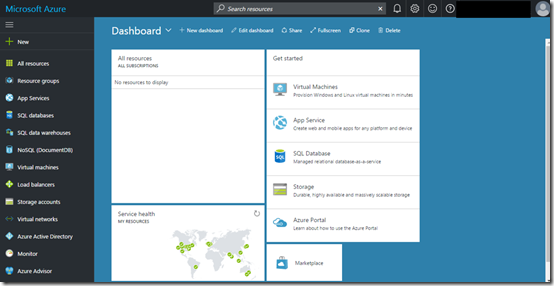
I was doing some shifting of domains and emails into Office 365 and came up against a few ‘unique’ issues I thought I’d share.
When I tried to move one domain into Office 365 I was told by the Office 365 DNS wizard that the domain was already in use by another Office 365 tenant! The message I received was:
domain.com was already added to a different Office 365 tenant domain.onmicrosoft.com.
Sign in to that account as an admin, and remove domain domain.com. Then come back here and try adding domain.com to this account again.
If you can’t sign in to domain.onmicrosoft.com as an admin, try resetting your admin password.
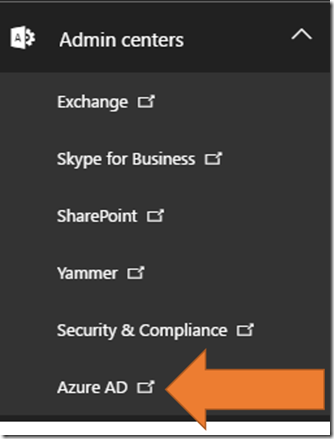
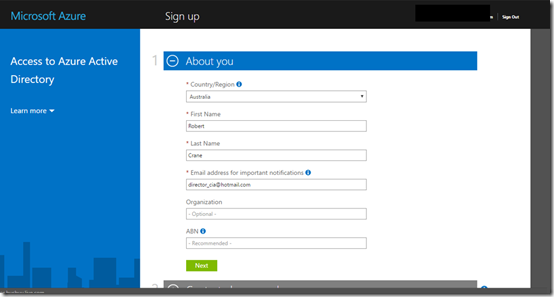
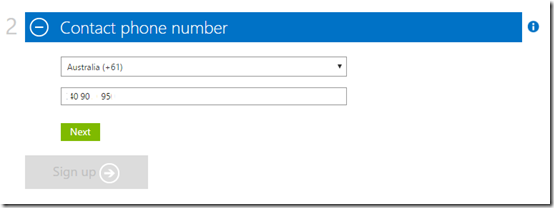
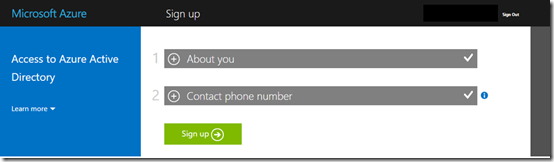
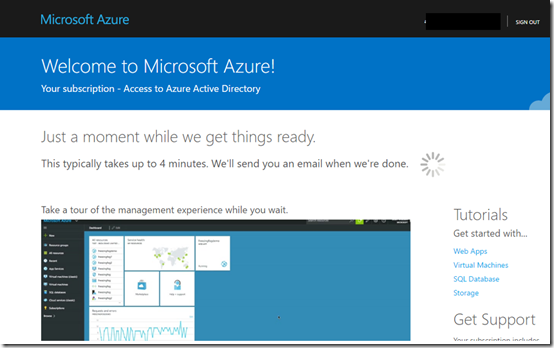
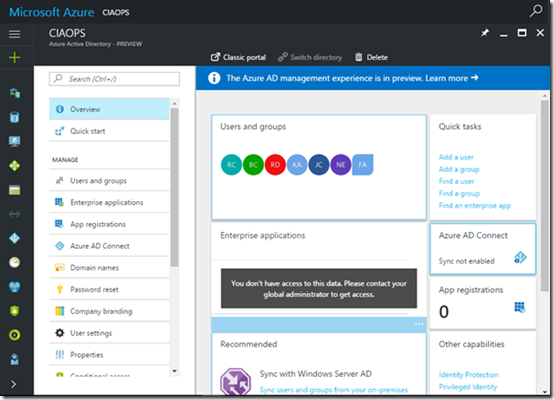
Say what?? How could this be I wondered? Then I remembered. I’d use that that email domain to send an Azure Rights Management document to. When the recipient attempted to open that document they were prompted to create a login in Azure Rights Management because the email account wasn’t already on Office 365. The login that they create for Rights Management is actually an Azure AD login. If it is the first time an email from this domain has logged into Rights Management then a new Azure AD tenant is established with this domain and the email address being the global administrator effectively.
