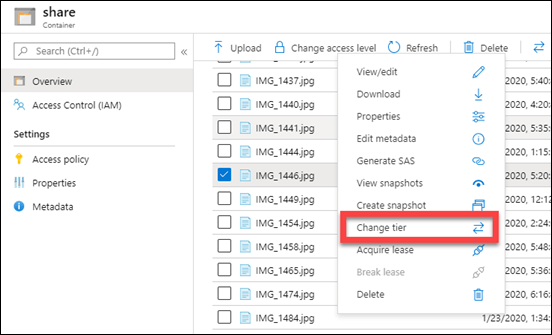
You can do the same using Azure Storage Explorer.
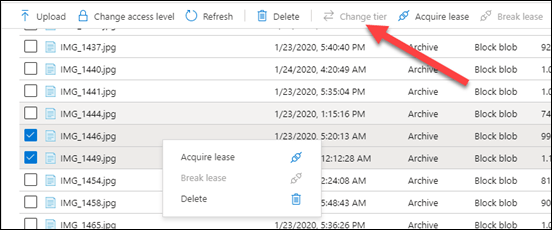
The challenge becomes when you want to do more than a single file at a time.
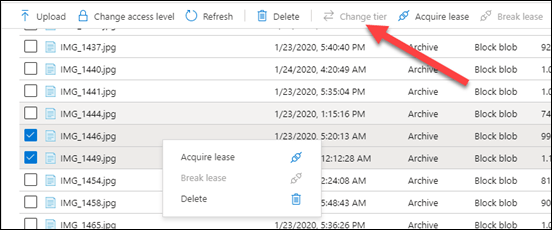
You’ll see that you now don’t get the option to set a tier any more once you have two items or more selected. The same happens with Azure Storage Explorer as well.
Thanks to Marc Kean who pointed me in the right direction, the solution lies in changing this programmatically. Marc has a script on his site and I found another on GitHub as well but decided to write my own anyway which you’ll find here:
https://github.com/directorcia/Azure/blob/master/az-blob-tierset.ps1
with mine you’ll need to set the following variable first at the top of the script:
$storageaccountname = “<your storage account name here>”
$storageresourcegroup = “<your storage account resource group name here>”
$storagetier = “<your desired storage tier level here>” # Hot, Cool or Archive
You’ll also need to connect to you Azure account beforehand which you can do with script of mine:
https://github.com/directorcia/Azure/blob/master/az-connect.ps1
My script will, get the storage account via:
$storageaccount = Get-AzStorageAccount -name $storageaccountname -ResourceGroupName $storageresourcegroup
Get the access for that account via
$key = (get-azstorageaccountkey -ResourceGroupName $storageaccount.ResourceGroupName -Name $storageaccount.StorageAccountName).value[0]
Get the context via:
$context = New-AzstorageContext -StorageAccountName $storageaccount.StorageAccountName -StorageAccountKey $key
get the actual container via:
$storagecontainers = get-azstoragecontainer -Context $context
It will then build an array of all the objects in that container. It will then cycle through all these items changing their tier level via:
$blob.icloudblob.SetStandardBlobTier($StorageTier)
This therefore effectively changes all the items in the container to the tier level you select. This is why I like to set up containers for specific tiers rather than intermingling.
Just remember to run this script AFTER you upload your files to swap them to the cheaper Archive tier. You could also use this script to swap them back at a later stage if you need.