Microsoft Purview Message Encryption is a cloud-based email encryption and rights management solution that helps protect sensitive emails in Microsoft 365. This report explains what Purview Message Encryption is, how it works, and provides step-by-step guidance to set it up and use it effectively in a small or medium-sized business (SMB) with Microsoft 365 Business Premium. We also cover policy configuration (mail flow rules and sensitivity labels), licensing considerations (assuming the organisation already has Business Premium), and best practices. All pricing is provided in Australian dollars (AUD) for clarity.

What is Microsoft Purview Message Encryption?
Microsoft Purview Message Encryption (formerly known as Office 365 Message Encryption, OME) is an online email protection service built on Azure Rights Management (Azure RMS)[1]. It combines strong encryption with fine-grained access controls (rights management) to secure email communication. With Purview Message Encryption enabled, users can send encrypted emails to recipients inside and outside the organisation. The encryption is enforced such that only recipients who authenticate with the allowed credentials (e.g. their Microsoft 365 or Gmail account, as specified by the policy) can decrypt and read the message; anyone else who intercepts it sees indecipherable content[2].
Purview Message Encryption enhances the default security of email in Microsoft 365. By default, Microsoft 365 already encrypts data in transit between its data centers and uses TLS encryption for emails in transport. However, Purview Message Encryption goes further by encrypting the message content itself and applying persistent protection. This means the protection stays with the email even after it leaves Microsoft’s servers, and it can enforce restrictions like “Do Not Forward”. For example, you can send an email that cannot be forwarded or printed by the recipient, or an email that only specific people (inside or outside your company) are permitted to open[3]. The encryption persists regardless of where the email goes – it remains encrypted at rest in mailboxes and in transit over the internet[3].
How it works: Purview Message Encryption uses Azure RMS (part of Microsoft Purview Information Protection) to encrypt the email and any attachments, and to apply rights policies. When an authorised recipient attempts to open an encrypted email, Outlook (or the viewer portal) checks their identity against the email’s permissions. If permitted, the service silently decrypts the content for viewing; if not, access is denied[3]. Internally, Office apps like Outlook, Outlook on the web, or mobile Outlook provide a seamless reading experience – users see the content normally if they have access rights. External recipients (for example, a client using Gmail) receive an email notification (often branded with your company’s details) stating that they’ve received an encrypted message. They are prompted to authenticate (using a one-time passcode or by signing in with a Google/Microsoft account) on the encrypted message portal, after which they can read and respond securely through that portal[1]. This approach means you can safely send confidential data to any email address.
