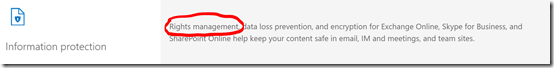
There are many benefits of the more advanced Office 365 plans. One of the benefits you receive with E3 licenses and above is Rights Management:
If you visit the E3 product page at:
https://products.office.com/en-us/business/office-365-enterprise-e3-business-software
You will find the above focus on the included Information Protection features. One of the ways this is provided is via Rights Management.
https://technet.microsoft.com/en-us/network/dn858608.aspx
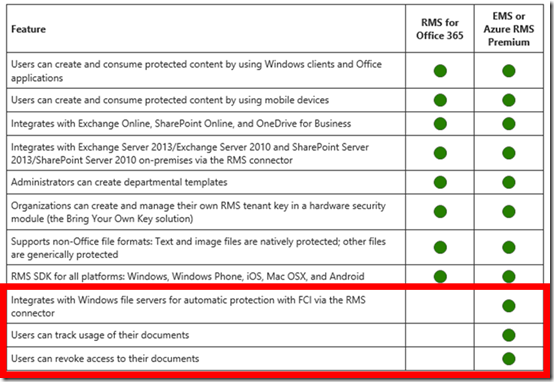
If you visit the above link you’ll find the table that compares the Rights Management features you receive in Office 365 E3 or better and with Azure Rights Management Premium.
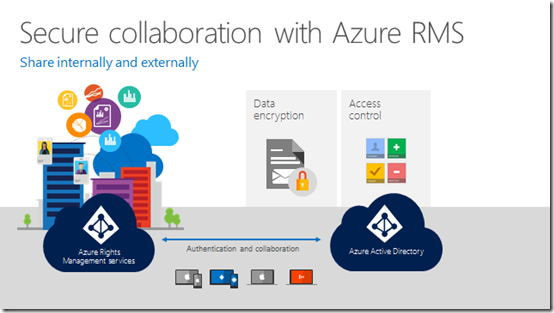
Although Office 365 Rights Management isn’t as full featured as the premium product it does most things a business needs. It will basically protect documents no matter where they are located. Rights Management basically will encrypt documents and embed permissions inside the document. Thus, the permissions go wherever the document goes, inside or outside the business.
This is unlike most documents today that are only protected by the location in which they are stored. If you have a sensitive document on your file server, it is generally locked down via server permissions. However, that doesn’t prevent someone with the appropriate permissions sending that document, as an email attachment say, another person who doesn’t normally have permissions. That is because once the file is removed from its secure container it effectively is no longer protected. That’s because only the container the file lives in has permissions, not the file itself. With Rights Management, the permissions are embedded into the file, ensuring it is protected where ever it goes.
So, if you have Office 365 E3 or better, what’s the easiest way to start using the included Rights Management abilities you get with Office 365?
The easiest way is to configure information to be directly protected from the file system and desktop applications.
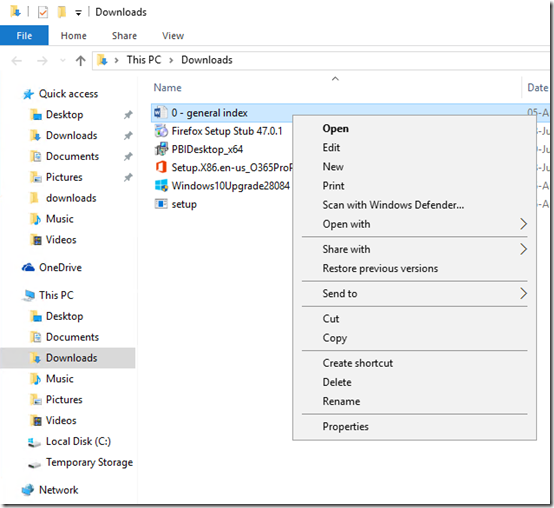
If you look at the above screen shots of PowerPoint and Windows Explorer you see there is no option to apply Rights Management. To provide that we need to firstly install the Rights Management agent software on the desktop.
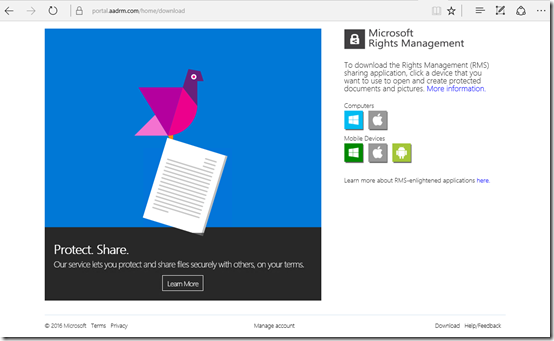
To download the agent software, navigate to the Microsoft Rights Management download portal at:
https://portal.aadrm.com/Home/Download
Simply select the icon that matches your device. In this case we’ll select the Windows computer icon.