This process of creating a ‘free’ Azure AD by a non-Office 365 email account is known as Azure Self Service signup and you can read more about what happens here:
What is Self-Service Signup for Azure?
Ok, so now I know how the domain came to already be associated with an Office 365 tenant but how the hell do I release it?
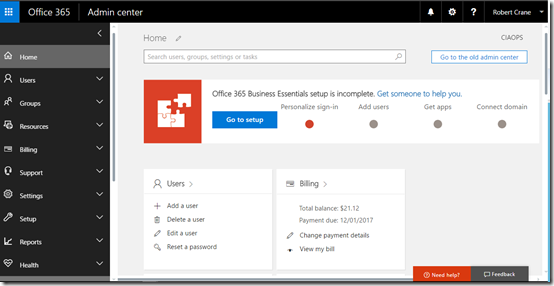
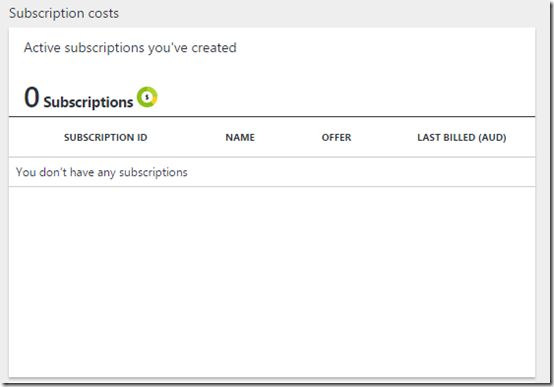
Luckily, I could remember the password for the Azure Rights Management user so I logged into the Office 365 console with that login. Sure enough, there was the custom domain. Easy enough to remove right? Not quite.
When I attempt to remove the custom domain from this tenant I get prompted that it is already in use by a user. Ok, ok. So I go back to the only user in the tenant (the one that set all this up for Azure Rights Management) and I swap the primary login back to domain.onmicrosoft.com. Good to go right?
Again, no so fast. Now I get, when trying to remove the domain, that the domain is as an alias or used with Skype. Hmm.. as this tenant has effectively no mailbox or Skype licences how do I check or change these?
PowerShell to the rescue! I use the script from the bottom of this post (thanks Bittitan):
https://community.bittitan.com/kb/Pages/How%20do%20I%20remove%20a%20domain%20from%20Office%20365.aspx
to quickly remove every alias that ends in domain.com.
Phew, now I can finally remove the domain from the ‘free’ Azure AD Rights Management tenant.