Comparison to traditional encryption: Unlike S/MIME encryption (which requires exchanging certificates) or manual password-protected attachments, Purview Message Encryption is centrally managed and user-friendly. The sender doesn’t need the recipient’s public key or a shared secret; instead, the encryption and key management are handled by Azure RMS. The recipient just needs to verify their identity. Purview Message Encryption was introduced as an evolution of the legacy OME and Information Rights Management (IRM) features in Exchange. In fact, Office 365 Message Encryption (OME) was retired in July 2023 and automatically replaced by Purview Message Encryption, which provides a more streamlined experience[4]. Key improvements in the new Purview solution include an “Encrypt-Only” option (allowing encryption without restricting recipient actions, for easier collaboration), the ability for users to manually encrypt emails directly in Outlook (not only via admin rules)[4], and a unified experience for both internal and external recipients (no more downloading of HTML attachments; external users use a web portal)[4].
Example use cases: An SMB might use Purview Message Encryption to protect emails that include personally identifiable information (PII) like customer contact details or tax file numbers, financial data like bank account or credit card numbers, or any confidential business information. For instance: an accounting firm can ensure that all emails containing tax file numbers or financial statements are encrypted; a healthcare clinic can automatically encrypt emails with patient data to comply with privacy laws; or staff could manually choose a “Confidential – Recipients Only” label when sending internal strategy documents to prevent those emails from being forwarded outside the company.
Licensing and Requirements
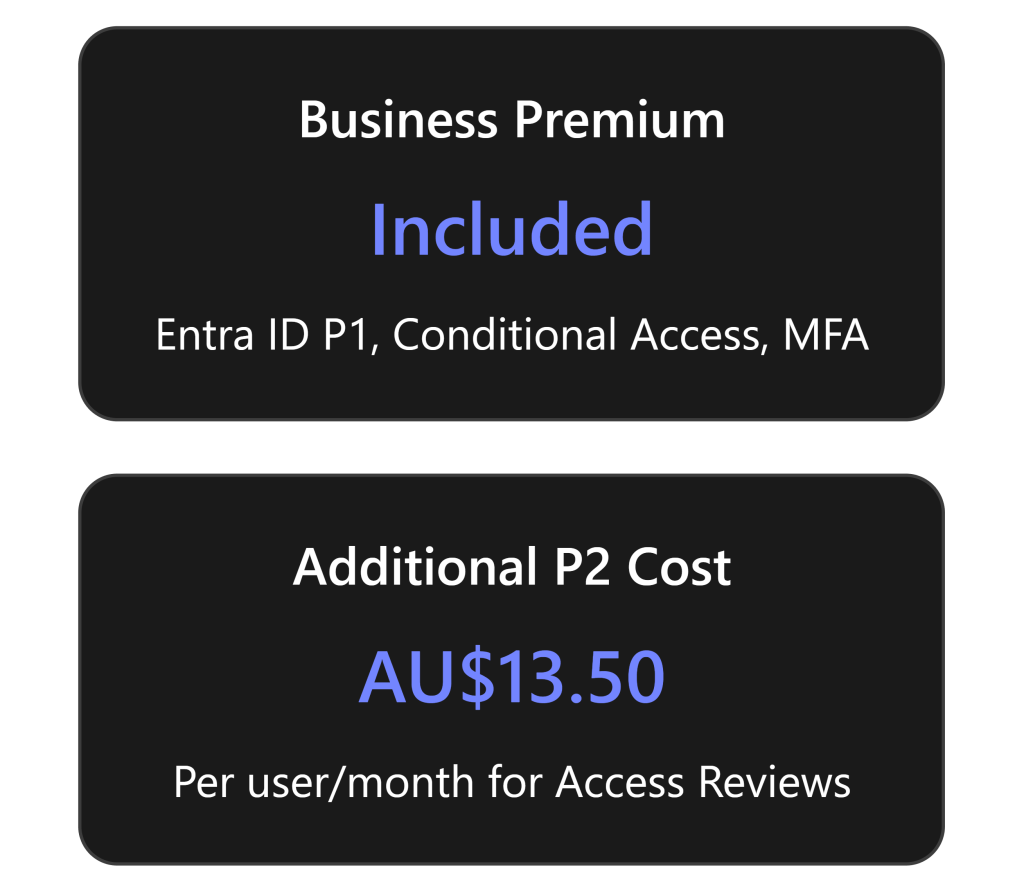
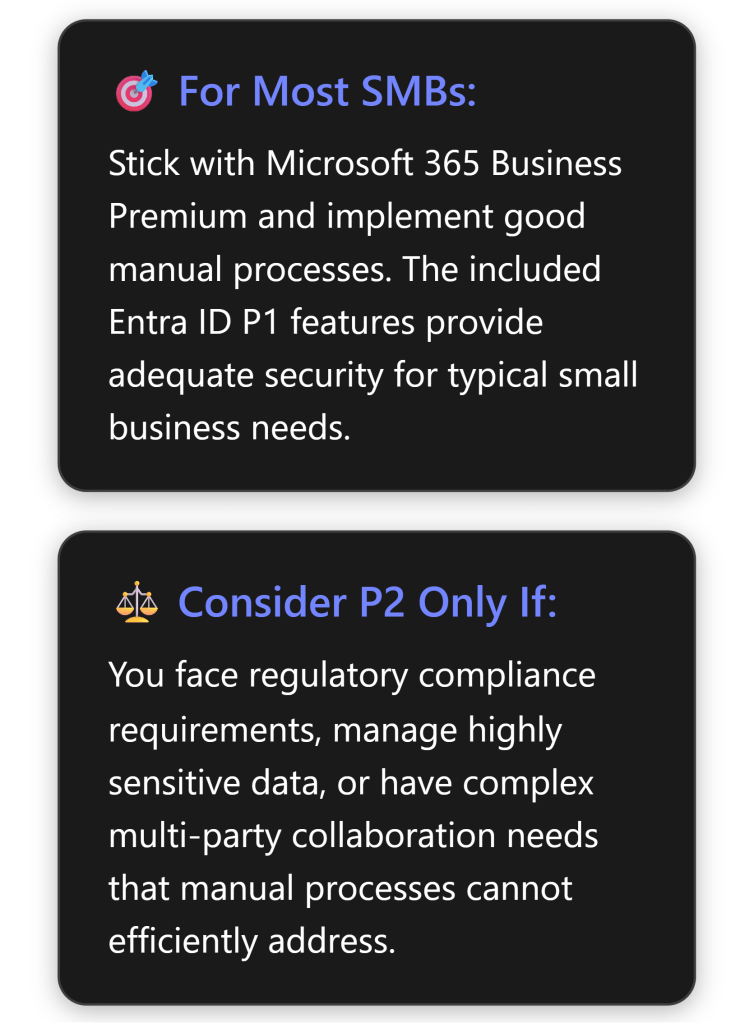
One of the advantages for SMBs with Microsoft 365 Business Premium is that Purview Message Encryption is already included in your subscription[4]. Business Premium includes Azure Information Protection (AIP) Plan 1[5][5], which provides the rights management and labeling capabilities underpinning Purview Message Encryption. This means you do not need to purchase any additional licenses to use the standard email encryption features.
To clarify how Purview Message Encryption is licensed, the table below compares Business Premium with other Microsoft 365 plans in context:
| Plan or License | Email Encryption Availability | Additional Requirements? | Price (AUD)* |
|---|---|---|---|
| Microsoft 365 Business Premium | Included – Purview Message Encryption via AIP Plan 1[4] | No extra license needed. Azure RMS is automatically available. | $32.90 user/month (ex. GST)[5] |
| Microsoft 365 Business Standard / Basic | Not included by default in these plans. | Requires add-on: Purchase Azure Information Protection Plan 1 for each user to enable Purview Message Encryption[4]. | $18.70 / $9.00 user/month (ex. GST) + AIP P1 add-on (~$2.80 ex. GST per user/month)[5][6] |
| Office 365 E3 / Microsoft 365 E3 | Included – Rights Management (AIP P1) is part of E3[1]. | No extra license needed for standard encryption features. | ~$32.80 user/month (ex. GST) for Office 365 E3[7]. |
| Office 365 E5 / Microsoft 365 E5 | Included – AIP Plan 2 is included, which adds Advanced Message Encryption. | No extra license needed; advanced features available (e.g. decrypting/revoking email). | ~$56.40 user/month (ex. GST) for Office 365 E5[7]. |
*Prices are per-user, per-month in Australian dollars. Business plans are listed at annual commitment rates excluding GST[5]; enterprise plan prices are approximate. GST in Australia is 10%, so e.g. Business Premium is about $36.19 including GST.
As shown above, Microsoft 365 Business Premium already covers the necessary licensing. If an organisation had Business Standard or Business Basic, they would need to add Azure Information Protection Plan 1 licenses (approximately A$3 per user per month) to get the encryption capability[4][6]. Enterprise E3 plans include it by default, and E5 plans include even more capabilities (more on Advanced Message Encryption below). Each user who sends or reads encrypted emails should be licensed appropriately[4].
