A common complaint I hear about Office 365 from IT Professionals is that it doesn’t filter spam as well as other third party solutions. My immediate question at that point is always “Well, have you actually gone in and configured ANY of the spam settings in Office 365 to improve your results?” to which the answer is always No. Thus, if you don’t take the time to customise what you get out of the box you’ll only get an out of the box solution which is probably not what you want! Thus, some configuration is required for EVERY Office 365 tenant to improve its spam filtering abilities.
The out of the box spam settings for Office 365 are not configured in an aggressive manner and you should go in and make changes from the defaults I would suggest. Here’s how to do that.
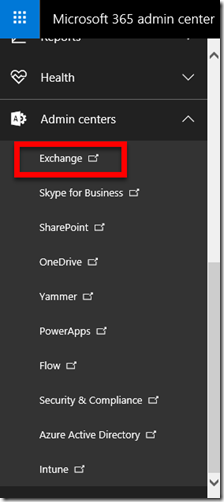
You’ll firstly need to login to the Office 365 portal as an administrator with rights to make changes. You’ll need to then navigate to the Office 365 Admin Center and select from the Admin centers on menu on the left hand side. You’ll find the Admin centers option right at the bottom.
From the list of options that now appear select Exchange as shown above.
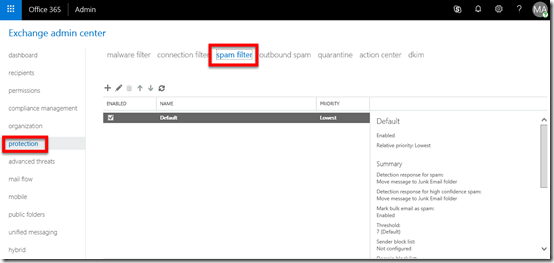
This will take you to the Exchange Admin center as shown above. In here select the protection option on the left and then spam filter on the right.
You will then typically see a single policy called Default.
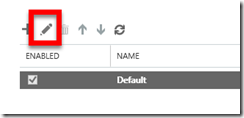
With this default policy selected, press the edit button (pencil) from the menu to view what settings this default policy has.
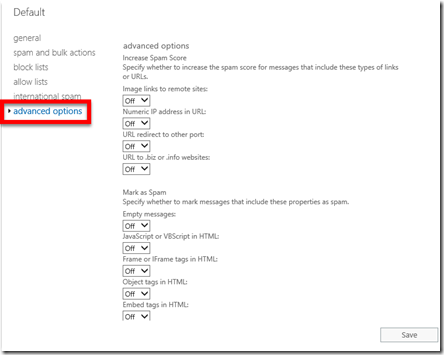
Select the different menu options on the left to view all the settings. Most you will see, like in the advanced settings shown above, are set to off.
You can of course edit this default policy, however it is better practice to go back to the list of policies and create a new one and leave the default one in place.
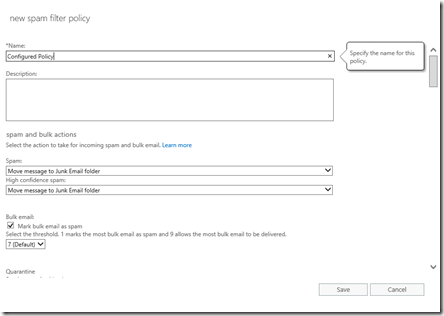
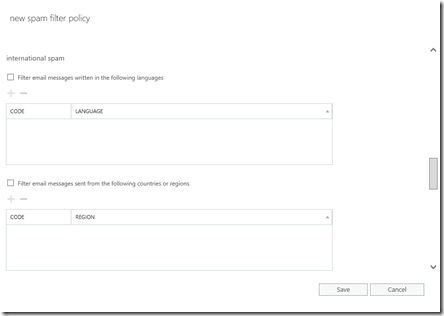
When you create a new policy using the plus button (+) a new dialog will appear like show above.
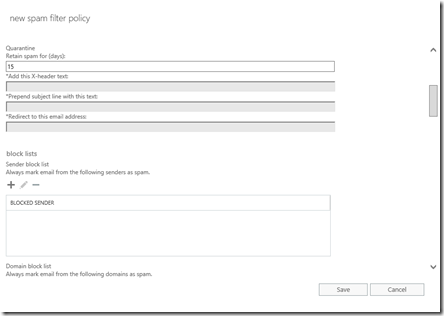
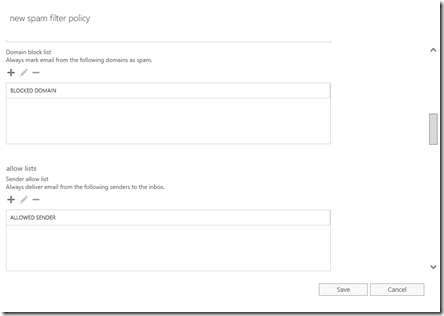
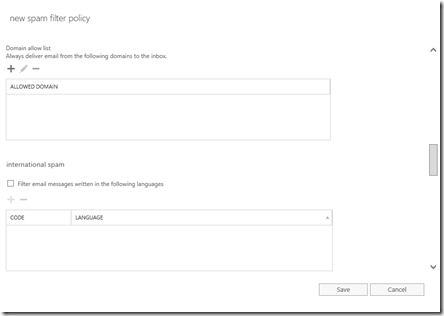
Give the new policy a name and now scroll through the settings to configure them for your needs.
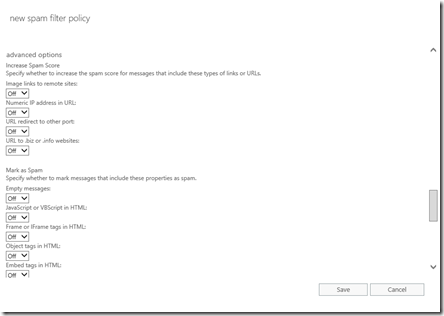
When you reach the advanced options towards the bottom you’ll see a number of options that can set on or off. The crowd sourced results I obtained for these were:
Image links to remote sites = OFF
Numeric IP addresses = ON
URL redirect to other port = ON
URL to .biz or .info websites = ON
Empty messages = ON
Javascript or VBScript in HTML = ON
Frame or iFrame tags in HTML = ON
Object tags in HTML = ON
Embed tags in HTML = ON
Form tags in HTML = ON
Web bugs in HTML = ON
Apply sensitive word list = ON
SPF record hard fail = ON
Conditional sender ID hard fail = ON
NDR backscatter = ON

You can then set whether the policy will simply run in test mode if you wish.
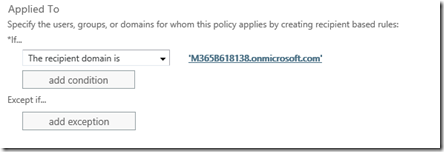
The final option is to determine where this policy will apply. Normally you want this across all your domains and users but as you see, you can have different policies for different users and domains if you wish.
All you now need to do is save the policy and start monitoring the results.
Hopefully, you can now see that out of the box Office 365 does take a very relaxed approached to spam which is not uncommon for most spam protection products. You can, and should, of course go in and configure the available options to be more restrictive. When you do this you will of course get much better results.
This post showed you how to make spam filter setting via the web interface, a much better and more consistent approach across many tenants is to do this using PowerShell. Look out for an upcoming article on this.
