You get a phone call from a client one Sunday morning in February. One of their bookkeepers had clicked an invoice link the previous Friday afternoon, signed in like normal, and gone home for the weekend. By Monday, the attacker had set up an inbox rule, watched a fortnight of email traffic, and sent a payment-redirect note to a supplier — from the bookkeeper’s actual mailbox. Eighty thousand dollars walked out the door before anyone noticed the wire details had quietly changed.
The tenant had MFA enforced. It had a Conditional Access policy. It had cyber insurance, renewed in January on the strength of those two things. None of that mattered.
The attack moved. The configuration didn’t.
Adversary-in-the-middle phishing kits don’t try to beat the MFA prompt anymore. They wait for the user to complete it, then steal the session token and replay it from somewhere else. Microsoft’s threat intel team disclosed an April campaign that hit thirty-five thousand users across thirteen thousand organisations in twenty-six countries — a single month, a single operator. Every one of those users had MFA. None of them had session controls tuned to actually defend the session.
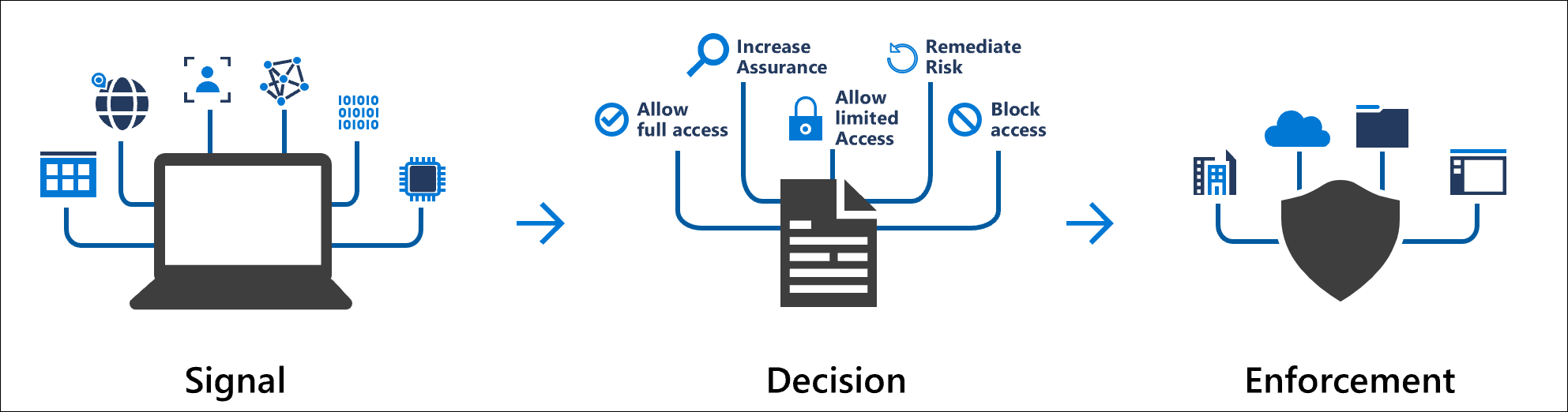
This is the bit MSPs need to sit with. Conditional Access in Entra was never built as an MFA tickbox. It is the session control surface — the place where you decide what a signed-in user can do, from where, on what device, for how long. The grant and session controls in that same blade — the ones most SMB tenants have never opened — are what break this attack. We have spent five years building a defence for 2018 and leaving it deployed in 2026.
Four switches, all in the same blade
There are four controls inside Conditional Access that meaningfully change the outcome of a token theft, and most Business Premium tenants pay for all of them and use none.
- Sign-In Frequency, set deliberately rather than left at its sliding ninety-day default, collapses the lifetime of a stolen token. Most tenants I look at have it set backwards — managed users get prompted constantly while unmanaged sessions ride for weeks.
- Require-compliant-device on Exchange Online forces the attacker’s browser session to fail at the grant, not the prompt.
- Phishing-resistant authentication strength — passkeys, FIDO2, Windows Hello — closes off the credential path to begin with.
- Token Protection, even in report-only on Windows native apps, gives you the telemetry to spot a session being replayed from a country your user has never visited.
None of this is theoretical. Microsoft auto-rolled Conditional Access into more than half a million tenants in late 2023 specifically because tenants were not configuring it themselves. That auto-rollout sets the floor. The four controls above sit above the floor, and they are the ones that change the renewal conversation with your insurer.
The unit economics finally work
The honest reason most MSPs haven’t retuned their CA baseline is that per-tenant identity work used to be uneconomic. That changed. With GDAP and Microsoft Lighthouse, an MSP can review CA policy, push report-only changes, and watch sign-in telemetry across every client tenant from one pane. Pair that with a Loop page or a Teams channel for your security pod and the review cadence stops being a heroics exercise.
The bookkeeper followed her training to the letter. What let her down was a tenant configured for the threat landscape we had four years ago. When the next breach lands in one of your tenants, it will not be the MFA prompt that failed. It will be the session controls nobody touched. That is where the work is now.