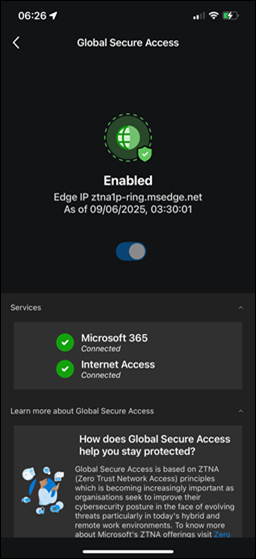
Technical requirements: The core requirement to use Purview Message Encryption is that the Azure Rights Management service is activated for your tenant[8]. In most cases, for eligible plans like Business Premium, this service is activated automatically by Microsoft, so no manual step is needed[8]. It’s essentially “on” if you have the right license. However, if your organisation previously used on-premises Active Directory Rights Management Services (AD RMS) or had deliberately turned off Azure RMS, you may need to activate it or migrate to Azure RMS first[4][8]. (This is uncommon for SMBs; it typically applies to larger organisations that had older on-prem infrastructure. In an SMB cloud-only environment, you can assume Azure RMS is enabled by default.)
To double-check, an admin can run a simple PowerShell command in Exchange Online:
Get-IRMConfiguration– this should showAzureRMSLicensingEnabled : Trueif Azure RMS (and thus Purview encryption) is enabled for your tenant[8].
If it’s False, you can enable it by running Set-IRMConfiguration -AzureRMSLicensingEnabled $True[8]. You might also run Test-IRMConfiguration -Sender <user> -Recipient <user> (using any two user emails in your org) to verify that encryption and decryption tests pass and that it finds the default RMS templates (like “Contoso – Confidential” or “Do Not Forward”)[8]. A successful test confirms that your tenant is correctly configured for Purview Message Encryption.
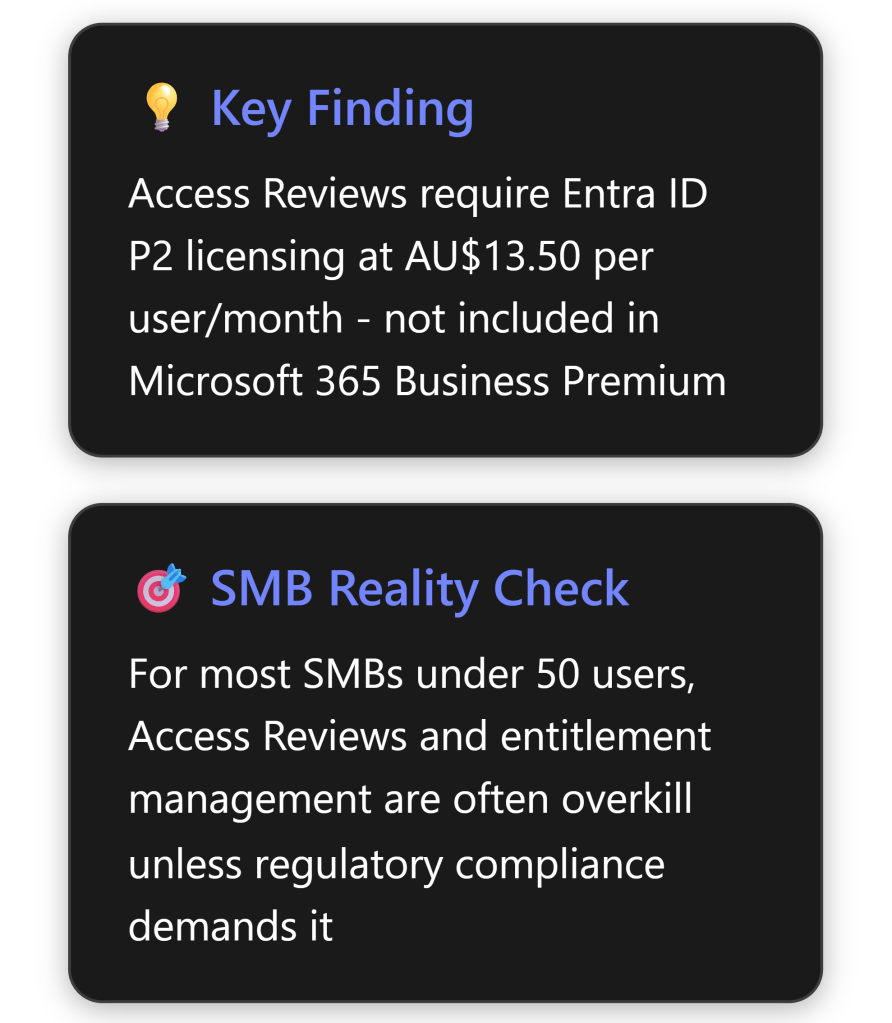
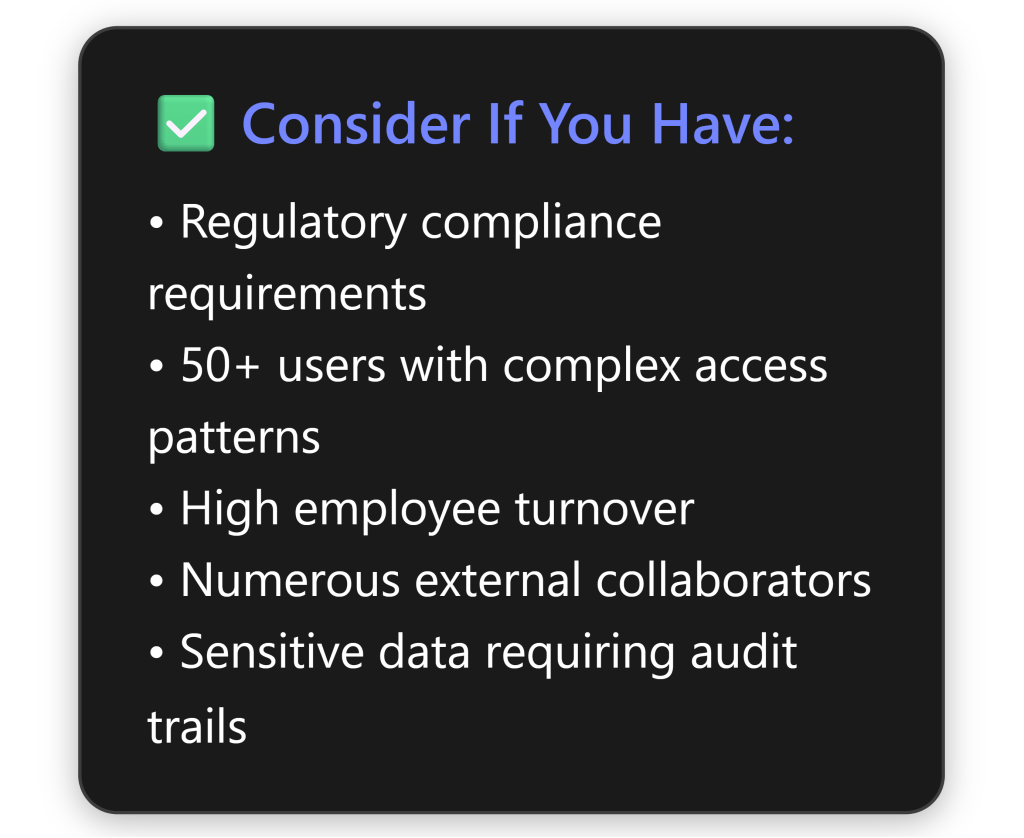
Advanced Message Encryption (AME): It’s worth noting that Microsoft offers an Advanced Message Encryption feature set for organisations with higher compliance needs. AME is included with the top-tier E5 licenses (or as an add-on via the Microsoft 365 E5 Compliance suite for others)[9]. It builds upon the standard encryption features by allowing more control over encrypted emails. For example, admins can define multiple custom branding templates for different purposes, set expiration dates on encrypted emails, or revoke access to an already-sent encrypted email via the admin portal[9][9]. These advanced controls are particularly useful if you need to automatically expire sensitive emails after a period or track and revoke messages for compliance. However, Advanced Message Encryption is not included in Business Premium, and for most SMB scenarios, the standard encryption (already provided) is sufficient. We will focus on the out-of-the-box capabilities available with Business Premium.
