Source – Cyber-Safety and IT efficiency fueled by Microsoft Intune Suite – https://secure.microsoft.com/en-US/sessions/b36d5f8d-62f1-440b-9dbe-7b0eea13cdce?source=sessions
Getting Endpoint Privilege Management rule policies working
In a recent article:
Getting Endpoint Privilege Management working
I detailed how to get the basics of Endpoint Privilege Management working using settings policies.
The next step in the process is to get the rules policies working in conjunction with this. The scenario will be that we want to only allow a single application to be run with elevated privileges on a device. Here, that application will be Adobe Acrobat installer.
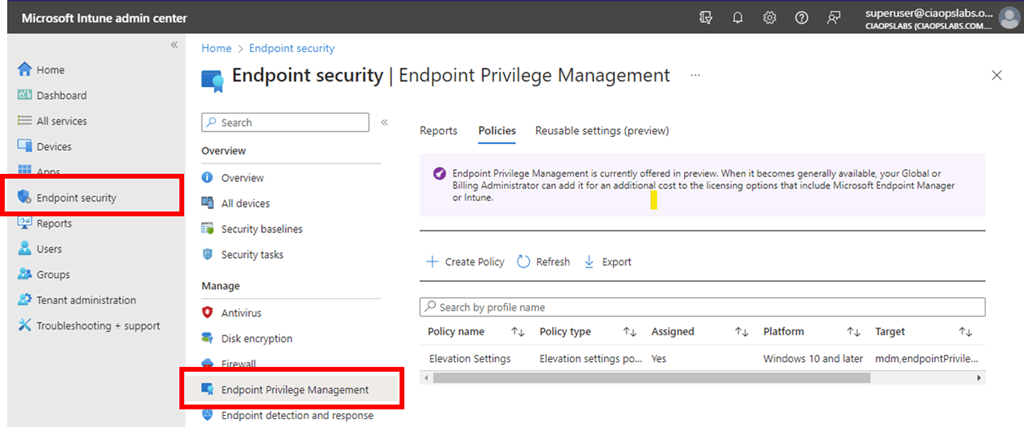
As before, we’ll need to go back into https://intune.microsoft.com under the Endpoint Security menu option as shown above.
We’ll firstly need to edit the original Settings policy from the previous article and change the Default elevation response to Deny all requests as shown above. This will block any request to elevate by default.
Next, we’ll need to create a new policy with the Profile set to Elevation rules policy as shown above.
As always, we need to give this new policy a name.
On the following screen select Edit instance on the right as shown above.
On the blade that appears from the right, you’ll need to give the Rule a name and then a description if you wish.
For the Elevate type I have selected User confirmed rather than automatic as well as requiring Validation to be a Business justification as shown.
Next is the actual file name for the Acrobat Reader installer which is acrordr2300120064_en_US.exe in the File name field.
To get the file hash I used the PowerShell command get-filehash as shown above.
The remaining details were obtained from the properties of the file, as shown above.
I then saved this Rule and completed the creation of the policy using the standard process, ensuring I applied it to teh appropriate group in my environment.
Once again, you need to wait until the policies have been pushed out to all devices.
With the policies deployed, if I now right mouse click on the Acrobat Reader installation file and select Run with elevated privileges I see,
that the configured app is identified in the dialog and I need to provide a business justification for the installation as was configured in the rules policy.
Once that has been completed the application installs as normal.
The Adobe Reader application runs on the device once the installation is completed as shown above.
If I try and install another application by using the run with elevated privileges option (here, on the file officesetup.exe), it is blocked as shown above because the default setting policy is deny all. To allow this, another rule for that specific file would need to be created in the policy.
This means that you can now create a default Privilege Management settings policy to deny all requests to elevate and then have specific rules to only allow pre-defined applications to be run as administrator on the device. Remember, all this can be done without needing to have a local administrator on the device.
Getting Endpoint Privilege Management working
If you are not aware yet, Endpoint Privilege Management is now available in public preview.
You can find it in https://intune.microsoft.com under the Endpoint Security menu option as shown above.
You’ll firstly need to use the Create Policy menu option, as shown to create a policy for your environment.
Select Windows 10 and later for the Platform (only option currently available).
Select Elevation settings policy for the Profile.
Select Create to continue.
As always, give the new policy a name and select Next to continue.
The most important thing here is to ensure that the option Endpoint Privilege Management is set to Enabled as shown above.
In this case, the Default elevation response is set to Require user confirmation.
Select Next to continue.
Continue through the rest of the policy as normal, ensuring you assign this policy to an appropriate group in your organisation.
You can then select on the new policy to view it and then select View report to see the results of how the policy has been applied in your environment.
It is important to ensure your workstations are at the appropriate update level. At the moment that is:
The policy will NOT work until you are at this level.
The above shows the client I used was Win 10 22H2 Build 19045.2788.

