Data Loss Prevention (DLP) is typically an outbound scanning technology in Office 365 that monitors and prevents sensitive information from leaving the organisation.

Previous, DLP was only part of Exchange Online. It is still possible to configure policies only in Exchange Online as you can see above, in the Exchange Online Admin console.
To do this in PowerShell you’d use the command:
new-dlppolicy
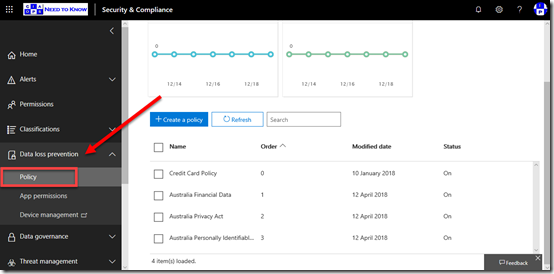
The new of way doing DLP in Office 365 is via the Security and Compliance Center as you see above. The benefits of using this new method is that it is possible to use policies to not only protect Exchange Online but SharePoint and OneDrive for Business from data leakage.

Office 365 DLP has a number of pre-canned policy templates you can use as shown above. It is always best practices to at least start with these since they cover the basics.
You’ll note above that I’m looking to configure a policy based on Australian Financial Data. This in effects scans material looking for SWIFT code, Australia Tax File Number, Australia Bank Account Number and Credit Card as you see in the lower right.

Proceeding with the GUI wizard then asks for the areas in Office 365 to protect. As you can see from the above, these locations include Exchange email, SharePoint sites and OneDrive accounts. You can modify the inclusion and exclusions to all these different areas if you wish.

You then determine what content you are looking for in the policy settings, as well as when to detect.

You can customise these rules if you wish, as shown above.

Finally, you can determine how this policy will operate and whether it is active.
Why is all this important for using PowerShell? The simple answer is, that with many options, knowing what everything does in the web interface is going to help when it comes to implementing via PowerShell.
So, to start the PowerShell configuration process you are going to need to connect to the Office 365 Security and Compliance center using PowerShell. You’ll find scripts to do that at my GitHub repo here:
https://github.com/directorcia/Office365
We don’t want to use the older, Exchange Online only cmdlets like:
new-dlppolicy
we’ll be using the newer Security and Compliance cmdlets like
new-dlpcompliancepolicy
The first thing I need to is create a new DLP policy called ‘Australian Privacy Act’ and do that with the commands:
$params = @{
‘Name’ = ‘Australian Privacy Act’;
‘ExchangeLocation’ =’All’;
‘OneDriveLocation’ = ‘All’;
‘SharePointLocation’ = ‘All’;
‘Mode’ = ‘Enable’
}
new-dlpcompliancepolicy @params
Now, this basically establishes the policy and the location that it applies to in Office 365. There are not any rules yet to check the content.
To do this. you need to create a variable that holds the sensitive data types you want to check. Yo can do that with the following:
$senstiveinfo = @(@{Name =”Australia Driver’s License Number”; minCount = “1”},@{Name =”Australia Passport Number”;minCount=”1″})
You’ll find information about the specific sensitive data types for you region here:
https://docs.microsoft.com/en-us/exchange/policy-and-compliance/data-loss-prevention/sensitive-information-types?view=exchserver-2019
With all that in place, the rule can be added to the existing policy using the following:
$Rulevalue = @{
‘Name’ = ‘Low volume of content detected Australia Privacy Act’;
‘Comment’ = “Helps detect the presence of information commonly considered to be subject to the privacy act in Australia, like driver’s license and passport number.”;
‘Policy’ = ‘Australian Privacy Act’;
‘ContentContainsSensitiveInformation’=$senstiveinfo;
‘BlockAccess’ = $true;
‘AccessScope’=’NotInOrganization’;
‘BlockAccessScope’=’All’;
‘Disabled’=$false;
‘GenerateAlert’=’SiteAdmin’;
‘GenerateIncidentReport’=’SiteAdmin’;
‘IncidentReportContent’=’All’;
‘NotifyAllowOverride’=’FalsePositive,WithJustification’;
‘NotifyUser’=’Owner’,’SiteAdmin’,’LastModifer’
}
New-dlpcompliancerule @rulevalue
You should recognise many of these settings from what is in the web interface. Don’t forget that DLP takes a while to crawl through all the different content areas you have selected and be applied.

If all of that executes successfully, then you should see a new DLP policy in the web interface as shown above.
If you have an Office 365 or Microsoft 365 licenses that includes DLP, you should use the pre-existing templates that Microsoft provides you for you region and create a new policy for each.
You can, of course, customise these easily by changing the PowerShell parameters or creating your own rules to suit. The great thing is, once you have worked all of this out you now a configuration you can apply to every tenant quickly and easily.
That is the power of automation thanks to PowerShell!