Step-by-Step Setup Guide for Purview Message Encryption
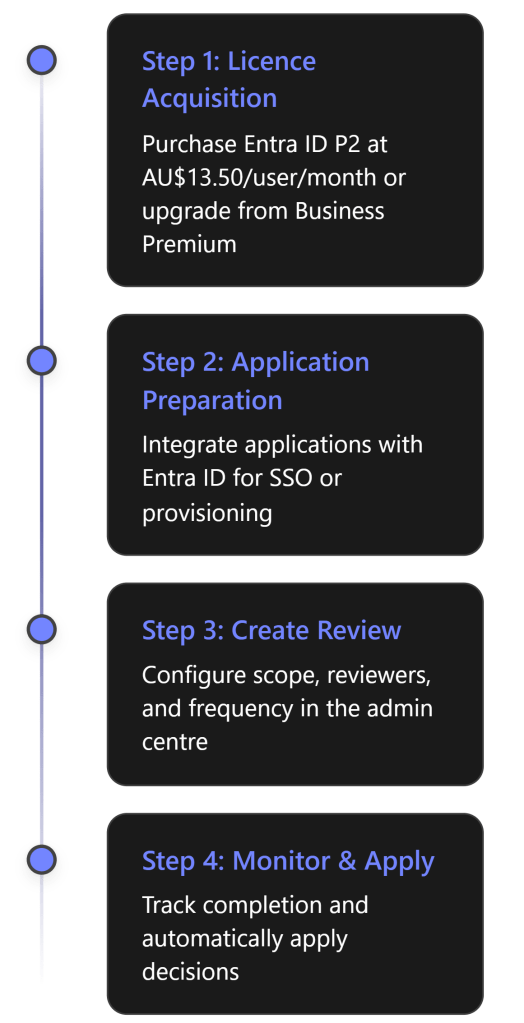
Setting up Purview Message Encryption in a Business Premium tenant involves a few one-time configuration steps by an administrator. Below is an overview timeline of the key steps, followed by detailed guidance:

Let’s dive into each of these steps in detail:
Step 1: Activate (or Verify) Azure Rights Management Service
Why: Purview Message Encryption relies on Azure Rights Management (the encryption engine of Azure Information Protection) to do the encryption and decryption. If Azure RMS isn’t active, encryption will not work.
What to do: In a Business Premium tenant, Azure RMS is typically already activated[8]. To double-check, you can go to the Microsoft Purview compliance portal, navigate to Information Protection > Overview. If you see a banner or option to “Activate” Azure Information Protection, go ahead and activate it. (If everything is already active, there may be no such prompt.)
For a programmatic verification, use PowerShell: Connect to Exchange Online (with an admin account) and run:
Get-IRMConfiguration | fl AzureRMSLicensingEnabled
If it returns True, then RMS is enabled[8]. If False, enable it by running:
Set-IRMConfiguration -AzureRMSLicensingEnabled $true
Additionally, if your organisation had been using an on-premises AD RMS server in the past and you haven’t yet switched, you must migrate to Azure RMS first[4]. (This likely doesn’t apply to a cloud-based SMB setup.)
Optional – Bring Your Own Key: By default, Microsoft manages the cryptographic keys used for encryption. Some organisations (usually larger or highly regulated ones) prefer to manage their own root key for encryption (a process called BYOK – Bring Your Own Key). This is complex and typically not necessary for an SMB. Microsoft recommends most customers let the service manage keys[8]. If BYOK is desired for compliance reasons, it should be done before broad deployment of encryption. (BYOK setup involves Azure Key Vault and is beyond the scope of this guide, but it’s supported[8].)