When the policy is applied successfully to the device you will find a new directory C:\Programs Files\Microsoft EPM agent is created as shown above.
If you look inside that directory you will see the above structure.
With these files now on the device, you can right mouse click on an executable and you should now see the option Run with elevated access as shown above.
When you select that option you will now be prompted, per the policy options, to enter a confirmation as shown above.
You can find documentation from Microsoft here:
CIAOPS Need to Know Microsoft 365 Webinar – April

Join me for the free monthly CIAOPS Need to Know webinar. Along with all the Microsoft Cloud news we’ll be taking a look at Microsoft Defender for Cloud Apps.
Shortly after registering you should receive an automated email from Microsoft Teams confirming your registration, including all the event details as well as a calendar invite.
You can register for the regular monthly webinar here:
(If you are having issues with the above link copy and paste – https://bit.ly/n2k2304
The details are:
CIAOPS Need to Know Webinar – April 2023
Friday 28th of April 2023
11.00am – 12.00am Sydney Time
All sessions are recorded and posted to the CIAOPS Academy.
The CIAOPS Need to Know Webinars are free to attend but if you want to receive the recording of the session you need to sign up as a CIAOPS patron which you can do here:
or purchase them individually at:
Also feel free at any stage to email me directly via director@ciaops.com with your webinar topic suggestions.
I’d also appreciate you sharing information about this webinar with anyone you feel may benefit from the session and I look forward to seeing you there.
March Microsoft 365 Webinar resources
https://www.slideshare.net/directorcia/march-2023-ciaops-need-to-know-webinar
If you are not a CIAOPS patron you want to view or download a full copy of the video from the session you can do so here:
http://www.ciaopsacademy.com.au/p/need-to-know-webinars
Watch out for next month’s webinar.
Blocking Command Prompt on Windows with an Intune Device Configuration profile
This article shows you how to use Intune to block the Command Prompt on Windows devices using a Configuration profile.

Navigate to https://endpoint.microsoft.com and select Device from the menu on the left as shown above.
Then, select Windows on the right.

Select Configuration profiles from the menu on the left as shown.

Select Create profile.
Then select the Platform as Windows 10 and later.
Select the Profile type as Templates.
From the list of templates select Custom.
Select Create in the bottom right.
Give the policy a name and select Next to continue.

Select Add.
In the OMA-URI settings enter the following as shown above:
Name = Block Command Prompt
Description = Block Command Prompt
OMA-URI = ./user/vendor/MSFT/Policy/Config/ADMX_ShellCommandpromptRegeditTools/DisableCMD
Data type = String
Value =
<enabled/>
<data id=”DisableCMDScripts” value=”1″/>
Ensure you enter these exactly as shown, anything else will prevent the policy working as expected.
Press Save.
You should now see the item you just entered displayed as shown above.
Select Next to continue.

Assign the policy to a group. Here it is being assigned to all Windows devices.
Select Next to continue.
You will now see a summary. Ensure the Configuration settings has the above set before selecting the Create button to complete the policy.
You should now see that the policy has been created and listed with all other Configuration profile policies as shown above.
You can edit this policy at any stage simply by selecting it.

You now need to wait until the policy is deployed successfully to devices. You can check the status of this by viewing the Device status for the policy as shown above.
If you open the Command Prompt on a device where the policy is deployed you will see the above message.
Blocking Registry edits on Windows with an Intune Device Configuration profile
This article shows you how to use Intune to block Registry editing on Windows devices using a Configuration profile.

Navigate to https://endpoint.microsoft.com and select Device from the menu on the left as shown above.
Then, select Windows on the right.

Select Configuration profiles from the menu on the left as shown.
Select Create profile.
Then select the Platform as Windows 10 and later.
Select the Profile type as Templates.
From the list of templates select Custom.
Select Create in the bottom right.
Give the policy a name and select Next to continue.
Select Add.
In the OMA-URI settings enter the following as shown above:
Name = Block Registry
Description = Block Registry
OMA-URI = ./user/vendor/MSFT/Policy/Config/ADMX_ShellCommandpromptRegeditTools/DisableRegedit
Data type = String
Value =
<enabled/>
<data id=”DisableRegeditMode” value=”2″/>
Ensure you enter these exactly as shown, anything else will prevent the policy working as expected.
Press Save.
You should now see the item you just entered displayed as shown above.
Select Next to continue.

Assign the policy to a group. Here it is being assigned to all Windows devices.
Select Next to continue.
You will now see a summary. Ensure the Configuration settings has the above set before selecting the Create button to complete the policy.
You should now see that the policy has been created and listed with all other Configuration profile policies as shown above.
You can edit this policy at any stage simply by selecting it.
You now need to wait until the policy is deployed successfully to devices. You can check the status of this by viewing the Device status for the policy as shown above.
If you now try and make a change to the registry on a device where the policy is deployed you will see the following message.
Techwerks 19

CIAOPS Techwerks returns to Melbourne CBD on Thursday the 18th of May.
The course is limited to 20 people and you can sign up and reserve your place now! You reserve a place by completing this form:
or by sending me an email (director@ciaops.com) expressing your interest.
The content of these all day face to face workshops is driven by the attendees. That means we cover exactly what people want to see and focus on doing hands on, real world scenarios. Attendees can vote on topics they’d like to see covered prior to the day and we continue to target exactly what the small group of attendees wants to see. Thus, this is an excellent way to get really deep into the technology and have all the questions you’ve been dying to know answered. Typically, the event produces a number of best practice take aways for each attendee. So far, the greatest votes are for deeper dives into the Microsoft Cloud including Microsoft 365, Azure, Intune, Defender for Endpoint, security such as Azure Sentinel and PowerShell configuration and scripts, with a focus on enabling the technology in SMB businesses.
Recent testimonial – “I just wanted to say a big thank you to Robert for the Brisbane Techworks day. It is such a good format with each attendee asking what matters them and the whole interactive nature of the day. So much better than death by PowerPoint.” – Mike H.
The cost to attend is:
Gold Enterprise Patron = Free
Gold Patron = $33 inc GST
Silver Patron = $99 inc GST
Bronze Patron = $176 inc GST
Non Patron = $399 inc GST
I hope to see you there.



