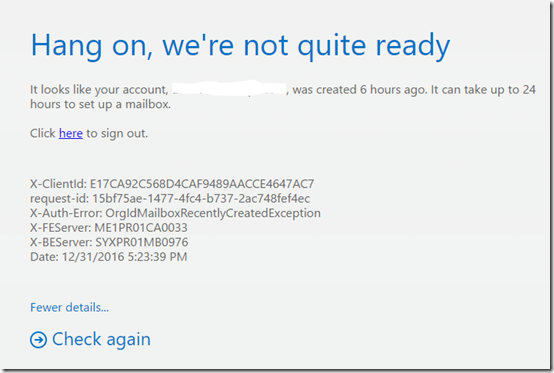
I now go through the normal process of adding the custom domain back into tenant with the Office 365 licenses I’m trying to build. All good so far. Now I license and create a user. Still all good. However, when I visit the new users mailbox on the web I’m greeted with a message like:
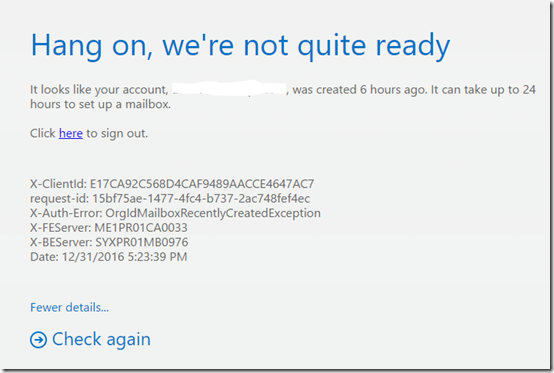
Hang on, we’re not quite ready
It looks like your account, user@domain.com, was created 1 hour ago. It can take up to 24 hours to set up a mailbox.
Click here to sign out.
X-Clientld: 2040134E67C145408AAEA2B206CE6183
request-id: ab7e2c74-b653-4f79-96d9-a5bca84f3a75
X-Auth-Error: OrgIdMaiIboxRecentlyCreatedException
X-FEServer: ME 1 PR01CA0033
X-BEServer: SYXPROI MB0976
Date: 12/31/2016 AM
Fewer details…
Check again
Hmmm..not good. Now I start wondering what’s going to happen to the inbound mail to this mailbox? I’ve shifted the DNS records so it will be flowing into the tenant, but will it end up in the mailbox? Lost? Or just be bounced? The unknown is freaking me out.
So I go into the Office 365 Administration area and check the user details and license. All good. I see that the mailbox exists in the Exchange admin area. All good. I turn on archiving for this mailbox and it works, however when I return to the mailbox on the web, same please wait message.
After about 10 minutes of clicking the Check again link I decided that a watched kettle never boils and I go away to do other things.
An hour later I return and get the same result when I try again. However, when I go into the usage statistics of the mailbox in I see that it actually has a small amount of data in it now. I assume this is inbound mail. My assumption is thus, that the mailbox is in fact accumulating inbound email even if I can’t get to it. A small ray of sunshine appears in the clouds of despair.
I also try and connect up a local version of Outlook 2016 to the mailbox, but no joy there either.
I then consider logging a support call via the portal, however when I attempt to do this the only option I’m given is for a phone call back. For some reason there is no email option?? Not wanting to inflict my impatience on others and risk being told to wait the period the message says in plain English in front of my eyes (i.e. the bleeding obvious), I defer logging a support call to further down the track, beyond the 24 hour period (but not a second beyond that!).
Deciding that the best thing is to do what the screen says and wait up to 24 hours and see if it sorts itself out, I head off to other distractions. That however doesn’t prevent me from checking the mailbox at the 3, 6 and 9 hour mark, all with the same result. Damm, this is not looking good!
At the 10 hour mark I try the mailbox again on the web and it looks like it is going to open (I get the ‘preparing Outlook’ screen) but alas same result. However, when I try to connect to the mailbox using my local version of Outlook now I get a connection and can see new emails! Yeah! Things are looking up. Thank you spirit of 2017.
With desktop Outlook connecting to my mailbox I begin to import the emails saved from the previous hosting configuration via PST. Although slow, the process is working. I now check the usage size of this mailbox and it is increasing. So two pluses there. A few minutes later I can now access the mailbox via the web browser. Halleluiah, technology be praised. Never doubted it for a second (rrrrrrright…..).
Thus, long story short. If you are moving an existing account from one Office 365 tenant to another (even if the original doesn’t have a mailbox) beware you may get the delay message shown previously when attempting to access the mailbox. Importantly if you do, don’t panic. Just wait it out. In my case it took 10 hours to come right, but like the message on the screen actually says, it could take up to 24 hours. However, if you check the usage of the mailbox in question and it is increasing, this would indicate that the mailbox is working an receiving emails and provide solace during your extended waiting period.
As they say, patience is a virtue and a virtue I am still perhaps yet to fully learn!