Step 2: Verify Configuration with Test Commands
After activation, it’s good practice to verify that encryption is fully functional in your tenant:
- Run
Test-IRMConfiguration -Sender <user@yourorg.com> -Recipient <user@yourorg.com>in Exchange Online PowerShell (substitute any valid sender and recipient in your organisation)[8]. This test attempts to acquire RMS templates, then encrypt and decrypt a sample message internally. You should see output with PASS results for acquiring templates, encryption, decryption, and IRM being enabled[8]. Typically, it will list available templates such as “ – Confidential”, “Do Not Forward”, etc., and conclude with “Overall Result: PASS”. - If the test fails with an error like “Failed to acquire RMS templates”, it may indicate Azure RMS wasn’t enabled or there’s a configuration issue. The Microsoft documentation provides additional PowerShell steps to troubleshoot this (for example, connecting to the AIPService module to set the licensing location)[8]. In most cases, with Business Premium, this step will pass on the first try if your licenses are assigned properly.
This verification ensures that your tenant is ready to start encrypting emails.
Step 3: Create Mail Flow Rules to Encrypt Emails (Automatic Encryption)
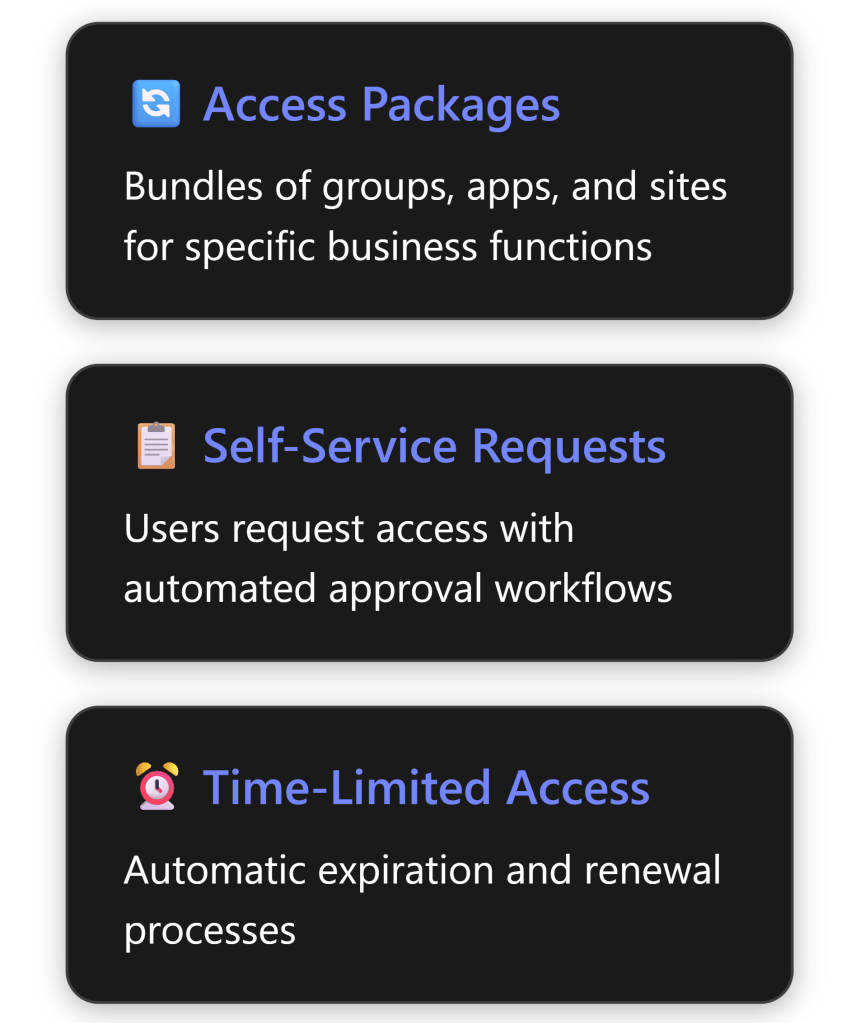
Mail flow rules (also known as transport rules) allow administrators to automatically apply encryption to emails that meet certain conditions. This is the primary way to enforce encryption consistently without relying solely on users. You can create rules, for example, to:
- Encrypt all outbound emails sent to recipients outside your organisation (external email).
- Encrypt messages that contain certain sensitive keywords or data (like “Confidential”, or credit card numbers, etc.).
- Encrypt emails sent to specific recipients or domains (for instance, always encrypt emails sent to a particular partner organisation or a specific client’s email address).
- Prevent recipients from forwarding certain emails by using a “Do Not Forward” template.
How to set up a new rule: Use the Exchange Admin Center (EAC) for a GUI approach or PowerShell for scripting. In the new EAC (https://admin.exchange.microsoft.com) go to Mail flow > Rules and click + Add a rule. Give the rule a name (e.g. “Encrypt outgoing financial data”). Then:
- Conditions: Under “Apply this rule if…”, choose the condition that triggers encryption. Common conditions are:
- “The recipient is located – Outside the organization” (to target external emails)[10].
- “The subject or body includes – ” or “The message contains sensitive information – ” (to target specific content).
- “The recipient domain is – \” (to target specific partner domains).
- You can combine multiple conditions with Add condition for specificity (e.g. external + contains “Project X”)[10][1].
- Actions: Under “Do the following…”, select Modify the message security > Apply Office 365 Message Encryption and rights protection[10]. Once you select this, another drop-down appears to choose an RMS template. Here you will see options like Encrypt, Do Not Forward, and any custom templates/labels you have.
- Choose Encrypt if you just want to encrypt (allowing recipients to forward or reply normally, but the message stays encrypted).
- Choose Do Not Forward if you want to encrypt and restrict recipients from forwarding or copying the content.
- (If you had published sensitivity labels that include encryption, their names might also appear here as available templates.)
- After selecting the template, click Save.
- You can add additional actions if needed (for example, adding a footer to notify the recipient that the message was encrypted). But typically just applying encryption is enough.
