In a recent article:
Getting Endpoint Privilege Management working
I detailed how to get the basics of Endpoint Privilege Management working using settings policies.
The next step in the process is to get the rules policies working in conjunction with this. The scenario will be that we want to only allow a single application to be run with elevated privileges on a device. Here, that application will be Adobe Acrobat installer.
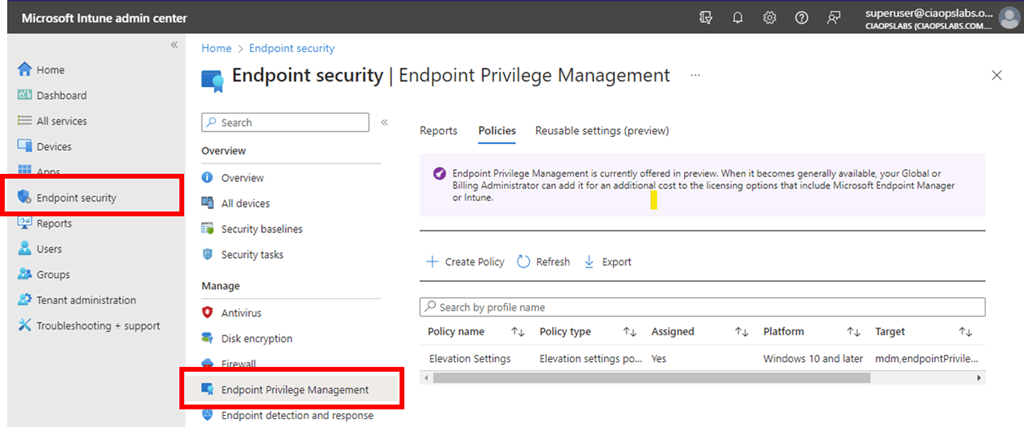
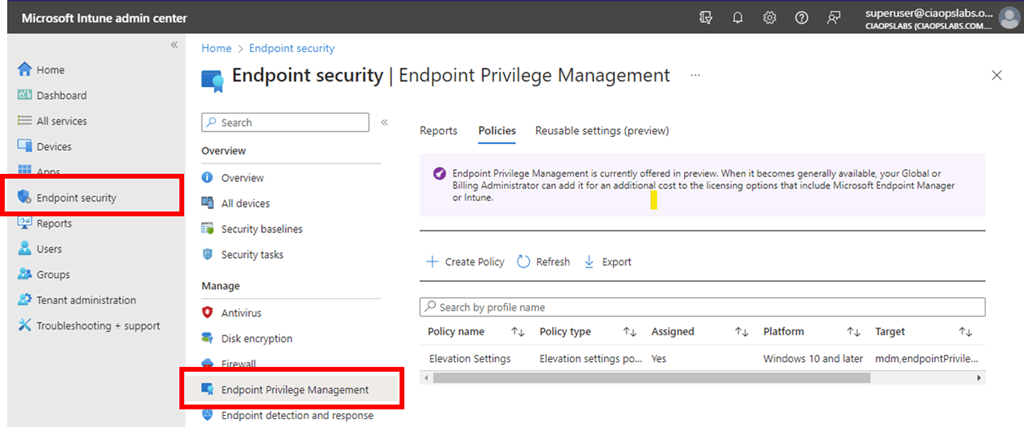
As before, we’ll need to go back into https://intune.microsoft.com under the Endpoint Security menu option as shown above.

We’ll firstly need to edit the original Settings policy from the previous article and change the Default elevation response to Deny all requests as shown above. This will block any request to elevate by default.

Next, we’ll need to create a new policy with the Profile set to Elevation rules policy as shown above.

As always, we need to give this new policy a name.

On the following screen select Edit instance on the right as shown above.

On the blade that appears from the right, you’ll need to give the Rule a name and then a description if you wish.
For the Elevate type I have selected User confirmed rather than automatic as well as requiring Validation to be a Business justification as shown.
Next is the actual file name for the Acrobat Reader installer which is acrordr2300120064_en_US.exe in the File name field.

To get the file hash I used the PowerShell command get-filehash as shown above.

The remaining details were obtained from the properties of the file, as shown above.
I then saved this Rule and completed the creation of the policy using the standard process, ensuring I applied it to teh appropriate group in my environment.
Once again, you need to wait until the policies have been pushed out to all devices.

With the policies deployed, if I now right mouse click on the Acrobat Reader installation file and select Run with elevated privileges I see,

that the configured app is identified in the dialog and I need to provide a business justification for the installation as was configured in the rules policy.


Once that has been completed the application installs as normal.

The Adobe Reader application runs on the device once the installation is completed as shown above.

If I try and install another application by using the run with elevated privileges option (here, on the file officesetup.exe), it is blocked as shown above because the default setting policy is deny all. To allow this, another rule for that specific file would need to be created in the policy.
This means that you can now create a default Privilege Management settings policy to deny all requests to elevate and then have specific rules to only allow pre-defined applications to be run as administrator on the device. Remember, all this can be done without needing to have a local administrator on the device.