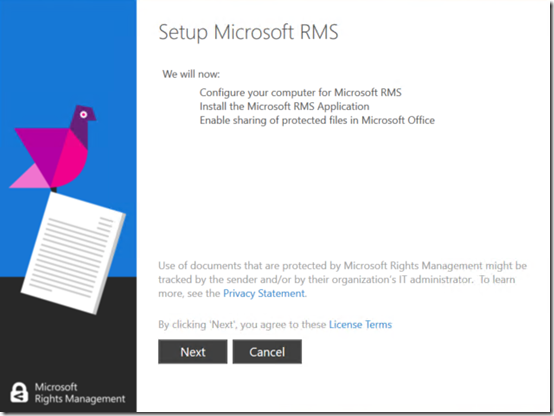
When the software has downloaded, run it.
Select Next to continue.
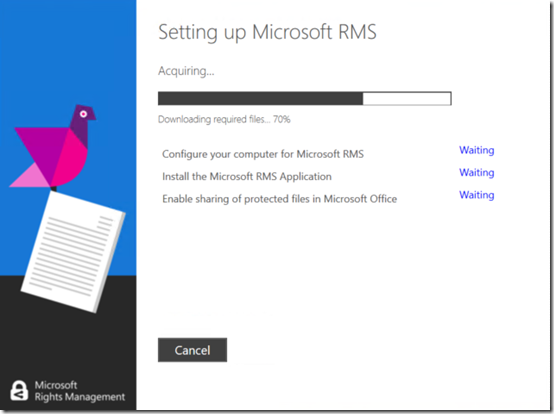
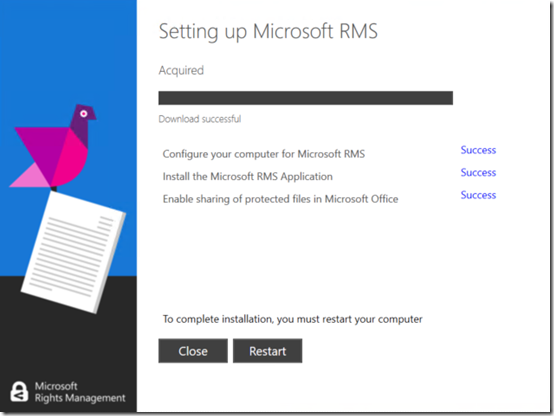
You’ll see the software configure and install Microsoft RMS for you.
After the installation is complete you’ll now need to Restart your system.
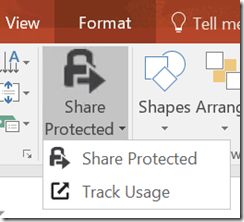
Now when you look at your Office applications you’ll see a new button called Share Protected as shown.
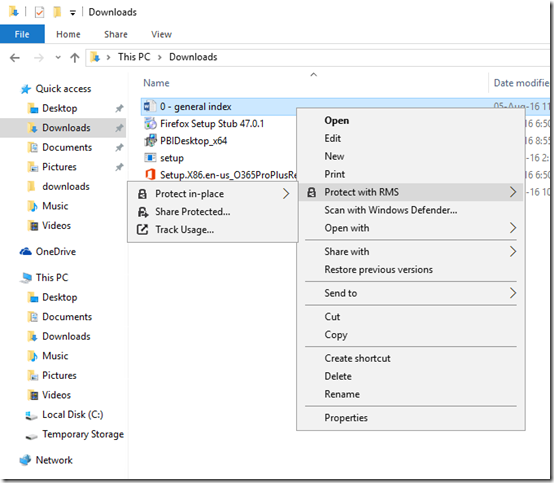
You’ll also find that Rights Management has been embedded into the file manager. Just right mouse click on any file and you’ll see the Protect with RMS option in the menu as shown.
I’ll cover off how you actually use this inbuilt Rights Management functionality to protect your information in an upcoming article, so stay tuned. However, at least now you have the agent installed on your desktop to make protecting your information with Rights Management easy.
Remember, Rights Management with Office 365 is currently only available with E3 or better suites but is also available as a stand alone purchase if you want it.