- Exceptions (optional): You may add exceptions if there are cases you don’t want to encrypt even if conditions match. For example, you might exclude a specific internal sender or a trusted external domain from the rule.
- Mode: Set the rule to Active (or test in audit mode first if you prefer). Save the rule.
Once enabled, any new email that meets the conditions will be automatically encrypted as it’s sent out. For instance, if you created a rule to encrypt all external mail, whenever a user sends an email to an @gmail.com or any non-company address, Exchange will apply encryption before delivering the message. These rules are enforced on the server side, so they work regardless of whether the user is on Outlook desktop, mobile, or another client.
Important: Mail flow rules cannot encrypt messages incoming from outside senders to you – they only act on messages your users send. If, for example, an external partner sends you an unencrypted email with sensitive info, the Exchange Online transport rule can’t retroactively encrypt that inbound message[10]. It will be delivered as is. (Transport rules in Exchange Online don’t support encryption as an action on incoming mail from outside, by design.) To protect inbound communications, you’d have to rely on the sender encrypting it on their side or use other methods (like asking them to use a secure portal).
You can create multiple mail flow rules for different scenarios as needed. Microsoft’s rules are quite flexible – you can combine conditions (AND/OR logic) and have multiple separate rules to handle various needs[1]. When you have more than one encryption rule, be mindful of their order and if any might overlap; rules can be ordered and if two rules apply encryption, the result is the same (the email is encrypted once). Also, consider adding a rule to strip encryption in certain cases if needed (for example, some organisations add a rule to decrypt emails sent to an internal archiving mailbox or certain internal tools, so that those systems can index or scan the content). Microsoft provides guidance on creating a rule to remove encryption as well[10], but for most SMB scenarios this may not be necessary.
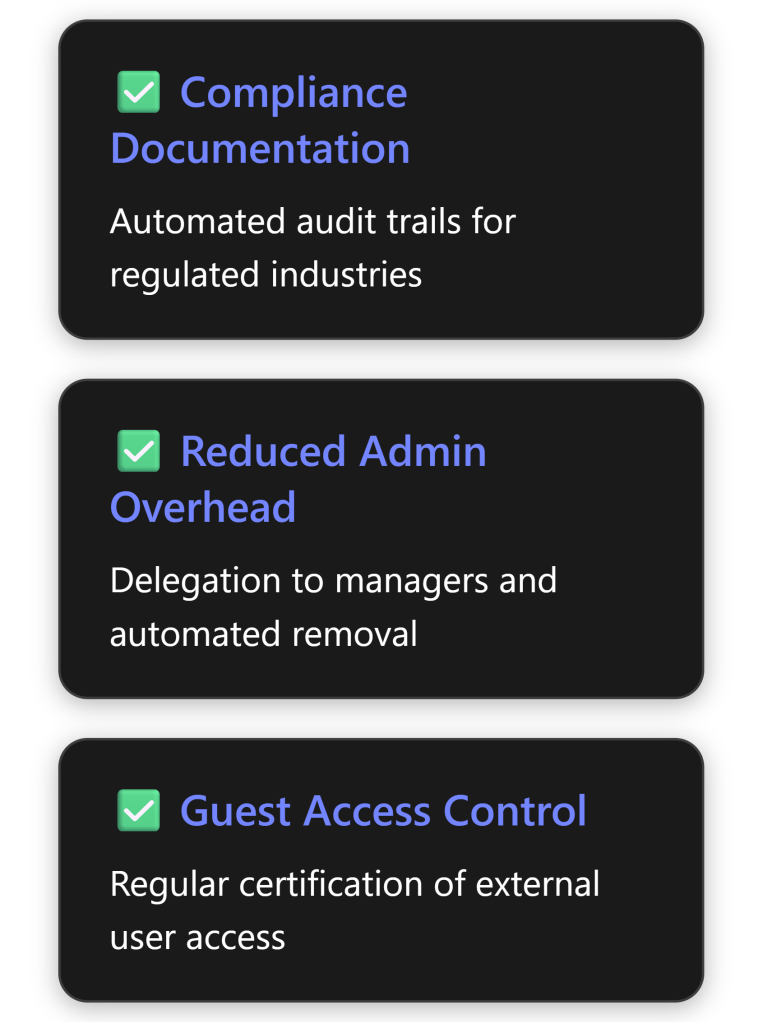
After setting up your encryption mail flow rules, you effectively have automatic encryption policies in place. This is great for compliance: it doesn’t rely on employees remembering to do anything. For example, you could enforce that all emails leaving your company with an attachment get encrypted, or any email mentioning “Payroll” that goes externally is encrypted.
Tip – using Data Loss Prevention (DLP): In Business Premium, you also have Microsoft Purview Data Loss Prevention available. A DLP policy can detect sensitive info (like credit card or TFN numbers) and one of the possible actions is to encrypt the message. This is essentially another way to create content-based encryption rules, with a richer interface for detecting sensitive info types. For instance, a DLP policy could automatically encrypt any email that contains a tax file number or health record. This achieves a similar outcome as mail flow rules. In fact, one recommended approach (for scenarios like HIPAA in healthcare) is to use DLP as a “smart filter” that scans emails and then triggers encryption when a sensitive data pattern is found[11]. The advantage of using Purview DLP policies for this is that you get benefits like detailed incident logging and user notifications. According to a case study, this delivers “zero user effort” (encryption happens even if staff forget), central control (one admin policy covers all mailboxes), and audit-ready logs of every encryption action[11]. In summary, DLP and mail flow rules both can automatically apply encryption – you can choose whichever method fits your admin comfort. (Mail flow rules are simpler to set up for straightforward conditions; DLP is powerful for detecting specific data types.)
Step 4: Set Up Sensitivity Labels for Encryption (Manual User-Driven Encryption)
While mail flow rules handle automatic encryption, you also likely want to empower users to manually encrypt emails when they choose. Business Premium allows you to create sensitivity labels in the Purview Compliance portal, which users can apply to emails or documents. These labels can be configured to include encryption.
For example, you might create a label called “Confidential – All Employees” that, when applied to an email, automatically encrypts it and only allows people within your organisation to open or read it. Or a label “Highly Confidential – No external sharing” that not only encrypts the email but also uses the “Do Not Forward” policy so recipients (even internal ones) cannot forward or copy the content.
How to create a sensitivity label with encryption:
- In the Microsoft Purview compliance portal (https://compliance.microsoft.com), go to Information Protection > Labels and click + Create a label.
- Give the label a name (e.g. “Confidential – Company Only”) and description for users.
- For the label scope, make sure Emails (and files, if desired) is selected, so that this label can apply to email content[3].
- In the configuration, you’ll have options for adding encryption. Enable the setting to “Encrypt content” (in older interface this might be a checkbox like “Protect content” or “Control access to content”[3]).
- You will be asked to choose how to assign permissions:
- Assign permissions now: You as the admin specify exactly who can do what with content under this label. For instance, you can state “Only users inside my organisation can view this email; they cannot forward or print it” (which is effectively an internal-only, do-not-forward policy). You could also allow some group full rights and others read-only. This is static; end users applying the label don’t get to change the permissions.
- Let users assign permissions when they apply the label: This option is useful if you want to give users some flexibility. With this, when a user applies the label in Outlook, they will be prompted to enter who should be able to access the content (they could type in specific email addresses or choose from a directory) and what permissions to give. This is akin to users creating an ad-hoc encryption rule on the fly, within the bounds you allow[3].
- If assigning permissions now, configure the specifics:
- Choose the users or groups who will be granted access when this label is applied (e.g. All members of for all internal).
- Choose their permissions: e.g. Viewer (read-only), or Editor (read and modify), etc. For email scenarios, typically read-only is used if you want to prevent forwarding, whereas if you just want to allow normal usage, giving view + edit might be fine (edit in context of email means ability to reply/forward I believe).
- If relevant, you can tick an option “Do not allow forwarding” which automatically restricts forwarding and copying from the email (this is essentially the Do Not Forward template enforced via the label).
- You can also set content expiration here (e.g., email content expires after 30 days) if using Azure Information Protection P2, but with P1 (Business Premium) this might not be available in sensitivity labels interface. Typically expiration is an advanced feature.
- You might see an option for offline access or the number of days a user can access the content without re-authenticating – these are fine-tuning options.
- Finish the label creation. Then, publish the label by creating a Label Policy (in Information Protection > Label Policies, include the new label and target it to the desired users or whole organisation). This causes the label to appear in end-user apps.
Once published (it may take a little time or a restart of Office apps to show up), users will see the sensitivity label in their Outlook (on the ribbon or under the Sensitivity button). They can apply it to an email just like they would mark it Confidential. Behind the scenes, as soon as they send an email with that label, the Exchange service will encrypt the message according to the rules you configured.
End-user experience (manual): If no sensitivity labels are defined, users in Business Premium will still typically have an “Encrypt” button in Outlook on the web or under Outlook’s Options > Permissions menu, giving them at least the default Encrypt-Only and Do Not Forward choices[1]. However, using custom labels allows you to present more user-friendly or scenario-specific options (with your own descriptions) and to integrate encryption with your classification scheme (e.g. a single label might also add a footer/tag like “Confidential” in addition to encryption).
For example, after the above setup, a user writing an email in Outlook can click the Sensitivity drop-down and choose “Confidential – Company Only”. Immediately, Outlook will show a small lock icon or a note indicating that encryption and forwarding restrictions are applied. When that user sends the email, it will be encrypted and only other people within the company tenant will be able to open it. If they accidentally sent it to an external address, that external recipient would get a message stating the email is protected and they are not authorised to view it (since our hypothetical label didn’t grant external access).
Important considerations with labels:
- Exchange IRM Configuration: To get the full benefits of using sensitivity labels to encrypt emails, you should ensure IRM is enabled in Exchange (which we did in Step 1)[3]. Otherwise, certain clients might not be able to open encrypted mails and search indexing might not work. We covered this, but it’s worth noting that enabling IRM (AzureRMS in Exchange Online) is what allows even mobile Outlook and web to open these labeled emails seamlessly.
- Multiple encryption methods: If a user applies a sensitivity label that encrypts an email, you do not need a mail flow rule to also encrypt it (and vice versa). They won’t conflict – the mail flow rule will typically detect the mail is already encrypted and skip, or it will apply encryption to an already encrypted mail which is fine (it remains encrypted). However, generally design your strategy to use either automatic rules for certain scenarios and labels for user-driven ones. They solve different problems (one doesn’t rely on the user at all, the other gives user flexibility).
- User training: It’s a good idea to show your staff how to use the new sensitivity labels in Outlook. For instance, explain that when they have a particularly sensitive email to send, they should apply the Confidential label before sending. The first time, some may be confused by the experience for external recipients (e.g. “The client said they had to click a link to view my email”). Include that in training so they and the recipient know it’s normal due to encryption.
Step 5: Test the Encryption Setup
Before rolling out broadly, test the configuration:
- Internal test: Have two users (or use your test account) within the company send encrypted emails to each other. They should be able to open them normally in Outlook (perhaps a small banner might indicate the message is encrypted). This ensures internal access isn’t inadvertently blocked by a policy.
- External test: Send an email from inside to an outside email (e.g., a personal Gmail or Outlook.com account) that should trigger encryption – for example, an email containing a sensitive keyword if you made that rule, or just any email if you encrypted all external mail. Confirm that:
- The external recipient gets a mail notification that’s branded (by default it will show your organisation name) saying “You’ve received an encrypted message”[11].
- The external recipient can follow the link or the instructions to authenticate and read the message in the browser. They might use a one-time passcode or sign in with a Google/Microsoft account. Test both if possible.
- Check that the content of the message is correct when they do see it (formatting, attachments if any).
- Reply as the external user through the portal and ensure the internal user can read the reply (the reply will also be encrypted).
- Policy tuning: If the external email did not arrive encrypted when it should have, double-check the conditions of your mail flow rule or DLP policy (maybe the test didn’t meet the condition exactly)[11]. Also verify the sender has the appropriate license (Business Premium assigned, etc.), since each sender needs a license for encryption to apply[11].
Everything working? Great. Now you can confidently roll this out knowing that protected emails actually reach their destination securely.
Step 6: User Awareness and Best Practices for Effective Use
Finally, effective use of Purview Message Encryption in an SMB isn’t just about configuration – it’s about incorporating it into your organisation’s workflows and culture. Here are some best practices and tips to get the most value:
- Educate your team: Introduce the feature to your users. Let them know that some emails will now be encrypted and what that means. For example, explain that if they see a lock icon or a banner that says “This message is encrypted” in an email, it’s expected. Likewise, if they send an encrypted email to a client, that client may contact them about the extra step to open it – your user should be able to reassure them it’s for security. Microsoft provides user-friendly guides on how to https://support.microsoft.com/office/cb882d70-47c1-4da6-b7da-4bb6ee4893b4 and how to open one, which you can circulate. In Outlook on the web, the user just clicks Encrypt under the compose options; in desktop Outlook, they can select an Options > Permissions setting or use the Sensitivity button if labels are deployed.
- Start with clear policies: When deciding what to encrypt, start with the most sensitive or regulated information. Don’t over-encrypt everything, or users might get frustrated with extra steps for trivial email. Common starting points are: encrypt all external emails (if your business frequently sends confidential data externally), or encrypt based on keywords (like “Confidential”, project names) or sensitivity types (like any email with a 9-digit number might be a TFN – treat accordingly). Make sure these rules are well-communicated. For instance, if you choose to automatically encrypt all external mail, users should know every email to a customer will have that behaviour (so they’re not caught off guard by a client’s questions).
- Use branding for familiarity: You have the option to customise the branding of the encrypted message mail and portal – for example, adding your company logo and a friendly message. This is done via the Set-OMEConfiguration cmdlet (for the standard single template) or in the Purview portal for advanced branding. Consider doing this so that when an external recipient gets an encrypted mail, they see your company’s name or logo on the portal. It helps them trust that it’s legitimate and from you. (Branding is an included feature for one template; multiple templates require AME/E5.)
- Integrate with DLP for compliance (if needed): As discussed, if you have compliance requirements (like HIPAA for health info, or need to protect credit card data under PCI DSS), leverage DLP policies. DLP can not only encrypt but also notify the sender (policy tip) that “This email was automatically encrypted because it contains XYZ”. This educates users over time on what triggers protection, and it provides an audit trail. In Business Premium, DLP for email is available[2][2] and can be a powerful ally in preventing data leaks.
- Test periodically: Make encryption testing part of your routine, especially after any Exchange or compliance configuration changes. Ensure new employees have the appropriate license and can use encryption if needed.
- Monitor and adjust: Check the reports in the Purview Compliance portal. There are audit logs and reports that can show label usage and DLP policy matches. For example, you can see how often your encryption rule triggers, or if any emails were blocked or had encryption removed. This can help fine-tune conditions (to reduce false positives, etc.). In an SMB, volume may be low, but it’s good to keep an eye that it’s working as intended.
- Know the limits: Be aware of a few limitations: The maximum message size for an encrypted email (including attachments) is 25 MB[4]. This is lower than the regular Exchange Online limit for non-encrypted mail. Very large files might need to be shared via SharePoint/OneDrive instead of email if they can’t be sent due to this limit. Also, if you send to many recipients via BCC, note that in some cases those BCC addresses might be dropped before encryption (an edge case with certain routing scenarios)[4] – generally not an issue unless you do mass BCC mailings.
- Advanced controls (if ever needed): If one day your SMB grows or has needs to revoke or expire emails, consider advanced message encryption capabilities. For instance, if an employee accidentally sent an encrypted email to the wrong external person, you as an admin could revoke access to that message (if you had Advanced Message Encryption via an E5 Compliance add-on)[9]. This isn’t available in Business Premium by default, but it’s something to be aware of as a potential upgrade if such scenarios are critical.
By following these steps and best practices, even a small organisation can leverage enterprise-grade email encryption with Microsoft 365 Business Premium. You’ll be keeping sensitive communications secure and meeting compliance obligations, all using tools that integrate natively with the email clients your users already use every day.
Conclusion: Microsoft Purview Message Encryption provides SMBs a robust yet user-friendly way to secure email communications. With Business Premium, you have all the needed components (Azure Information Protection P1, Exchange Online, etc.) to deploy it without additional cost. By carefully configuring the service – enabling it, creating sensible mail flow rules, and utilizing sensitivity labels – you can ensure that confidential information in emails is accessible only to authorised recipients, helping protect your business and your customers. Best of all, it achieves this in a manner that is largely seamless to end users and external partners once set up. In summary, Purview Message Encryption, when set up and used effectively, can significantly enhance your organisation’s data protection posture for email with minimal disruption and excellent integration into your existing Microsoft 365 environment.
References
[1] Enabling Microsoft Purview Message Encryption – UC Today
[2] Set up information protection capabilities – Microsoft 365 admin
[3] Apply encryption using sensitivity labels | Microsoft Learn
[4] Message Encryption FAQ | Microsoft Learn
[5] Microsoft 365 Business Plans and Pricing | Microsoft 365
[6] Microsoft Azure Information Protection – Telstra
[7] Office 365 Pricing Australia | Crowd IT
[8] Set up Microsoft Purview Message Encryption | Microsoft Learn
[9] Advanced Message Encryption | Microsoft Learn
[10] Define mail flow rules to encrypt email messages
[11] How to Automatically Encrypt HIPAA‑Sensitive Email with Microsoft …